Dive into the world of vulnerability research
You’re curious, but taken aback by the cloud of terms to
memorize, processes to follow and names to know?
We’ve got you.
Understand the Basics:
- Is there a “hacker mindset”?
- Who looks for vulnerabilities, and why?
- How do we measure how “bad” a vulnerability is?
- What hoops and hurdles are there until a patch is finally issued?
- In what ways can code become vulnerable?
- What are these “Bluekeep” and “Spectre” you’ve heard of?
- What is it like being a vulnerability researcher, and what lies in the future for this field?
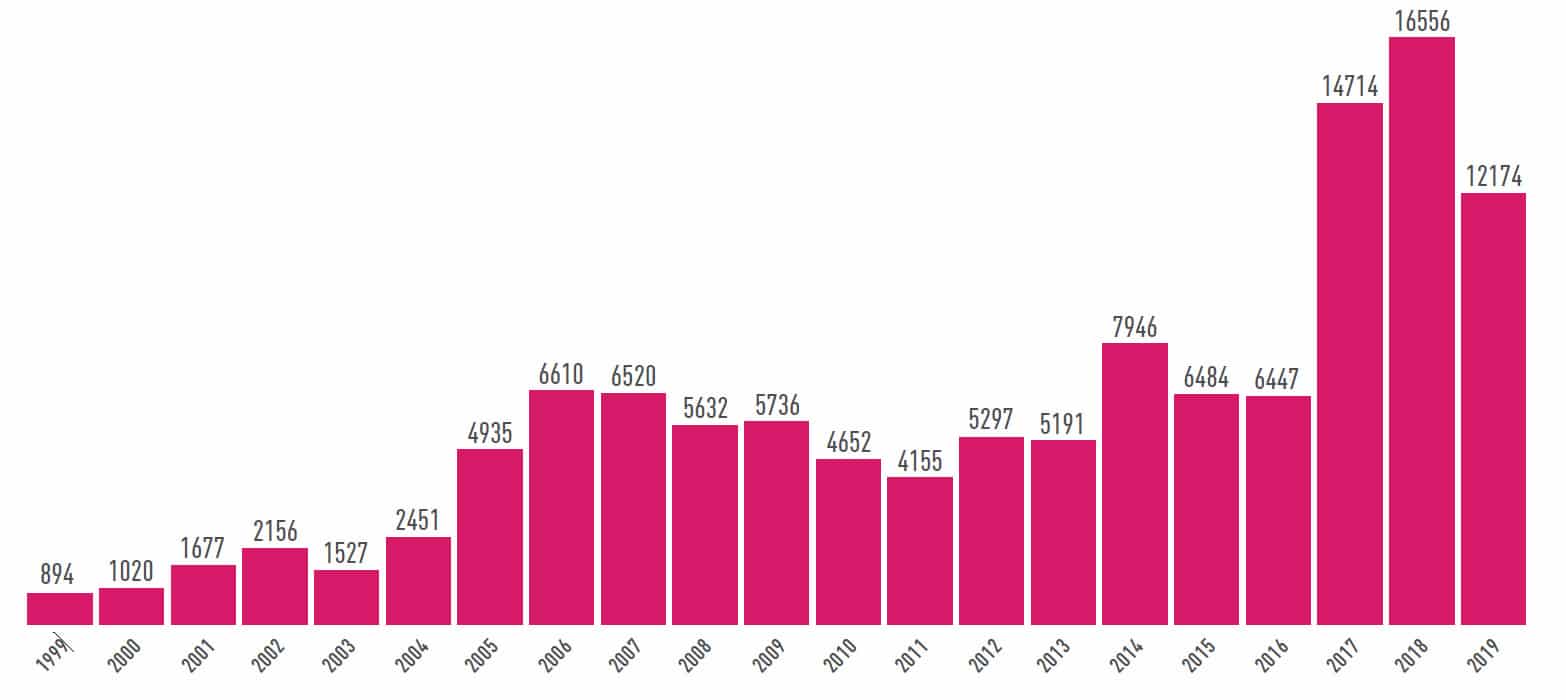
Vulnerability by Year
| Chapter | Reading Time | Key Terms |
|---|---|---|
| Introduction | 3 min | Be Excellent to Each Other! |
| What is ‘Hacking’ Anyway? | 7 min | Abstraction, ingenuity, supply & demand |
| Estimating Vuln Impact | 4 min | CVSS, vector, scope, remediation, … |
| Lifecycle of a Vuln | 9 min | Fuzzing, reversing, write-what-where, shellcode, mitigations, bypassses, disclosure |
| Why Code Becomes Vulnerable | 12 min | UAF, injection, forgery, overflow, … |
| Effects of Vulnerable Code | 2 min | Privilege escalation, information disclosure, arbitrary code execution, denial of service |
| Household Names Demystified | 15 min | Bluekeep, Curveball, Spectre, StageFright, … |
| Q&A with Sagi Tzadik | 4 min | SIGRed |
| The Long Game & Conclusion | 4 min | – |
| Total | 1 hr | – |
[..] you’d be assaulted on all sides by colorful blinking lights [..]. On your left, someone’s built a human-size copy of Tetris out of cubic LEDs. On your right, someone’s running a lockpicking workshop. Above you a 3D-printed drone flies around in a circle [..]
Attempted description of CCC (Chaos Communication Congress)
The discovery of a high-impact vulnerability can equal money, power, prestige [..] there is an implicit wacky race of highly motivated [actors] vying to be first past the post.
Chances are, there are many possible sequences of bytes that could each compromise every Windows 10 machine in existence, and the world can only operate in a sane way by virtue of bliss ignorance.
The researcher is hoping for an enthusiastic “oh god, we have to fix this immediately”, but they aren’t always so lucky.
On the woes of coordinated disclosure
In certain situations, [overflow] produces a result that makes sense.
Not this specific situation, though. Now the process is convinced that some shopping
cart contains a negative two billion apples.
I usually describe my work to my friends as “Glorified QA.”
