What is Ransomware?
In 2025, ransomware has evolved significantly past simple file encryption. While denying access to your data by encrypting it and demanding a ransom payment for the decryption key remains a core tactic, today’s ransomware does much more. Cyber– attackers now frequently incorporate additional functionalities like data theft. This means they don’t just lock up your files; they also steal sensitive information. This dual threat creates even greater pressure for victims to pay the ransom, as they face not only data loss but also the potential for public exposure of stolen data or its sale on the dark web.
Ransomware has quickly become the most prominent and visible type of malware. Recent ransomware attacks have impacted hospitals’ ability to provide crucial services, crippled public services in cities, and caused significant damage to various organizations.
Why Are Ransomware Attacks Emerging?
Ransomware reached record levels in 2025, with 7,960 victims listed on double‑extortion leak sites—a 53% increase year‑over‑year. Activity peaked in both Q1 and again in Q4, driven largely by mass‑exploitation campaigns, including Cl0p’s zero‑day attacks that compromised hundreds of organizations early in the year. The collapse of several major RaaS groups reshaped the ecosystem, enabling Qilin to surge ahead as the most active operator, publishing over 1,000 victims and tripling its monthly volume.
The United States accounted for roughly 52% of all disclosed victims, far exceeding other regions. Attacks remained centered on commercial sectors, particularly business services, consumer goods & services, and industrial manufacturing. Overall, the ecosystem continued to expand and reorganize, demonstrating increasing resilience and aggression despite global enforcement efforts.
How Ransomware Works
In order to be successful, ransomware needs to gain access to a target system, encrypt the files there, and demand a ransom from the victim.
While the implementation details vary from one ransomware variant to another, all share the same core three stages
- Step 1. Infection and Distribution Vectors
Ransomware, like any malware, can gain access to an organization’s systems in a number of different ways. However, ransomware operators tend to prefer a few specific infection vectors.
One of these is phishing emails. A malicious email may contain a link to a website hosting a malicious download or an attachment that has downloader functionality built in. If the email recipient falls for the phish, then the ransomware is downloaded and executed on their computer.
Another popular ransomware infection vector takes advantage of services such as the Remote Desktop Protocol (RDP). With RDP, an attacker who has stolen or guessed an employee’s login credentials can use them to authenticate to and remotely access a computer within the enterprise network. With this access, the attacker can directly download the malware and execute it on the machine under their control.
Others may attempt to infect systems directly, like how WannaCry exploited the EternalBlue vulnerability. Most ransomware variants have multiple infection vectors.
In 2025, ransomware attacks frequently leverage vulnerabilities within an organization’s third-party suppliers, recognizing them as a weaker entry point. This often begins with compromised credentials or unpatched software in a vendor’s system, allowing attackers to gain initial access. From there, the threat actors exploit the trusted connection between the supplier and the target organization to move laterally and deploy ransomware, bypassing the main company’s direct defenses.
- Step 2. Data Encryption
After ransomware has gained access to a system, it can begin encrypting its files. Since encryption functionality is built into an operating system, this simply involves accessing files, encrypting them with an attacker-controlled key, and replacing the originals with the encrypted versions. Most ransomware variants are cautious in their selection of files to encrypt to ensure system stability. Some variants will also take steps to delete backup and shadow copies of files to make recovery without the decryption key more difficult.
- Step 3. Ransom Demand
Once file encryption is complete, the ransomware is prepared to make a ransom demand. Different ransomware variants implement this in numerous ways, but it is not uncommon to have a display background changed to a ransom note or text files placed in each encrypted directory containing the ransom note. Typically, these notes demand a set amount of cryptocurrency in exchange for access to the victim’s files. If the ransom is paid, the ransomware operator will either provide a copy of the private key used to protect the symmetric encryption key or a copy of the symmetric encryption key itself. This information can be entered into a decryptor program (also provided by the cybercriminal) that can use it to reverse the encryption and restore access to the user’s files.
While these three core steps exist in all ransomware variants, different ransomware can include different implementations or additional steps. For example, ransomware variants like Maze perform files scanning, registry information, and data theft before data encryption, and the WannaCry ransomware scans for other vulnerable devices to infect and encrypt.
