Top 4 Next-Generation Firewalls (NGFWs) Compared
Next-generation firewalls (NGFWs) act as an organization’s first line of defense against cyber threats. They inspect and filter all traffic entering and leaving the enterprise network to block attempted malware infections and data exfiltration.
Below, we discuss some of the key features that a truly effective NGFW should offer, and then compare the top NGFW vendors.

The Need for a Strong Next-Generation Firewall (NGFW)
NGFWs have always been a vital component of an organization’s security architecture, but the need for them has only increased in recent years. Several high-profile security incidents – such as SolarWinds, Microsoft Exchange Server, and Colonial Pipeline hacks – have demonstrated the increasing sophistication of cyber threat actors.
Additionally, the sudden shift to remote work and cloud computing due to the COVID-19 pandemic has caused significant changes in organizations’ IT infrastructures.
With these changes come new security challenges and exposure to cyber threats. In the modern world, the question of whether an organization will be targeted by a cyberattack is not one of “if” but “when”.
Therefore, companies need top-tier security solutions to prevent and block attempted cyberattacks, and a strong NGFW is the cornerstone of any cybersecurity deployment. When attempting to choose between NGFW vendors, it can be difficult to identify the criteria to base decisions on.
Jump directly to the sections below:
The Key factors
Comparing the top vendors
Select the right Vendor
Key Factors to Consider When Choosing a NGFW
Real-Time Prevention
Many classical security solutions are designed to detect cybersecurity incidents, enabling the organization to respond. However, this approach to security means that organizations only react to threats after the attacker has access and starts achieving their goals and doing damage to the organization. A better approach to security focuses on prevention, blocking malware and other threats before they enter the network. By blocking the infection of “patient zero,” a NGFW with real-time prevention eliminates risk, damage, and cost to the organization.
![]()
![]()
Identification and Identity Management
Robust identification and identity management are essential to effective cybersecurity. Without the ability to differentiate legitimate users, applications, and devices from illegitimate ones, it is impossible to accurately detect and block intrusions into the network. Effective identification requires full visibility into entities inside an organization’s environment regardless of location and platform (on-prem, cloud, mobile, endpoints, or IoT devices). Compromised credentials are a leading target of cybercriminals and cause of security incidents. Organizations should select NGFWs that provide robust identification and access control for the distributed workforce.
Inspection within SSL/TLS
The SSL/TLS protocol improves the privacy and security of traffic by wrapping network communications in a layer of encryption and applying robust authentication. While this is a major benefit for data security, cyber threat actors also use SSL/TLS to conceal their activities on the network.
In Q1 2021, 46% of malware used TLS to hide their communications from security solutions. The ability to perform SSL/TLS introspection is crucial for a NGFW. Without the ability to unwrap the encryption around network traffic, an organization is blind to the traffic on their networks and cannot effectively detect malware delivery or data exfiltration. A NGFW should be able to perform SSL/TLS introspection with minimal network latency to balance the needs of network security and performance.
![]()
![]()
Going Beyond Signature-Based Defenses
In the past, cybersecurity tools have relied upon signature-based detection to identify malware and other cyberattacks. By comparing content to pre-defined signatures, these solutions can identify known malware variants with high accuracy.
Today, signature-based detection misses 70% of malware attacks. A NGFW must go beyond signature-based detection to use technologies capable of detecting and remediating novel and zero-day threats, including:
- Sandboxing (including static, dynamic, and behavioral analysis)
- Content disarm and reconstruction (CDR) to sanitize documents
- Artificial intelligence and machine learning
- Comprehensive threat intelligence
Zero-Trust Approach
Historically, organizations have used a perimeter-focused approach to security. By deploying security solutions at the network perimeter, they attempted to keep threats outside the network while allowing “trusted” parties full access to the internal network.
Now, network perimeters are dissolving, insider threats are a growing challenge, and cyber threat actors are more adept at breaking through perimeter-based defenses. Zero trust security addresses these challenges by providing access and permissions on a case-by-case basis. Permissions are assigned based on least privilege, which grants a user, device, or application only the permissions that are needed to do its job.
NGFWs should be designed to enforce zero trust principles. This can include going beyond implementing strong access control to include advanced intrusion prevention systems (IPSs) and web application firewalls (WAFs) to protect applications against exploitation.
![]()
![]()
Shared Threat Intelligence
HIgh-quality threat intelligence is vital to effective threat prevention, detection, and response. This data provides insight into current attack campaigns and the activities of threat actors, enabling organizations to identify attempted intrusions into their networks.
However, threat intelligence is only of value if it is available to the solutions that need it to detect potential threats. NGFWs should be able to share threat intelligence with the rest of an organization’s security infrastructure to provide comprehensive visibility and coordinated threat management.
Unified Management Configuration
Most organizations’ security architectures are built of dozens of standalone point security solutions. This means that security teams must learn to use a variety of different dashboards and navigate a complex security architecture. This inefficient workflow slows threat detection and response, increasing the potential cost and damage to the organization.
