Step Up to Gen V Cyber Security.
Security That Prevents Fifth-Generation Cyber Attacks.
2017 was a global wake-up call to get serious about addressing the cyber threat landscape. Unprecedented levels of cyber attacks played out as large-scale, multi-vector mega attacks that inflicted major damage on business and reputation. As a result, we find ourselves in the midst of the fifth generation of cyber attacks. To remain operationally secure now, businesses require a new generation of cyber security: Gen V.
In Q1 2018, Check Point surveyed 443 security professionals around the world about their security infrastructures. The results showed that most security infrastructures are generationally and dangerously behind the level of attacks they must protect against. This state of affairs is urgent and startling.

We Are at an Inflection Point
Hackers are exploiting the fact that most organizations rely on older generations of security. As the sophistication and scale of attacks has grown, previous generations of security, which merely detect, are no longer effective. Increased connectivity has created a vast new frontier – a target-rich hunting ground for cyber attackers and illicit acts. And with every successful advancement of malicious activity, a new generation of IT security has spawned. What’s needed for the latest generation of cyberattacks: advanced real-time threat prevention that protects all networks, virtual, cloud, remote office and mobile operations.
The Evolution of Cyber Threats and Their Solutions
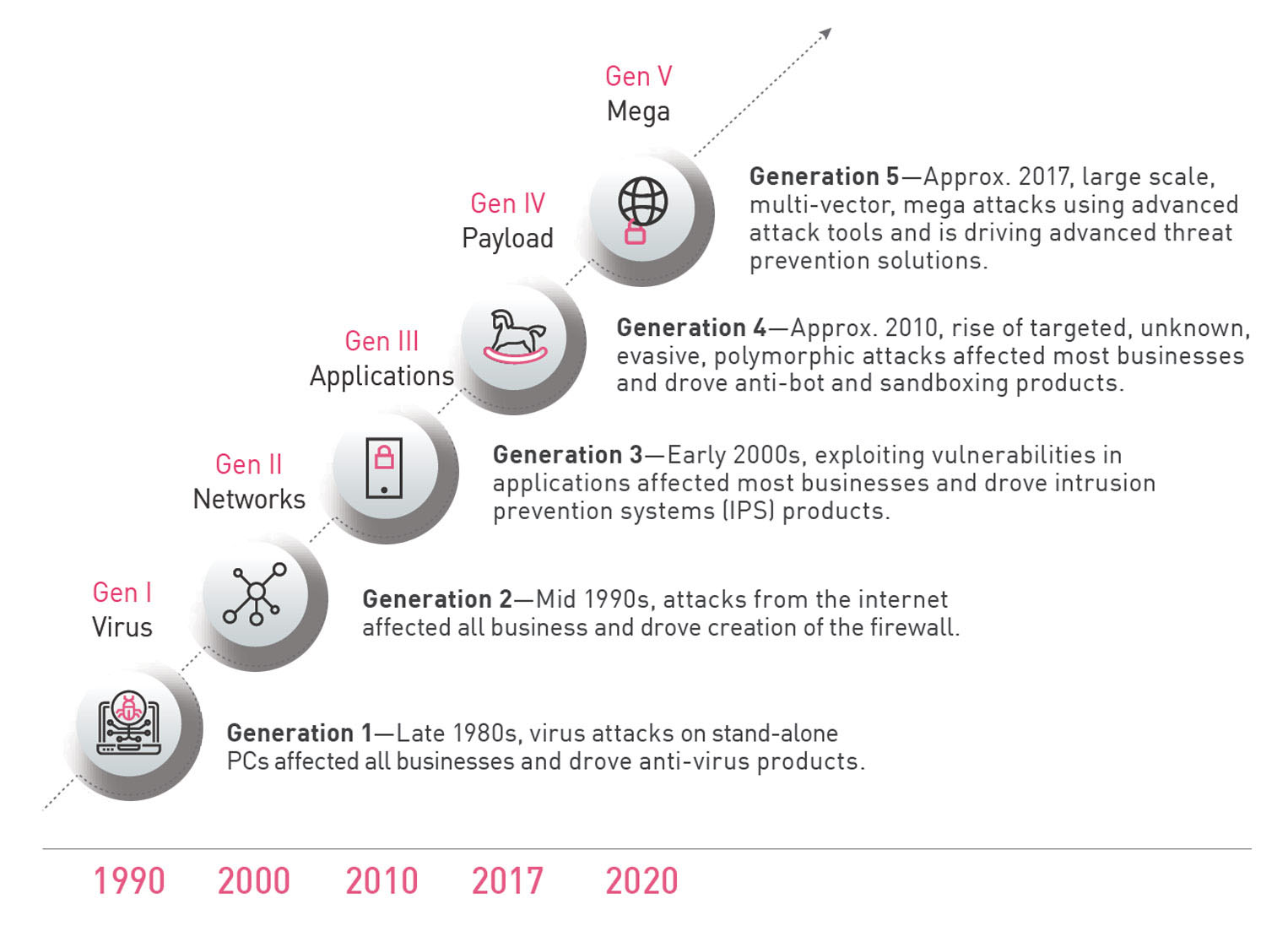
Likewise, cyber security protection adapted accordingly with each passing generation:
- Generation I: Hackers were typically clever pranksters. Virus attacks on stand-alone PCs began mostly as annoyances or mistakes. To halt disruption, anti-virus products were developed.
