Protecting Against a Rapidly Spreading Cyber Pandemic
With the Covid-19 outbreak, cyber criminals have seized this global crisis to launch treacherous cyber exploits. The new normal landscape has generated a surge of sophisticated Gen V cyber attacks, including targeted ransomware. The Cyber Pandemic is here. Now is the time to pull out all the stops and take action to protect your organization.
For more information on how to stay protected from the Log4J vulnerability CLICK HERE
![]()
Remote Work
Ensuring employees have secure access to corporate resources
![]()
Collaboration Tools
Replacing face-to-face activities with reliable virtual tools
![]()
Digital Transformation
and Cloud
Accelerating the pace to trusted digitally connected services
Cyber Pandemic Update
Protect yourself against the
Apache Log4j 0-Day vulnerability
One of the most serious vulnerabilities on the internet in recent years.
When we discussed the Cyber pandemic, this is exactly what we meant – quickly spreading devastating attacks.
Learn how to stay protected with Check Point real-time threat prevention protections
READ MORE
Video Guide: How To Secure Your Remote Workforce
From recent attack trends to best practices for mobile, endpoint and cloud email security, our 8-part video guide is everything security admins need to secure the remote workforce in the new normal, and beyond.
WATCH NOWTopics of Interest
- Best Practices to Stay Safe in a Cyber Pandemic
- Your New Cyber Security Normal
- Cyber Security in the Age of Coronavirus (Video)
- Coronavirus Related Attacks Reach 200,000 Weekly
- Hackers Set Return-to-Work Traps
- Threat Actors Join in the Race Towards a Coronavirus Vaccine
- Security Concerns Over Contact Tracing Apps
- Fixing the Zoom ‘Vanity Clause’
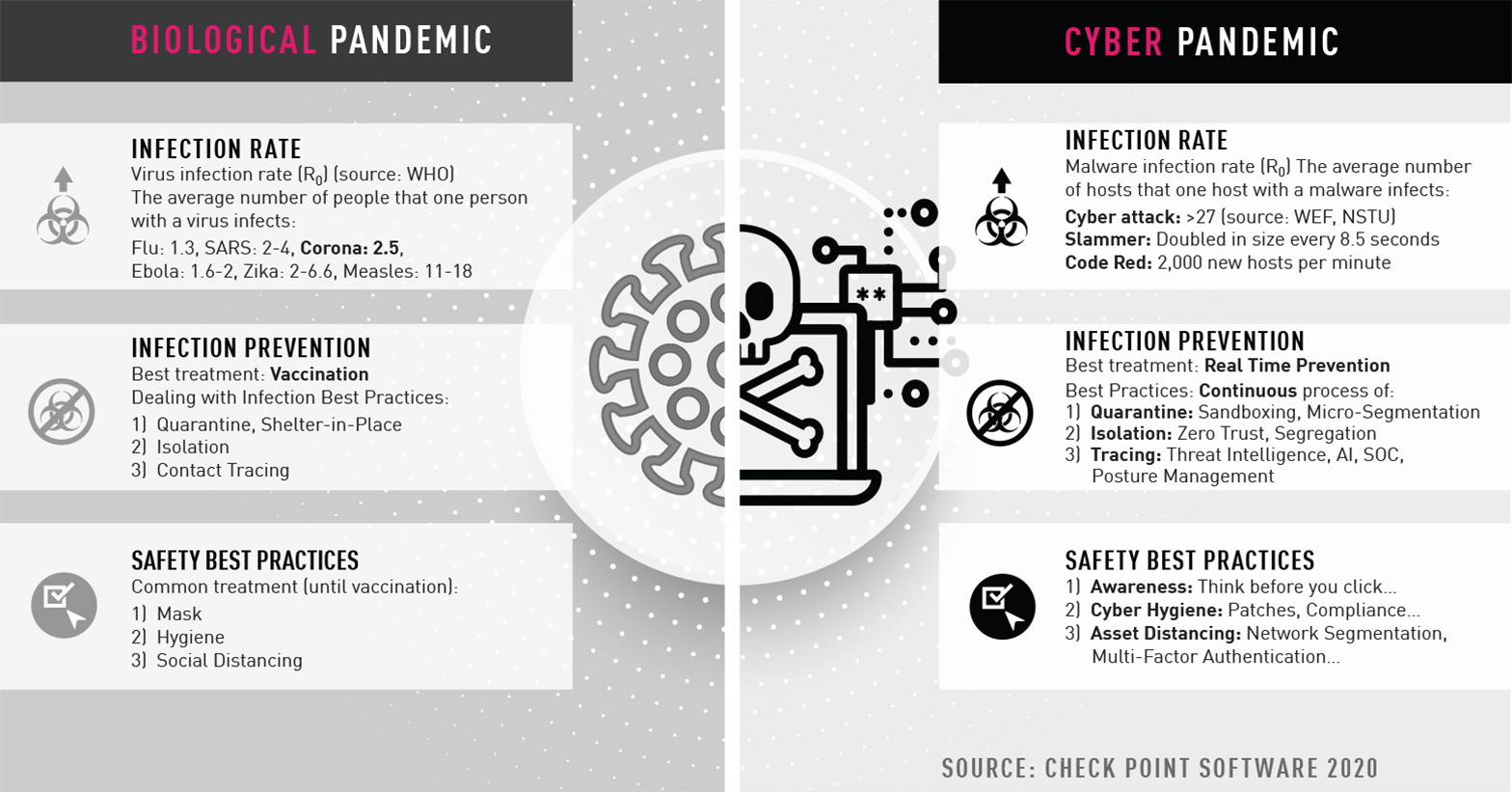
- Biological Pandemic vs. Cyber Pandemic: Similarities and Parallelization, Lessons Learned
- Moving Beyond Coronavirus onto Safer Ground
- Coronavirus Impact: Cyber Criminals Target Zoom Domains
- Protection from Hackers and Phishing Attempts
- Coronavirus Impact: As Retailers Close their Doors, Hackers Open for Business
>> Technical Resources
>> Check Point and Partners Give Back
>> Previous “Topics of Interest”
Best Practices to Stay Safe in a Cyber Pandemic

REAL-TIME PREVENTION
As we‘ve learned, vaccination is far better than treatment. The same applies to your cyber security. Real time prevention places your organization in a better position to defend against the next cyber pandemic.
SECURE YOUR EVERYTHING
Every part in the chain matters. Your new normal requires that you revisit and check the security level and relevance of your network’s infrastructures, processes, compliance of connected mobile, endpoint devices, and IoT.
