Zero Trust Database Access
Confidently provide access to development and production environments through Check Point’s role-based policy engine, that provides tailored, privileged access to your most sensitive data.
REQUEST A DEMOThe Most Secure Way to Manage Database Access
Today’s engineering teams are leveraging the agility and flexibility of cloud-based development environments. The rapid pace of development and deployment increases the need for accessibility, which increases the risk of simple human error which can corrupt, delete, or drop valuable data from your database. But, traditional perimeter-based security methods often restrict the agility of development.
Check Point integrates natively with database protocols, providing developers with a quick and secure connection to any database through their terminal. Any underlying security measures are indetectable. At the same time, Check Point manages and monitors database access end-to-end. Security teams control who has access and what permissions they have.
NEW: VPN-as-a-Service
with Zero Trust
Secure any employee, third party or DevOps user with a choice of
application or network level access.
Role-Based Access Profiles
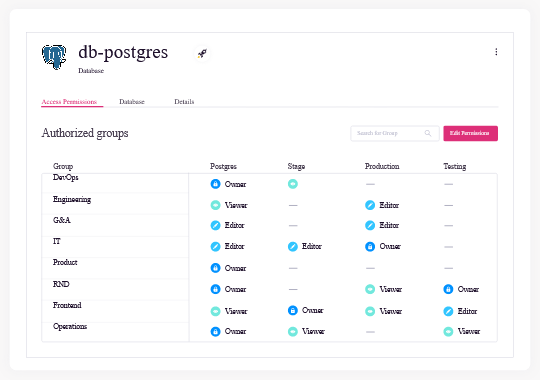
Administrators can confidently provide developers with database access and limit their roles down to “view only,” completely blocking their ability to write, drop or alter the database. Check Point supports three roles profiles: owner, editor, and viewer.
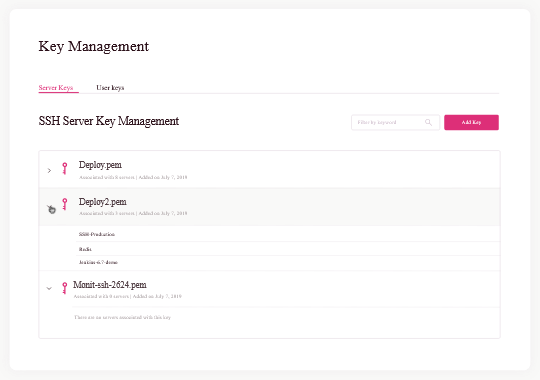
Built-In PAM
Check Point’s built-in PAM solution eliminates the risk associated with users holding static credentials. Users authenticate to a database using either a short-lived token or a public-private key pair, both of which are issued and managed through Check Point. The keys are rotated periodically and can be manually revoked at any time, instantly cutting off all access.
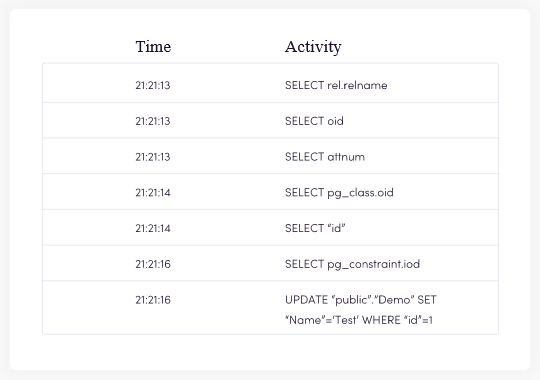
Visibility on All Queries
Check Point integrates natively with database protocols, providing users with a quick and secure connection to any database through their terminal and providing administrators with a complete audit trail of user activity, including executed queries. All audit logs are tied to user accounts and devices and can be exported to your SIEM or other monitoring tools for additional contextual data.
Our Fresh Approach to Database Access

Check Point’s Comprehensive Feature Set

Native user experience
Check Point integrates natively with database protocols, including ODBC and OLE-DB, providing users with a quick and secure connection to any database through their terminal. Any underlying security measures are undetectable.

Eliminate static credentials
Static credentials pose risks to modern IT environments as they do not include user identity information, are difficult to rotate regularly and can be used by anyone who has them. Check Point’s built-in PAM solution eliminates these risks associated with users holding static keys or VPN credentials.

Role-Based Access Profiles
Administrators can confidently provide developers with database access based on one of three roles profiles: owner, editor, and viewer.

IDP Integration
Check Point integrates with your IDP and leverages user identities for authentication and to provide centralized role-based access management on all database servers. This includes MySQL MsSQL, Mongo, Elasticsearch.

Visibility
Get a complete audit trail of user activity, including all executed queries. All audit logs are tied to user accounts and devices and can be exported to your SIEM or other monitoring tools for additional contextual data.

Real-Time Security
Provide granular, role-based access, monitoring all developer activity, and terminate sessions in real-time based on suspicious behavior.
Ready to Experience Corporate Access?
We’re here to help. Contact us to learn more about clientless, cloud-delivered SASE technology.