Best Email Security Solutions Compared 2026
As email moves to the cloud, organizations must rethink their email security strategies. We take a closer look at the best email security solutions on the market today.
The COVID-19 pandemic and the rise of cloud computing have had a significant impact on how modern companies do business. Remote work pushed many companies to accelerate their adoption of cloud-based solutions, identifying cloud-based solutions to support a distributed workforce.
One of the most widely-used Software as a Service (SaaS) solutions is cloud-based email. However, as email moves from on-prem email servers to the cloud, organizations must rethink their email security strategies.
The Need for Email Security
Email is one of the most common attack vectors for malware delivery, data exfiltration, and other cyber threats. Email security is a vital component of an enterprise cybersecurity strategy. When email was on-premises, Secure Email Gateways (SEG) made sense, and efficiently and effectively protected corporate email. However, due to the “new normal”, email moved to the cloud at an accelerated rate.
The shift to cloud-based webmail is forcing companies reliant on legacy email gateway architectures to adapt. In 2021, the market size of email security solutions was $3.65 billion with a CAGR of 14.4%.
How to Choose an Email Security Company?
For an email security solution to identify and block email-based threats, emails must be routed through the email gateway. This creates challenges for legacy email gateway vendors that designed their solutions with on-prem email servers in mind. In contrast, other solutions are designed for cloud-based email and distributed enterprise.
One of the primary differences between legacy on-prem and cloud-based email solutions is how they direct traffic to the email gateway. The two main approaches are via MX records and application programming interfaces (APIs).
The MX Record Approach
An MX record is part of the DNS record associated with a particular domain. The purpose of the MX record is to identify the IP address of the domain’s email server or mail transfer agent, enabling inbound emails to be routed to that server.
When deploying a legacy SEG, an organization must change its MX records to point to the IP address of that gateway. This enables emails to be routed through the gateway but has significant downsides, including:
- Complexity and Disruption: An MX record approach to email routing requires reconfiguration of an organization’s DNS records and makes significant changes to email routes. This is a very invasive and disruptive approach to deploying a security solution.
- Open Source Intelligence (OSINT): DNS records are designed to be public knowledge, enabling anyone to send an email to a domain. Updating an MX record publicizes the email security solution that an organization uses. This allows attackers to customize their attacks to exploit any known flaws or limitations in the email security solution.
- Limited Visibility: Modifying MX records only reroutes incoming email from outside the domain, meaning that an SEG is blind to internal email traffic. Since internal threats make up 35% of attacks, this leaves an organization exposed to over a third of attacks.
API-Based Solution
SEGs need to rewrite MX records because they lack the ability to directly integrate with email solutions. As a result, they need to reroute email to pass through them on the way to the email solution to provide security.
However, many modern email solutions expose APIs designed to allow a third-party service provider to query and manage a user’s delivered email. This provides the ability to implement email security within the corporate email platform rather than as a standalone solution reliant on intercepting emails en route.
How Does API Replace MX Records?
Some cloud-based email providers offer API access to emails within an account. For example, Microsoft 365 includes the Microsoft Graph API, which allows a third-party service to query the emails delivered to the customer. This API can be set up quickly and easily via OAuth authentication.
Using Microsoft Graph API and similar API-based solutions, it is possible for a third-party provider to offer the following services:
- Anti Spam
- Anti Malware
- Anti Phishing
- URL Filtering
An email security solution that uses API-based integration can be far more effective than an MX record-based approach. For example, Check Point Workspace Security Email is 44x more effective at keeping phishing emails from reaching a user’s inbox than legacy email gateways using MX record approaches.
Email Security Vendors Compared
An organization can implement email security with various solutions. Some of the major email security companies in the space include Check Point, Proofpoint, Mimecast, and cloud email providers such as Google and Microsoft. These solutions take different approaches to email security and provide different feature sets, resulting in varying levels of effectiveness at email protection.