Types of Ransomware Attacks
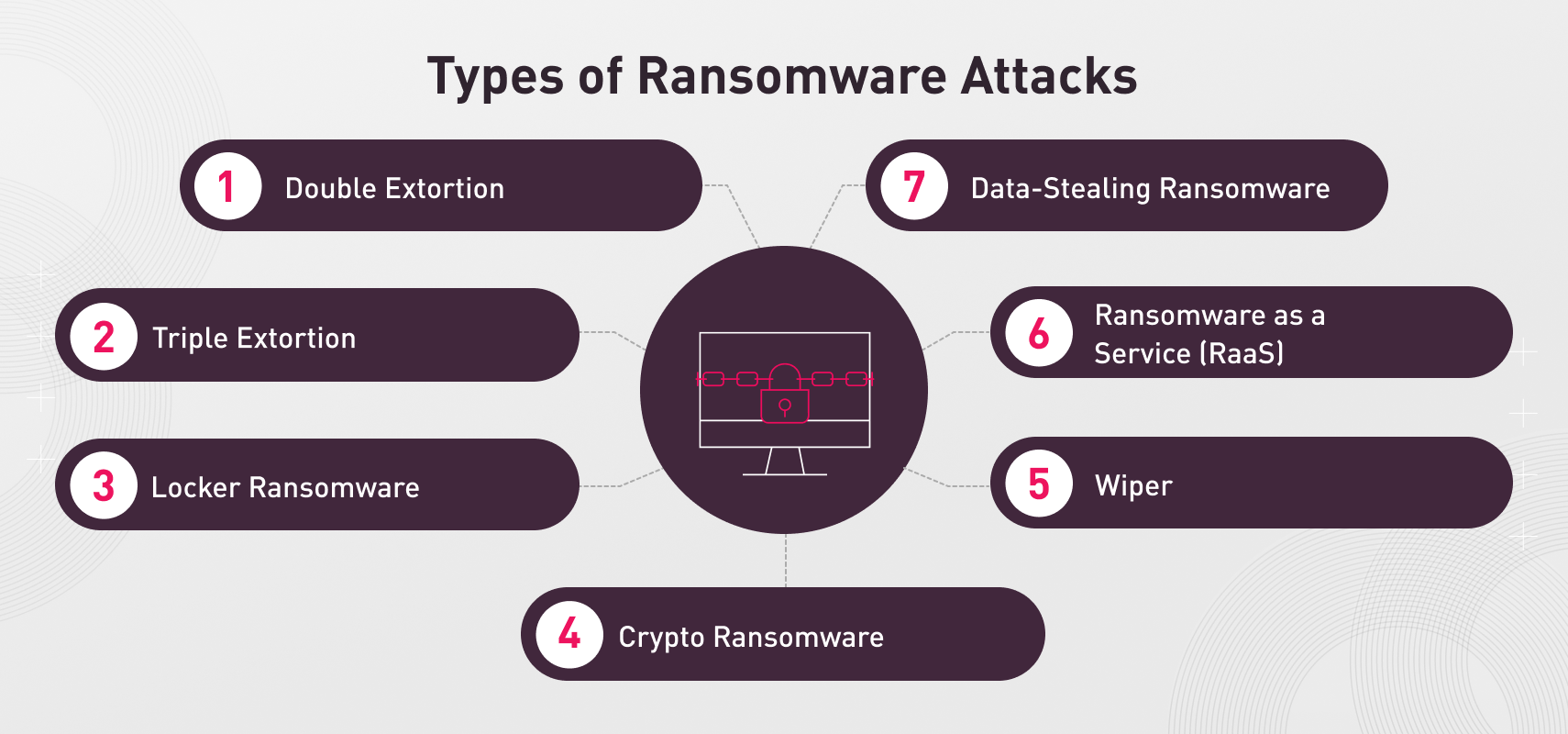
Ransomware has evolved significantly over the past few years. Some important types of ransomware and related threats include:
- Double Extortion: Double-extortion ransomware like Maze combines data encryption with data theft. This technique was developed in response to organizations refusing to pay ransoms and restoring from backups instead. By stealing an organization’s data as well, the cybercriminals could threaten to leak it if the victim doesn’t pay up.
- Triple Extortion: Triple extortion ransomware adds a third extortion technique to double extortion. Often, this includes demanding a ransom from the victim’s customers or partners or performing a distributed denial-of-service (DDoS) attack against the company as well.
- Locker Ransomware: Locker ransomware is ransomware that doesn’t encrypt the files on the victim’s machine. Instead, it locks the computer — rendering it unusable to the victim — until the ransom has been paid.