An effective NGFW enables an organization to simplify its security architecture through consolidation. By integrating multiple different solutions behind a single dashboard, security teams are able to more quickly respond to potential threats across the entire organization.
However, security consolidation is not enough for efficiency. It is essential that the user interface is intuitive and enables security administrators to complete tasks with minimal efforts. To learn more about the management and menu complexity of various NGFW solutions, check out the agony meter.
![]()
Security from the Start
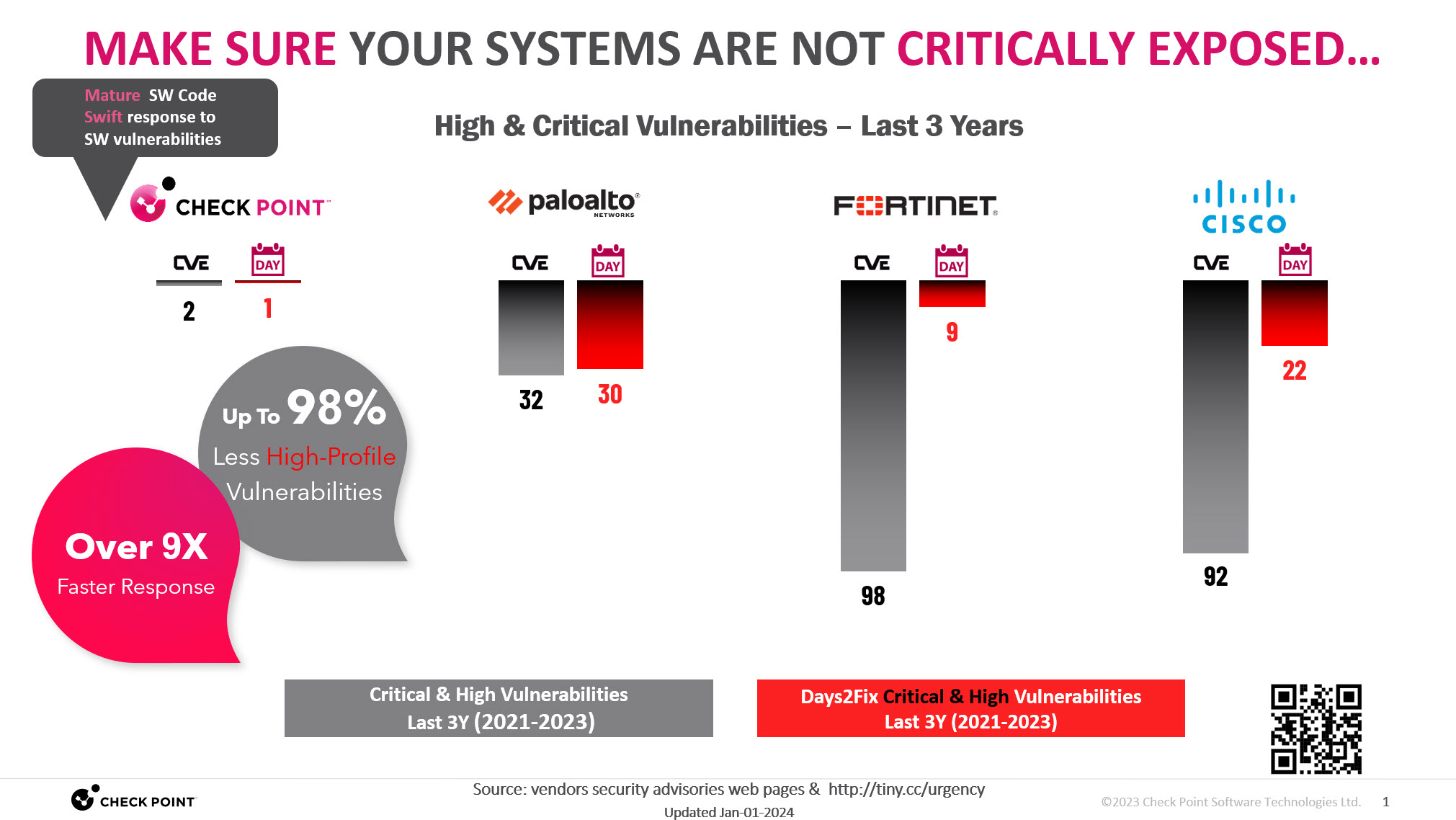
All software have bugs. However, there is a big difference between having a few bugs and software that has a large number of exploitable vulnerabilities. Each vulnerability that reaches production code creates a window between the initial discovery of the bug and the application of a vendor-provided patch that an attacker can exploit.
When looking for a NGFW solution, it is important to take a look at the history of vulnerabilities in the product. If a NGFW is prone to large numbers of exploitable vulnerabilities, it can undermine the security of the entire organization.