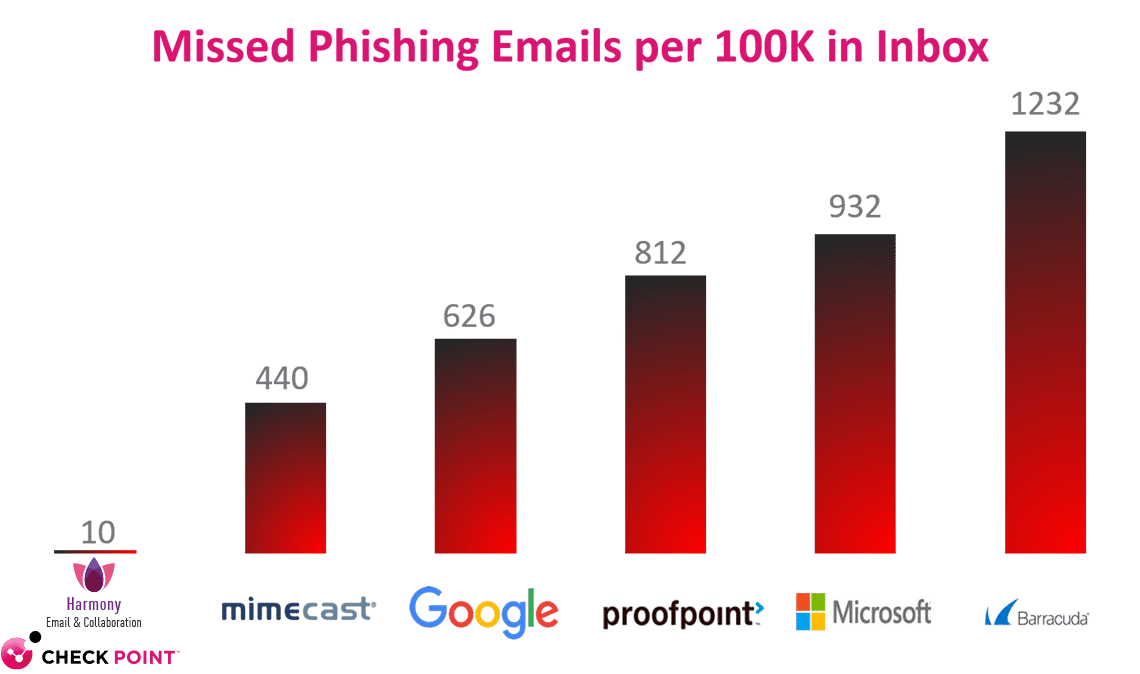
44x more effective than legacy gateway approaches like Proofpoint, Mimecast, and Barracuda
93x more effective than Microsoft

Check Point
The Check Point Check Point Email Security suite provides email security protection for Microsoft 365, Google Workspace, and other collaboration and file-sharing applications. Some of the main benefits of Workspace Security include:
- Advanced Email Security: Provides protection against advanced phishing, malware, and ransomware attacks. Threats are blocked before they reach the inbox across inbound, outbound, and internal email communications in real-time.
- Data Loss Prevention (DLP): Identifies and blocks sensitive data from leaving the organization via email and other online collaboration apps.
- Account Security: Identifies and blocks attempted account takeover attacks, keeping users and the organization safe.
- Cross-Platform Support: Many organizations have expanded their online collaboration toolsets, adding apps like Slack and Teams. Check Point’s Check Point Email Security suite provides protection across all collaboration platforms.
- Technological Leadership: Workspace Security is the first solution to implement API-based integration, machine learning (ML), and artificial intelligence (AI) for email security.

Proofpoint Essentials
Proofpoint Essentials is Proofpoint’s basic email security offering, which includes support for cloud-based email platforms such as Microsoft 365. Some limitations of Proofpoint Essentials include:
- MX-Based Routing: Proofpoint Essentials customers must change their MX DNS record to point to their email gateway. This invasive and disruptive approach to email routing informs attackers that the organization is using Proofpoint Essentials, enabling them to tailor their attacks.
- No Sandbox: Sandboxed evaluation is essential to identifying novel malware within email attachments. This is not available within the Essentials package, making it necessary to upgrade to a more expensive package to add protection against zero-day threats.
- No Content Disarm and Reconstruction (CDR): CDR dissects a file, excises malicious content, and rebuilds it before sending the sanitized file on to the recipient. Without CDR, Proofpoint Essentials users must wait to receive clean files.
- Email-Only Protection: Proofpoint Essentials requires a separate cloud application security broker (CASB) solution to protect SaaS applications. This requires additional cost and overhead.
- Single Line of Defense: Deploying Proofpoint Essentials requires disabling security features built into Microsoft 365, such as spam filtering. This increases the probability that malicious emails will reach users’ inboxes.
- Incomplete Protection: Proofpoint’s URL protection is vulnerable to bypass by malformed URLs. This allows emails pointing to phishing pages to reach users’ inboxes.
![]()
Mimecast M2
Mimecast M2 is an email security solution based on traditional gateway approaches to email security. Some of the shortcomings of Mimecast M2 email security include:
- MX-Based Routing: Mimecast M2 forces customers to modify their MX records to direct email through the secure email gateway. This is disruptive, invasive, and provides attackers with valuable intelligence for tailoring their attacks.
- Anomaly-Based Detection: Mimecast M2 relies on basic anomaly detection to analyze email contents with no dynamic analysis.
- Limited Sandboxing: Mimecast M2’s sandbox is incapable of catching advanced evasion techniques.
- Static Social Engineering Protection: Mimecast M2 only uses static dictionary matching to identify impersonation in phishing emails. This provides less protection than real-time analysis.