- Crypto Ransomware: Crypto ransomware is another name for ransomware that underscores the fact that ransomware payments are commonly paid in cryptocurrency. The reason for this is that cryptocurrencies are digital currencies that are more difficult to track since they’re not managed by the traditional financial system.
- Wiper: Wipers are a form of malware that is related to but distinct from ransomware. While they may use the same encryption techniques, the goal is to permanently deny access to the encrypted files, which may include deleting the only copy of the encryption key.
- Ransomware as a Service (RaaS): RaaS is a malware distribution model in which ransomware gangs provide “affiliates” with access to their malware. These affiliates infect targets with the malware and split any ransom payments with the ransomware developers.
- Data-Stealing Ransomware: Some ransomware variants have focused on data theft, abandoning data encryption entirely. One reason for this is that encryption can be time-consuming and easily detectable, providing an organization with an opportunity to terminate the infection and protect some files from encryption.
Popular Ransomware Variants
Dozens of ransomware variants exist, each with its own unique characteristics. However, some ransomware groups have been more prolific and successful than others, making them stand out from the crowd.
1.Ransomhub
RansomHub, a prominent Ransomware-as-a-Service (RaaS) group that emerged in February 2024, quickly rose to prominence by attracting affiliates from disrupted groups like ALPHV and LockBit. Despite a low payment rate, their high affiliate profit-sharing model (90%) drove a surge in attacks, especially in July and August 2024, primarily targeting U.S. and Brazilian businesses. RansomHub’s ransomware, written in Golang and C++, is known for its fast encryption, use of EDRKillShifter, and recent implementation of remote encryption. However, on April 1, 2025, RansomHub’s operations ceased, with affiliates reportedly shifting to Qilin and DragonForce claiming control, marking its demise in the ransomware landscape.
2.Akira
Akira, a ransomware variant first identified in Q1 2023, targets both Windows and Linux systems using ChaCha2008 encryption. It infiltrates systems via phishing emails and VPN vulnerabilities, then employs tactics like LOLBins and credential dumping to evade detection and gain privileges. Akira utilizes intermittent encryption to avoid security solutions and deletes shadow copies to hinder recovery. The group also performs extortion-only attacks, stealing data and demanding ransom without encryption. Akira demands large ransoms, primarily targeting large enterprises in North America, Europe, and Australia, particularly in education, finance, manufacturing, and healthcare. To mitigate Akira attacks, organizations should implement cybersecurity awareness training, anti-ransomware solutions, regular data backups, patch management, strong user authentication (MFA), and network segmentation.
3.Play
The Play Ransomware Group, also known as Play or Playcrypt, has emerged as a significant cybercriminal entity since 2022, successfully compromising over 300 organizations globally, including high-profile targets like Microsoft Cuba, the City of Oakland, and the Swiss government. This group employs unique tactics such as intermittent encryption, which encrypts only selective parts of files to evade detection, and double extortion, where they not only encrypt data but also exfiltrate it and threaten its public release if a ransom is not paid. Play leverages vulnerabilities in FortiOS and exposed RDP servers for initial access, subsequently distributing ransomware payloads via Group Policy Objects as scheduled tasks. They operate a Tor blog to publicize their attacks and the data they’ve stolen, pressuring victims into compliance.
4.Clop
Cl0p is a ransomware that is a variant of Cryptomix malware. It’s a sophisticated threat operating as a Ransomware-as-a-Service (RaaS) that primarily targets industries handling sensitive data, such as healthcare and finance. It employs a double extortion strategy, encrypting data and threatening to publicly release stolen information if a ransom is not paid. Cl0p’s distribution methods include phishing emails and the exploitation of zero-day vulnerabilities, making it challenging to prevent. This ransomware is known for its digitally signed code, high ransom demands, use of SDBOT for self-propagation, and a preference for corporate networks. To prevent Cl0p attacks, organizations should implement AI-powered threat detection, constant monitoring, log checking for unusual activity, comprehensive employee training on phishing, quick quarantine of infected systems, and strong authentication protocols.
