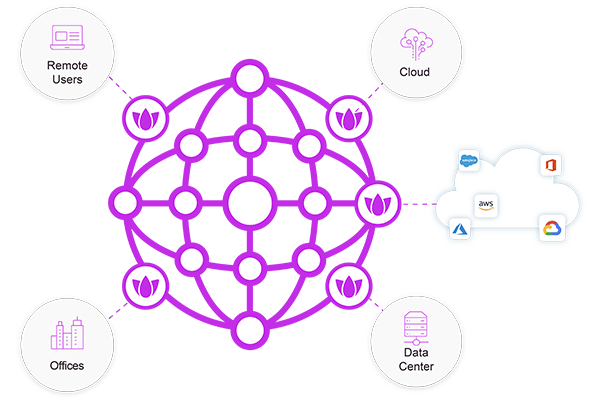
Full Mesh Private Access
Seamless secure remote access with granular zero trust policies and network segmentation
Private Access for Enhanced Security and Productivity
Hybrid work and the shift to the cloud have made the physical network perimeter obsolete. When you require a robust, global network with application-based access, Check Point SASE Private Access has you covered.

Fast Deployment
Check Point SASE offers seamless, quick deployment to keep your business running smoothly.

Full Mesh Access
Connect any user or site to any resource or data center, anywhere in the world.

Secure Access For Unmanaged Devices
Unmanaged devices are a potential high-risk security exploit. Mitigate these threats with agentless Zero Trust access.

Global Private Backbone
Our high-performance network provides fast delivery between corporate sites worldwide thanks to multiple tier-1 links at each point-of-presence (PoP), reserved bandwidth, and peering agreements.
Protect Your Workforce from the Dangers of the Web
Granular, Secure Remote Access
Protect access to company resources whether on-prem or in the cloud with zero trust access.
- Device Posture Check Ensure that devices are meeting company security requirements before connecting to the network, with continuous verification ensuring the device posture does not change.
- Unified Cloud Console Seamlessly onboard and offboard users, add or remove permissions, or even add multiple networks for greater security.
- Per-application access control Users need to connect to applications, not the entire network. Zero Trust Access rules ensure that employees get what they need to do their job. No more, no less.
- Device Inventory Management View the managed devices connecting to your network and their current posture.

12,000+ Customers Secured
Discover how Check Point SASE can improve your organization’s network security.
Seamless M&A for IT
Mergers and acquisitions can be complicated, but merging multiple networks doesn’t have to be with Check Point SASE.
Gain Control and Visibility Over Acquired Networks
Understand and stabilize the new environment
- Assess the acquired network to identify all assets, services, and cloud providers
- Establish visibility and security to monitor access and potential security gaps
- Keep networks separate (if needed) to maintain stability with an independent but observable network
- Leverage Check Point SASE as a bridge between multiple networks for seamless management
Transitioning to a Single, Secure Network
After establishing visibility and stability work towards seamless integration
- Align identity providers and enable SSO to reduce friction and improve security
- Gradually migrate cloud services to deal with more easily transferable resources, first
- Merge on-prem resources and address configuration challenges cautiously
- Implement Zero Trust policies to strengthen access controls for the new larger network
Secure Access for Unmanaged Devices
Check Point Enterprise Secure Browser creates a Zero Trust secure browsing layer on unmanaged devices separating company and personal data.

- Critical Data is never saved to the user device and disappears when the browser session ends
- Device posture check ensures unmanaged devices meet your security requirements
- Built-in session recording provides granular visibility into user actions
- Prevent users from taking copy/paste actions on sensitive documents and data
Close the unmanaged device gap with Enterprise Secure Browser
Check Point SASE Suite
Discover Check Point SASE, a seamless, robust solution for securing remote workers to on-prem and cloud resources

Internet Access
- 10x faster browsing thanks to on-device inspection
- Accurate localization
- Improved user privacy and compliance
- Comprehensive protections such as web and DNS filtering, malware protection and more

SaaS Security
- Inline and API-based enforcement with Application Control for 10,000+ cloud apps, tenant restrictions, DLP, and Threat Prevention powered by ThreatCloud AI
- Out-of-band API scanning protects data contained in SaaS apps
- AI-powered data classification with 800+ predefined data types
- SaaS posture management

SD-WAN
- Optimized routing for 10,000+ applications and users
- Auto-steering based on link health e.g. latency and packet loss
- Sub-second failover to any WAN link: MPLS, 5G, broadband
- Zero-touch provisioning with full branch-level security
See how Check Point SASE helps IT professionals manage their network with ease
Explore Check Point SASE
Private Access Datasheet
Learn more about seamless secure access with robust application-by-application access rules.
The Essential SASE for Enterprises eBook
Secure your network with SASE for flexibility, security, and performance.