The increased use of the cloud means an increased level of security, especially in technologies that secure workloads, containers, and serverless applications on multi- and hybrid-cloud environments.
CONSOLIDATION AND VISIBILITY
Dramatic changes in your company’s infrastructure presents a unique opportunity to assess your security investments. Are you really getting what you need and are your point solution protecting the right things? Are there areas you’ve overlooked?
The highest level of visibility, reached through consolidation, will guarantee you the security effectiveness needed to prevent sophisticated cyber attacks. Unified management and risk visibility fill out your security architecture. This can be achieved by reducing your point product solutions and vendors, and your overall costs.
Your New Cyber Security Normal
With a cyber pandemic, your cyber security demands that you understand the cyber risks with your changed computing environment. The matrix below provides a starting point as you re-assess your cyber security strategies.
| Change | Effect | Risk | Top Process & Technology |
|---|---|---|---|
| Working from home | Personal mobile and computers provided access to corporate networks | Data breach (e.g. key logger, screen logger on pc/mobile) | 1. Implementation of endpoint security and hygiene with compliance check (latest patches, AV…) 2. User training awareness (e.g. phishing simulation) 3. Mobile threat defense on mobile |
| Rapid move to cloud » |
Speed of deployment on the expense of security | Basic security controls can lead to data loss and manipulation | 1. Invest in Cloud Security posture management 2. Deploy workload security for containers and serverless apps. 3. Real time prevention of threats with IaaS security |
| Critical infrastructure » | Allowing critical infrastructure remote access | Critical infrastructure breach | 1. IoT security for IoT devices 2. bolster network security posture with red team … 3. OT security with Scada enforcement |
| Increased network capacity | More throughput is needed to address data in motion | Lack of service Network is down |
1. Invest in network security that scales according to needs 2. All protections must be enabled while keeping business continuity 3. Scalable secure remote access |
Coronavirus Related Attacks Reach 200,000 Weekly
Learn about the latest network, cloud and mobile threats
READ REPORT
Hackers Set Return-to-Work Traps
As businesses transition their workforces back to the office, hackers are distributing phishing emails and malicious files disguised as COVID-19 training materials.