5.Qilin
Qilin operates as a prominent Ransomware-as-a-Service (RaaS), utilizing a highly customizable, Rust-based ransomware to target organizations across various sectors globally. This group gained significant traction in April 2025, topping the list for ransomware attacks. Qilin employs a double extortion technique, not only encrypting victims’ files and demanding a ransom for decryption, but also exfiltrating sensitive data and threatening its release even if the ransom is paid. Their sophisticated tactics include tailoring attacks to each victim, modifying filename extensions, terminating specific processes, and offering various encryption modes. Qilin advertises its services on the dark web, showcasing a proprietary data leak site (DLS) with unique company IDs and stolen account details, and reportedly gained affiliates after RansomHub shut down.
6.Ryuk
Ryuk is an example of a very targeted ransomware variant. It is commonly delivered via spear phishing emails or by using compromised user credentials to log into enterprise systems using the Remote Desktop Protocol (RDP). Once a system is infected, Ryuk encrypts certain types of files (avoiding those crucial to a computer’s operation), then presents a ransom demand.
Ryuk is well-known as one of the most expensive types of ransomware in existence. Ryuk demands ransoms that average over $1 million. As a result, the cybercriminals behind Ryuk primarily focus on enterprises that have the resources necessary to meet their demands.
7. Maze
The Maze ransomware is famous for being the first ransomware variant to combine file encryption and data theft. When targets started refusing to pay ransoms, Maze began collecting sensitive data from victims’ computers before encrypting it. If the ransom demands were not met, this data would be publicly exposed or sold to the highest bidder. The potential for an expensive data breach was used as additional incentive to pay up.
The group behind the Maze ransomware has officially ended its operations. However, this does not mean that the threat of ransomware has been reduced. Some Maze affiliates have transitioned to using the Egregor ransomware, and the Egregor, Maze, and Sekhmet variants are believed to have a common source.
8.REvil (Sodinokibi)
The REvil group (also known as Sodinokibi ) is another ransomware variant that targets large organizations.
REvil is one of the most well-known ransomware families on the net. The ransomware group, which has been operated by the Russian-speaking REvil group since 2019, has been responsible for many big breaches such as ‘Kaseya‘ and ‘JBS’
It has competed with Ryuk over the last several years for the title of the most expensive ransomware variant. REvil is known to have demanded $800,000 ransom payments.
While REvil began as a traditional ransomware variant, it has evolved over time-
They are using the Double Extortion technique- to steal data from businesses while also encrypting the files. This means that, in addition to demanding a ransom to decrypt data, attackers might threaten to release the stolen data if a second payment is not made.
9. Lockbit
LockBit is a data encryption malware in operation since September 2019 and a recent Ransomware-as-a-Service (RaaS). This piece of ransomware was developed to encrypt large organizations rapidly as a way of preventing its detection quickly by security appliances and IT/SOC teams.
10. DearCry
In March 2021, Microsoft released patches for four vulnerabilities within Microsoft Exchange servers. DearCry is a new ransomware variant designed to take advantage of four recently disclosed vulnerabilities in Microsoft Exchange
The DearCry ransomware encrypts certain types of files. Once the encryption is finished, DearCry will show a ransom message instructing users to send an email to the ransomware operators in order to learn how to decrypt their files.
11. Lapsus$
Lapsus$ is a South American ransomware gang that has been linked to cyberattacks on some high-profile targets. The cyber gang is known for extortion, threatening the release of sensitive information, if demands by its victims aren’t made. The group has boasted breaking into Nvidia, Samsung, Ubisoft and others. The group uses stolen source code to disguise malware files as trustworthy.
How Does Ransomware Affect Businesses?
A successful ransomware attack can have various impacts on a business. Some of the most common risks include:
- Financial Losses: Ransomware attacks are designed to force their victims to pay a ransom. Additionally, companies can lose money due to the costs of remediating the infection, lost business, and potential legal fees.
- Data Loss: Some ransomware attacks encrypt data as part of their extortion efforts. Often, this can result in data loss, even if the company pays the ransom and receives a decryptor.
- Data Breach: Ransomware groups are increasingly pivoting to double or triple extortion attacks. These attacks incorporate data theft and potential exposure alongside data encryption.
- Downtime: Ransomware encrypts critical data, and triple extortion attacks may incorporate DDoS attacks. Both of these have the potential to cause operational downtime for an organization.
- Brand Damage: Ransomware attacks can harm an organization’s reputation with customers and partners. This is especially true if customer data is breached or they receive ransom demands as well.
- Legal and Regulatory Penalties: Ransomware attacks may be enabled by security negligence and may include the breach of sensitive data. This may open up a company to lawsuits or penalties being levied by regulators.