- MTA-Based Deployment: Email protection can only be deployed using MTA. This requires disabling built-in security features in Microsoft 365, reducing overall security.
- Manual DLP Definitions: Administrators must manually define data types for DLP. This is complex, time-consuming, and runs the risk that an oversight will result in the leakage of sensitive information.


Native Vendors Security (Microsoft and Google)
Cloud email providers like Microsoft and Google provide integrated email security features for their users. However, these solutions have their limitations, such as:
- Less Comprehensive Coverage: Microsoft and Google specialize in cloud email hosting, not email security. As a result, their email security solutions are less comprehensive than a dedicated email security solution.
- Platform-Focused: Integrated email security features are designed to protect emails on their own platforms. Emails routed outside the platform are not protected
Microsoft Exchange Online Protection (EOP) is included with all Microsoft O365 packages, while Defender Plan 1 & 2 are add-ons. However, all of these solutions have the following shortcomings:
- Limited Sandbox Detection: Built-in sandboxing does not have the ability to detect advanced evasion techniques used by modern attacks.
- File Preview: Microsoft’s Dynamic Delivery provides a risk-free preview of files but not permanent access to a risk-free document created via CD&R.
- Limited Safe Links Coverage: Safe Links does not provide protection within files or inside Dynamic Delivery. Additionally, it creates latency when users attempt to access legitimate sites.
- Poor User Experience: Complex policy controls, limited information on incidents, multiple management views, and limited forensics capabilities on files identified to be malicious all lead to additional resource usage and labor hours for forensics.
- Malformed URL Bypass: Safe Links protection can be bypassed by deliberately malformed URLs. This allows emails with links pointing to phishing sites to reach a user’s inbox.
Email Security with Check Point
Check Point’s Workspace Security Email & Collaboration suite (previously Avanan) is a cloud-native solution that delivers security via API with internal context and advanced machine learning to stop the most pernicious attacks. Unlike other API solutions, Workspace Security is the only one on the market that acts as a full-fledged, standalone email security solution. Workspace Security detects and stops the evasive attacks that bypass Microsoft security and that other email security solutions miss.
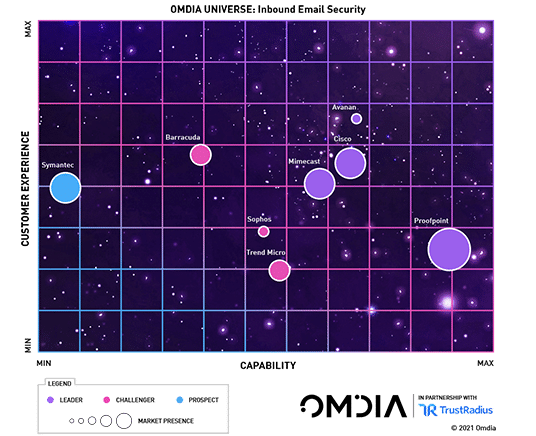
Explore the advantages of API-based email security solutions in this report by Gartner. Then, learn about how to select an email security solution in this Omdia report.
Selecting the Right Email Security Vendor
A Email Security solution must include certain key features to provide effective protection to an organization.
Here is a summary of the main points:



(extortion / payments / impersonation)
(sandbox + CDR)
(AV / spam / reputation)
(Includes: Slack / Citrix / Outlook / Sharpoint, Onedrive / Teams / Gsuite / Box / Dropbox / GoogleDrive)
Global Chemical Manufacturer Grace Secures Cloud Digital Transformation with Check Point Workspace Security Solutions
“Grace has deployed Office 365 cloud based email solution…. We were experiencing significant phishing attacks; within three months we were in trouble. We turned to our trusted partner Check Point and deployed Workspace Security Email & Office. Within an hour we had the product up and running. Within the second hour we had it properly tuned and it was catching emails immediately…”
– David Antlitz, Global Manager, Security and Firewall Technologies, Grace
Gimv secures critical investment data with Check Point Workspace Security
“We exchange a lot of sensitive data, through a lot of emails…. Data security is critical. It’s not a question of ‘if’ you’re being attacked, it’s ‘when’… We had another provider, but Check Point was the first to introduce a threat emulation feature... It’s a ‘set and forget’ solution, it gives end users the confidence to know that the mail in their mailbox has already passed security checks and is secure”
– Kristof Poppe, IT Manager, Gimv
Canal Bank Secures Email with Check Point Workspace Security Email & Office
Cloud technology plays an important role in Canal Bank’s strategy… Canal Bank chose Workspace Security Email & Office, a cloud service that is built specifically to fight cloud email and productivity suite threats… “We have been using Workspace Security Email & Office for the last year, and during that time we have stopped approximately 1400 phishing attacks”… “The solution also defended us from about 800 malware attacks… Check Point also provides reports that give me thorough visibility into threats targeting our email platform.”



