Anti-Phishing
Phishing is one of the most talked about cyber-attack, and for a good reason. It can come in many shapes and forms, as it is constantly evolving and introducing new ways of tricking users using their biggest weakness – their human nature. This is why organizations must adopt security solutions with anti phishing capabilities.
Check Point Anti-Phishing
![]()
Superior
Prevention
Block even the most sophisticated phishing attacks such as Business Email Compromise and impersonation
![]()
Protect All Your
Weak Links
Prevent phishing attacks across email, mobile and endpoint devices
![]()
Leverage
ThreatCloud AI
Anti-phishing is powered by the world’s most powerful threat intelligence database
The History of Phishing
Phishing started in the mid 1990’s with the goal of luring users to voluntarily give information such as account credentials or other sensitive data. That means that these scams have been around for nearly 30 years, and they don’t seem to be going away anytime soon. Phishing scams have greatly evolved since their early days, and now include sophisticated techniques such as social engineering. While most phishing attacks back in the day were sent in mass in the hopes of ‘catching’ a few users, this is not the case with many of these attacks nowadays, which often target very specific personnel or users.
Watch the webinar:
History, Evolution & Future of Social Engineering
Join us as Maya Horowitz, our VP Research, takes us on a fascinating journey through the most shocking social engineering scams in history, how they evolved to what we see in our mailboxes today, and where it’s all possibly headed in the near future.
WATCH ON DEMANDRead the eBook:
History, Evolution & Future of Social Engineering
Embark on a fascinating journey from biblical times to 20th century’s biggest social engineering scams, how they evolved into what we see in our mailboxes every day, and where we’re headed in the near future.
DOWNLOAD EBOOKWhy are Phishing Attacks So Dangerous?
Organizations must deploy anti phishing solutions to protect employees and their own businesses against today’s phishing attacks, which can be extremely targeted, well thought of, and include a hefty amount of research work behind them. Attackers spend a lot of time studying their pray and only then attack, to ensure the attack’s success. Today’s phishing schemes cost organizations millions of dollars, and include some more specific types such as Business Email Compromise (BEC) and impersonation attacks, which are extremely sophisticated. One example of a recent BEC attack is the Florentine Banker Group case that our own CPR revealed earlier this year, and included a meticulous plan and execution.
Phishing attacks may can come from different attack vectors, most common one being email. Another common attack vectors are phishing sites and text messages, usually aimed to stealing credentials in order to perform Account Takeover, which can lead to devastating results such as data loss, fraudulent money transfers and more. As mentioned, since these attacks are specifically designed to exploit the human nature, it is extremely important for organizations to take actions that would prevent these attacks from ever reaching their employees. Educating employees is important, but in times where remote work is so common and employees get much more emails and messages than they can deal with, let alone recognize a sophisticated attack, anti-phishing must come into play.
Check Point’s anti-phishing solutions includes different products to address different attack vectors from which phishing attacks come – email, mobile, endpoint and network.
Check Point Anti-Phishing Solutions
Anti-Phishing for Office 365 & G Suite with Workspace Security Email & Office
Workspace Security Email & Office deploys between the inbox and its native security. The solution secures inbound, outbound, and internal email from phishing attacks that evade platform-provided solutions and email gateways. It works with these other solutions and doesn’t require any MX record changes that broadcast security protocols to hackers.
API-based integration allows Workspace Security Email & Office to analyze all historical emails in order to determine prior trust relations between the sender and receiver, increasing the likelihood of identifying user impersonation or fraudulent messages. Artificial Intelligence (AI) and Indicators of Compromise (IoCs) used in the past train the Workspace Security Email & Office platform for what to look for in complex zero-day phishing attacks.
Granular Visibility into Phishing Attacks
Granular visibility into Phishing attacks See every threat caught by Workspace Security Email & Office, the email subject, content, and why it was determined to be phishing based on the 300+ indicators Workspace Security Email & Office looks at in every email. Phishing indicators are explained in plain English, so it is easy to assess the potential impact of an attack.

Anti-Phishing for Mobile Devices with Check Point Endpoint Security
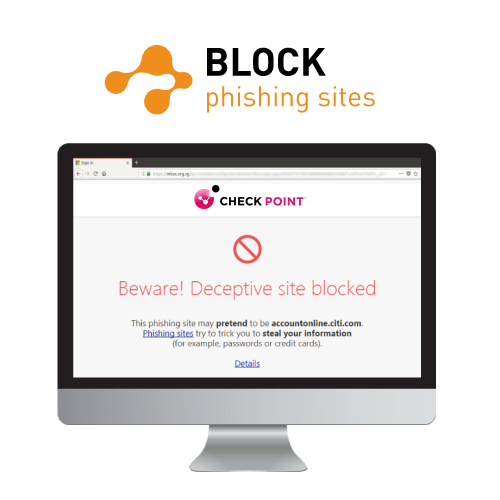
Zero-Phishing identifies and blocks the use of phishing sites in real time. It even protects against previously unknown phishing sites. When a user browses a website, and prior to typing in his/her credentials, the zero-phishing engine will inspect, identify, and block phishing sites. If the site is deemed malicious, the user will not be able to enter credentials. This engine offers zero-day protection based on site characteristics, such as known malicious URLs. Even brand-new phishing sites can be identified.
Zero-Phishing Also Prevents Credentials Re-use, So Users Won’t Expose Their Corporate Passwords
On-access activation
Real-time inspection
Dozens of indicators
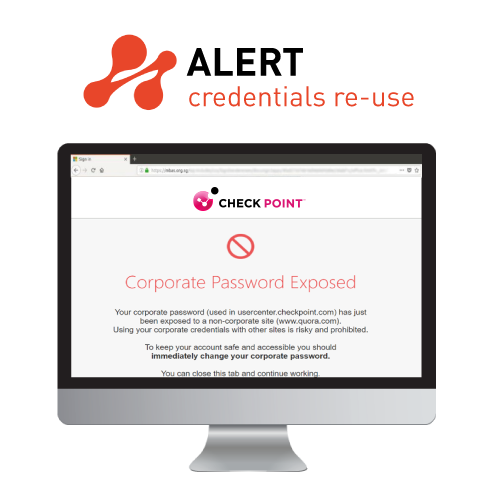
Compares cached PW hashes
Collected on internal sites
Enforced on external sites
Collected from
Dark Web Alerts user on usage
Notifies Admin
Anti-Phishing for Mobile Devices with Check Point Endpoint Security
Check Point’s Zero-Phishing technology for mobile devices. It allows organizations to combat zero-day phishing attacks by inspecting the web page itself and making an informed determination as to whether it is a phishing site. Combined with the SSL inspection feature, organizations can enjoy total protection from phishing sites, no matter which protocol they use or if it is a previously unknown site.
The Power Behind Pre-Emptive User Protection
Check Point Anti-Phishing solutions eliminate potential threats before they reach users without affecting workflows or productivity.
- Click-time URL protection examines and blocks suspicious links in real time, removing the risk of URLs that are weaponized after the email has been sent.
- Zero-day phishing protection identifies and blocks new and known phishing sites by analyzing the characteristics of the page and URL.
- Eliminates risk from incoming email by inspecting all aspects of messages before they enter the mailbox, including attachments, links and email text.