Common Ransomware Target Industries
Ransomware can target any company across all industry verticals. However, ransomware is commonly deployed as part of a cybercrime campaign, which is often targeted at a particular industry. The top five ransomware target industries in 2023 include:
- Education/Research: The Education/Research sector experienced 2046 ransomware attacks in 2023, a 12% drop from the previous year.
- Government/Military: Government and military organizations were the second most targeted industry with 1598 attacks and a 4% decrease from 2022.
- Healthcare: Healthcare experienced 1500 attacks and a 3% increase, which is particularly concerning due to the sensitive data and critical services that it provides.
- Communications: Communications organizations experienced an 8% growth in 2023, totaling 1493 known attacks.
- ISP/MSPs: ISPs and MSPs — a common ransomware target due to their potential for supply chain attacks — experienced 1286 ransomware attacks in 2023, a 6% decrease.
How to Protect Against Ransomware
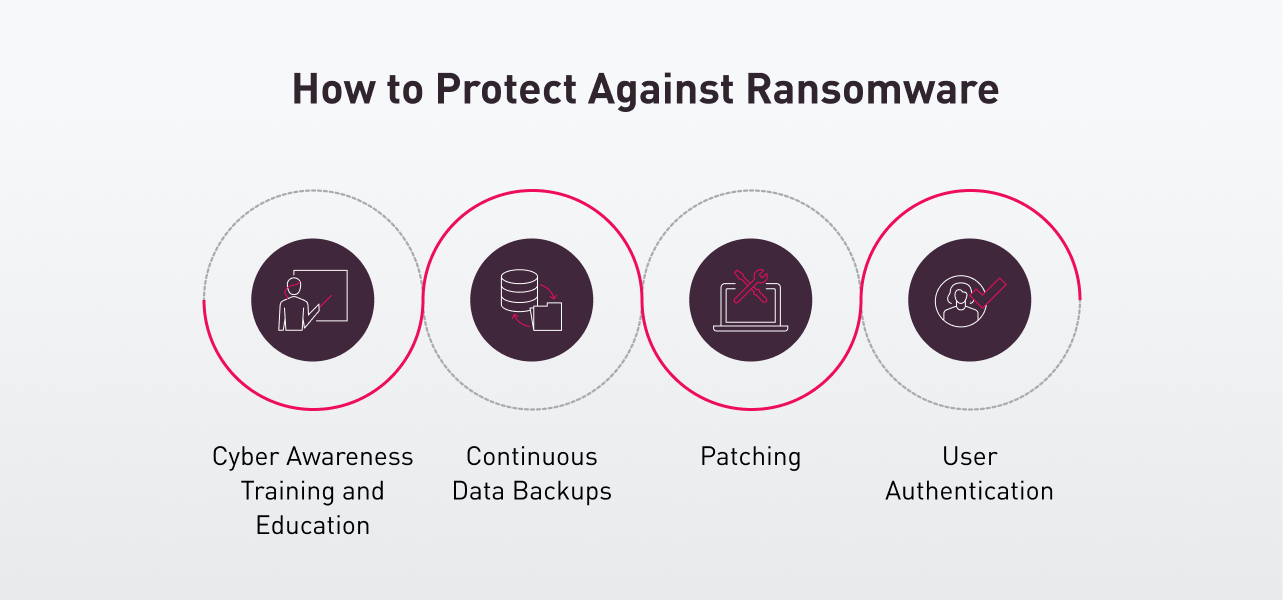
- Utilize Best Practices
Proper preparation can dramatically decrease the cost and impact of a ransomware attack. Taking the following best practices can reduce an organization’s exposure to ransomware and minimize its impacts:
- Cyber Awareness Training and Education: Ransomware is often spread using phishing emails. Training users on how to identify and avoid potential ransomware attacks is crucial. As many of the current cyber-attacks start with a targeted email that does not even contain malware, but only a socially-engineered message that encourages the user to click on a malicious link, user education is often considered as one of the most important defenses an organization can deploy.
- Continuous data backups: Ransomware’s definition says that it is malware designed to make it so that paying a ransom is the only way to restore access to the encrypted data. Automated, protected data backups enable an organization to recover from an attack with a minimum of data loss and without paying a ransom. Maintaining regular backups of data as a routine process is a very important practice to prevent losing data, and to be able to recover it in the event of corruption or disk hardware malfunction. Functional backups can also help organizations to recover from ransomware attacks.