Comparing the Top NGFW Vendors
A number of different vendors offer NGFW solutions. However, four vendors stand out from the rest. When choosing between Check Point, Fortinet, Palo Alto Networks, and Cisco, keep the following pros and cons in mind.

Check Point is the industry leader in NGFWs with 22 years of recognition by Gartner as a Leader in the space. Some of the features that differentiate Check Point NGFWs from other vendors include:
- Best Operational Efficiency: Check Point Security Management is the industry’s most integrated and robust platform managing security at all sizes.
- Proven and Most Consistent Track Record: Check Point has been a leader in network security since 1997.
- Security Comes First: Check Point builds & develops its security solution securely – right from the start.
- Best Prevention: Real-time threat prevention is a core philosophy of Check Point solutions.
- Best-in-class Hyperscale Platform: Check Point’s hyperscale solutions enable growth with the best ROI in the industry.
![]()
Fortinet shows attractiveness with high performance at low cost, but when it comes to NGFW it is not always the case. Furthermore, it shows more complexity managing it with more management complexity. Fortinet solutions have significant shortcomings, including:
- Perception Gap: Hardware-based Forti-ASIC acceleration is limited to firewall traffic only. Next-Gen advanced security engines lack the same acceleration, creating significant performance degradation.
- SMB Oriented: Limited capabilities with enterprise-grade requirements when it comes to managing complex environments.
- Vulnerable Solutions: 98 High & Critical vulnerabilities have been discovered in Fortinet products between 2021-2023 (read FBI & CISA warning), leaving customers exposed.
![]()
Palo Alto Networks (PAN) offers a middle-of-the-road NGFW by cutting corners with security, in some cases preferring performance over security. It has an unacceptable number of vulnerabilities on its own security products (read swarm of PAN-OS vulnerabilities). In many cases, it is more complex than competing vendors.
The main shortcomings of PAN NGFWs include:
- Response-Focused: With advanced threats, Palo Alto Networks does not offer real-time prevention but focuses on detection and remediation after the fact.
- High Agony Managing Security in low Efficiency: PAN solutions offer limited and complex operational efficiency, especially in large environments.
- Limited Visibility: PAN solutions provide low visibility into high-risk applications.
- Vulnerable Solutions: 32 High & Critical vulnerabilities have been discovered in PAN products between 2021-2023 (read swarm of PAN-OS vulnerabilities & NSA advisory warning).
- Cutting Corners: Palo Alto Networks is using security shortcuts that can lead to breaches. Watch this video

Cisco offers the most complex NGFW solution of the four leading vendors. This contributes to a number of issues, including:
- Response-Focused: Cisco solutions do not offer prevention of advanced threats. Instead, they detect these threats and support remediation after the fact.
- Lack of Security Unification: Cisco solutions are not unified and use different components for different purposes. For example, Cisco Adaptive Security Appliances (ASAs) implement firewalls, Firepower offers threat prevention, and Secure Web Gateway (SWG) provides web protection for web applications. Each of these solutions requires its own user Management, unique policies and logs.
- Complex Management: Day-to-day administrative security tasks are extremely complicated, time-consuming, and error-prone.
- Vulnerable Solutions: 92 Vulnerabilities have been reported in Cisco products between 2021-2023.
Selecting the Right NGFW Vendor
A NGFW must include certain key features to provide effective protection to an organization. To learn more about what you should be looking for in a NGFW, check out the Buyer’s Guide to Cybersecurity.
(apps/users/devices)
coverage
coverage
coverage
management
35 menus and significantly more time for same task
22 menus and significantly more time for same task
38 menus and significantly more time for same task
Vulnerabilities on vendors’ own security products 2020-2023 (lower is better)
at start
162 vulnerabilities
at start
339 vulnerabilities at start
357 vulnerabilities at start
Check Point NGFWs are the only solution that provides all of the key capabilities of NGFWs, and they also offer greater functionality, higher usability, and better security than competing solutions. Check Point offers best-in-class security by building its solution security first. It also offers unique capabilities that are essential for preventing and remediating today’s and tomorrow’s advanced attacks.
Check Point is a long-lasting Gartner leader for 21 years now and will continue to innovate and lead the cybersecurity landscape. To see Check Point NGFWs in action, request a demo with one of our security experts.
Network Security Through the Voice of the Customer
Our Customers Love Us
Versatile Security Protection –Like A Swiss Army Knife For Security
Checkpoint Next Generation Firewall proves to be a great solution for our small business infrastructure. R80 Security Management has allowed our company to easily (and significantly) improve our protections over time. read more >
CheckPoint Next Gen FW, The Best Way To Protect A Corporation Against The Latest Threats
Our experience with CheckPoint has been very satisfactory for the advanced security approach, being able to provide our corporation with the latest generation security mechanisms and being able to have maximum control and visibility of our perimeter security. read more >
Apple In The World Of Firewalls
The Check Point Next Generation Firewall is like Apple in the world of Firewall and Security. It is an old, but still modern and competitive solution, and Check Point is always on the edge of security technologies. read more >