- Generation II: As the internet started to become central to business and our lives, hackers began to organize and communicate among themselves, laying the groundwork for cyber crime for financial gain. Malicious and volatile software began to crop up. This gave rise to the first firewall, along with intrusion detection systems (IDS).
- Generation III: Attackers began to analyze networks and software to find and exploit vulnerabilities throughout the IT infrastructure. Firewalls, anti-virus, and intrusion detection system (IDS) products were proving to be insufficient in the face of exploits. This sparked the era of best-of-breed patchwork security models as businesses scrambled to protect themselves. Check Point began focusing on prevention and launched intrusion prevention systems (IPS) products.
- Generation IV: Cyberattacks reached a new level of sophistication, ranging from international espionage to massive breaches of personal information to large-scale internet disruption. Attacks were hidden in everything from resumes to picture files—evasive and polymorphic. While internet security of the 2nd and 3rd generations provided access control and inspected all traffic, it was incapable of validating actual end-user content received in email, through file downloads and more. In response, Check Point introduced anti-bot and sandboxing products to address previously unknown and zero-day attacks.
- Generation V: Advanced ‘weapons-grade’ hacking tools are leaked, allowing attackers to move fast and infect large numbers of businesses and entities across huge swaths of geographic regions. Large-scale, multi-vector mega attacks spark a need for integrated and unified security structures. Prior generations of patchwork, best-of-breed, detect-first technologies are no match for the rapid and stealthy attacks of the fifth generation. Check Point develops a unified architecture with advanced threat prevention solutions that shares threat intelligence in real time, preventing attacks on virtual instances, cloud deployments, endpoints, remote offices, and mobile devices.
It’s Time to Modernize
Attackers operate freely and can advance without hindrance. Meanwhile, businesses are held back by up-time requirements, change control, compliance controls, staffing shortages, budget restrictions – and best-of-breed security infrastructures. Adding more products to an already operationally heavy security infrastructure compounds the problem. The bottom line is that business cannot keep up.
Most businesses are stuck in the world of 2nd- and 3rd-generation security, which only protects against viruses, application attacks, and payload delivery. Networks, virtualized data centers, cloud environments, and mobile devices are left exposed. To ensure a cyber secure organization, businesses must evolve to 5th-generation security: advanced threat prevention that uniformly prevents attacks on a business’s entire IT infrastructure.
Gen V Defined
Gen V security leaves the patch work, best-of-breed deployments of the past behind. Instead, it’s characterized by an architecture that unifies all networks, cloud, and mobile, supported by automatic and immediate threat intelligence.
5th-generation security is marked by key advancements over the prior 4th-generation security:
- Consolidates next-generation-firewall (NGFW), sandbox, bot security, endpoint security and other security controls into a single unified security system.
- Shares real-time threat information throughout the system.
- Prevents advanced 5th-generation and first occurrence of new attacks; does not allow first-attack “patient-zero” infection.
- Extends prevention of advanced attacks to cloud deployments and mobile devices as part of the single, unified security system.
- Uniformly prevents attacks across a business’s entire IT infrastructure of computer networks, virtual instances, cloud deployments, endpoints, remote offices and mobile devices.
- Centrally manages, monitors and responds to all security activities and events as a single, unified security system.
Gen V Defined
Brought to you by Check Point
Check Point is the first consolidated security architecture across networks, cloud and mobile, providing the highest level of threat prevention against both known and unknown targeted attacks to keep you protected now and in the future.
- Protection against targeted attacks with unified threat intelligence and open interfaces
- Preemptive threat prevention with real-time sharing of threat information for hyper-responsive protection
- Simplified, agile, and unified management with consolidated security layers, providing superior policy efficiency and single-pane-of-glass visibility

As Check Point’s Gen V cyber security solution, Check Point delivers unprecedented protection against current and potential attacks—today and in the future.
2023 Cyber Security Report
Geo-political conflicts trigger all-time high for cyberattacks.
See more trends and insights.