- Double digit percentage rises for Corona-related malicious sites in Latin America, Southeast Asia, Africa and Eastern Europe
- Non coronavirus-related headline news (including ‘Black Lives Matter’) being used in phishing scams
- In regions where restrictions are being lifted there is a decrease in Corona-related malicious websites
Threat Actors Join in the Race Towards a Coronavirus Vaccine
Hackers are sending emails with subject lines related to the coronavirus vaccine, in order to trick recipients into downloading malicious Windows, Word and Excel files designed to extract a person’s usernames and passwords directly from their computers.
LEARN MORE
Security Concerns Over Contact Tracing Apps
Researchers flag concern around implementation of contact tracing apps, citing possibilities of device traceability, personal data compromise, app traffic interception, and fake health reports.
LEARN MOREFixing the Zoom
‘Vanity Clause’
Check Point and Zoom collaborate to fix vanity URL issue
Check Point and Zoom identify a security issue in Zoom’s customizable URL feature.
If exploited, a hacker would have been able to manipulate ID meeting links by posing as an employee of a potential victim organization via Zoom, giving the hacker a vector for stealing credentials or sensitive information.
LEARN MORE
Moving Beyond Coronavirus onto Safer Ground
We’ve all experienced that 2020 is like no other year in our recent history. It’s a crisis of such magnitude that has altered the way of life for societies around the world. It’s effects have been felt on our institutions and organizations.
We’ve also learned that the ability to be agile and act swiftly has been a necessity. The pandemic will pass over time, but it’s effects will be felt forever. As we move to safer ground, we’ll not take for granted our ability to stay connected and be protected. The “new normal” will require us to make changes and adapt to a new reality that could include a major cyber pandemic.
To know more what you can do for cyber security, contact your local Check Point Software representative. We’re ready to help with your move to safer ground.
Coronavirus Impact: Cyber Criminals Target Zoom Domains
During the past few weeks, we have witnessed a major increase in new domain registrations with names including “Zoom”, which has 20% of the video conferencing market. Since the beginning of 2020, more than 1700 new domains were registered and 25% of them were registered in the past week. Out of these registered domains, 4% have been found to contain suspicious characteristics. Learn more about the cyber attacks
targeting users of Zoom video conferencing.

Protection from Hackers and Phishing Attempts
Since the Coronavirus outbreak began, a number of new websites have registered with domain names related to the virus. Here are our recommendations to stay protected:
- Be cautious of special offers
- Beware of lookalike domains
- Ensure that you are visiting the authentic source
Coronavirus Impact: As Retailers Close their Doors, Hackers Open for Business
As the world takes action to contain coronavirus, hackers around the globe are taking advantage of the outbreak by accelerating activities to spread their own infections. It’s important to:
- Remain cautious and alert
- Report anything suspicious

Technical Resources
Check Point and Partners Give Back
In early March 2020, a cross-functional group of Check Point employees formed The Americas COVID-19 Donation program with a goal to provide financial support to charities on the front lines of the pandemic. To maximize our impact we approached partners asking for matching donations thereby doubling our strength! Collectively, our efforts have led to more than $1M in donations to 80+ organizations and the numbers keep growing.
LEARN MOREOther Topics of Interest
- Protect Your Business from the SolarWinds Sunburst Attack
- SolarWinds Sunburst Attack: What Do You Need to Know?
- Sunburst, Teardrop, and the New NetSec Normal
- Sunburst Report
- The Sunburst Attack: A Second Strain of Malware and Strengthening Your Security
- Critical Microsoft Vulnerability Found
- Coronavirus-themed Spam Spreads Dangerous Malware

 \
\