- Patching: Patching is a critical component in defending against ransomware attacks as cyber-criminals will often look for the latest uncovered exploits in the patches made available and then target systems that are not yet patched. As such, it is critical that organizations ensure that all systems have the latest patches applied to them, as this reduces the number of potential vulnerabilities within the business for an attacker to exploit.
- User Authentication: Accessing services like RDP with stolen user credentials is a favorite technique of ransomware attackers. The use of strong user authentication can make it harder for an attacker to make use of a guessed or stolen password
-
Reduce the Attack Surface
With the high potential cost of a ransomware infection, prevention is the best ransomware mitigation strategy. This can be achieved by reducing the attack surface by addressing:
- Phishing Messages by employing email protection, such as Harmony Email Security
- Unpatched Vulnerabilities, Compromised credentials and other exposed assets on the dark web using an external risk management tool such as Check Point ERM
- Remote Access Solutions, by employing SASE protection.
- Mobile Malware security.
-
Deploy an Anti-Ransomware Solution
The need to encrypt all of a user’s files means that ransomware has a unique fingerprint when running on a system. Anti-ransomware solutions are built to identify those fingerprints. Common characteristics of a good anti-ransomware solution include:
- Wide variant detection
- Fast detection
- Automatic restoration
- Restoration mechanism not based on common built-in tools (like ‘Shadow Copy’, which is targeted by some ransomware variants)
How to Remove Ransomware?
A ransom message is not something anyone wants to see on their computer as it reveals that a ransomware infection was successful. At this point, some steps can be taken to respond to an active ransomware infection, and an organization must make the choice of whether or not to pay the ransom.
- How to Mitigate an Active Ransomware Infection
Many successful ransomware attacks are only detected after data encryption is complete and a ransom note has been displayed on the infected computer’s screen. At this point, the encrypted files are likely unrecoverable, but some steps should be taken immediately:
- Quarantine the Machine: Some ransomware variants will try to spread to connected drives and other machines. Limit the spread of the malware by removing access to other potential targets.
- Leave the Computer On: Encryption of files may make a computer unstable, and powering off a computer can result in loss of volatile memory. Keep the computer on to maximize the probability of recovery.
- Create a Backup: Decryption of files for some ransomware variants is possible without paying the ransom. Make a copy of encrypted files on removable media in case a solution becomes available in the future or a failed decryption effort damages the files.
- Check for Decryptors: Check with the No More Ransom Project to see if a free decryptor is available. If so, run it on a copy of the encrypted data to see if it can restore the files.
- Ask For Help: Computers sometimes store backup copies of files stored on them. A digital forensics expert may be able to recover these copies if they have not been deleted by the malware.
- Wipe and Restore: Restore the machine from a clean backup or operating system installation. This ensures that the malware is completely removed from the device
How Can Check Point Help
Check Point’s Anti-Ransomware technology uses a purpose-built engine that defends against the most sophisticated, evasive zero-day variants of ransomware and safely recovers encrypted data, ensuring business continuity and productivity. The effectiveness of this technology is being verified every day by our research team, and consistently demonstrating excellent results in identifying and mitigating attacks.
Check Point Endpoint Security, Check Point’s leading endpoint prevention and response product, includes Anti-Ransomware technology and provides protection to web browsers and endpoints, leveraging Check Point’s industry-leading network protections. Check Point Endpoint Security delivers complete, real-time threat prevention and remediation across all malware threat vectors, enabling employees to work safely no matter where they are, without compromising on productivity.
Check Point External Risk Management significantly enhances an organization’s defense against ransomware. Through continuous Attack Surface Management (ASM), Check Point discover and monitor all internet-facing assets, identifying vulnerabilities and misconfigurations that ransomware gangs could exploit. Check Point’s deep and dark web monitoring proactively detects leaked credentials before they can be leveraged for initial access or account takeovers, a common ransomware entry point. Furthermore, Check Point provides crucial Supply Chain Intelligence, continuously assessing the security posture of third-party vendors and technologies to mitigate risks introduced through the supply chain, a growing vector for ransomware attacks. Finally, their strategic threat intelligence, derived from vast data collection and analysis, provides real-time insights into emerging ransomware trends, threat actor tactics, techniques, and procedures (TTPs), enabling organizations to proactively harden their defenses and make informed security decisions before an attack materializes.
