Simplify Your Security Strategy with the Check Point Cyber Security Platform
Reduce complexity, improve TCO and tighten risk posture through our platform approach.
Cyber Security Executives Face Growing Complexity, Costs, and Risks
Generative AI, supply chains and cloud are all expanding your attack surface, while making it easier to launch cyberattacks. And as you adopt hybrid work, hybrid networks, and hybrid clouds, the task of keeping compliance and risk levels in check becomes more difficult.
These circumstances create three main challenges.
- Manage complex and changing environmentsHybrid environments lead to a multitude of security controls with no central mitigation, while emerging technology adds risk
- Demonstrate cost-effectivenessThe onus is on executives to show how any new security investment will lower risk and add value
- Manage compliance and risk Risk to the business needs to be minimized to ensure optimal uptime, while meeting compliance mandates
Check Point named a leader in the 2025 Gartner Magic Quadrant for Hybrid Mesh Firewalls.
Adopt The Check Point Security Platform Approach and Reap the Benefits
The Check Point Platform is an AI-powered cloud-delivered security management platform that reduces complexity, lowers TCO and tightens your compliance and risk posture, while delivering the industry’s #1 catch rate.
Reduce Management Complexity Across Your digital Environment
Consolidate controls into a single platform and increase cross-product automation to quickly reduce management complexity.
- Get one intuitive security management portal that slashes the time needed to perform common tasks
- Automate policy to secure CI/CD pipelines and 10,000+ applications
- Implement automated workflows across products, tools and 3rd part security vendors, for faster mitigation
- Enable strategic initiatives such as hybrid mesh and zero trust security

CHECK POINT RELATED PRODUCTS/SOLUTIONS
CHECK POINT PORTAL
Consolidate security management into a single intuitive portal across the enterprise
CHECK POINT EVENTS
Automate mitigation workflows with collaborative security across the enterprise
HYBRID MESH FIREWALL
Futureproof your security with unified management for cloud, virtual and on premises firewalls
ZERO TRUST SECURITY
Implement a Zero Trust framework spanning networks, people, devices, data and workloads
Improve Your Security Total Cost of Operation
Lower overall cost by consolidating vendors, reducing the number of breaches and automating administration
- All-inclusive per-annum subscription, with no hidden costs – hardware, software, subscriptions and support
- Lower breach-related costs thanks to proven, highest catch rate
- Spend less resources patching firewalls with our superior product integrity
- Reduce management overhead through automation and AI-based services

CHECK POINT RELATED PRODUCTS/SOLUTIONS
2025 MIERCOM NGFW BENCHMARK REPORT
#1 Catch rate for malware and phishing-Powered threat intelligence and generative AI services
CHECK POINT AI COPILOT
Accelerate administration, ticket resolution and operations with an expert Generative AI assistant
CHECK POINT EVENTS
Automate mitigation workflows with collaborative security across the enterprise
Tighten Your Compliance and Risk Posture
Meet industry regulations, strengthen your risk posture, and prevent more breaches.
- Centrally audit across your digital estate with unified visibility, logging and incident management
- Verify compliance and improve risk posture with dedicated modules for SaaS, IaaS, GenAI and gateways
- Manage external risk arising from supply chains, social media, dark web and more
- #1 catch rate with new threat signals shared globally in less than 2 seconds
- Virtually patch against the latest 3rd party vulnerabilities (CVEs) faster

CHECK POINT RELATED PRODUCTS/SOLUTIONS
EXTERNAL RISK MANAGEMENT
Manage external risk created by supply chains, brand impersonation, the dark web and more
Achieve Better Security with Our Platform Approach
The Check Point Platform is the shared infrastructure that powers Check Point’s network security, cloud security, workspace security, and cross-product security operations.
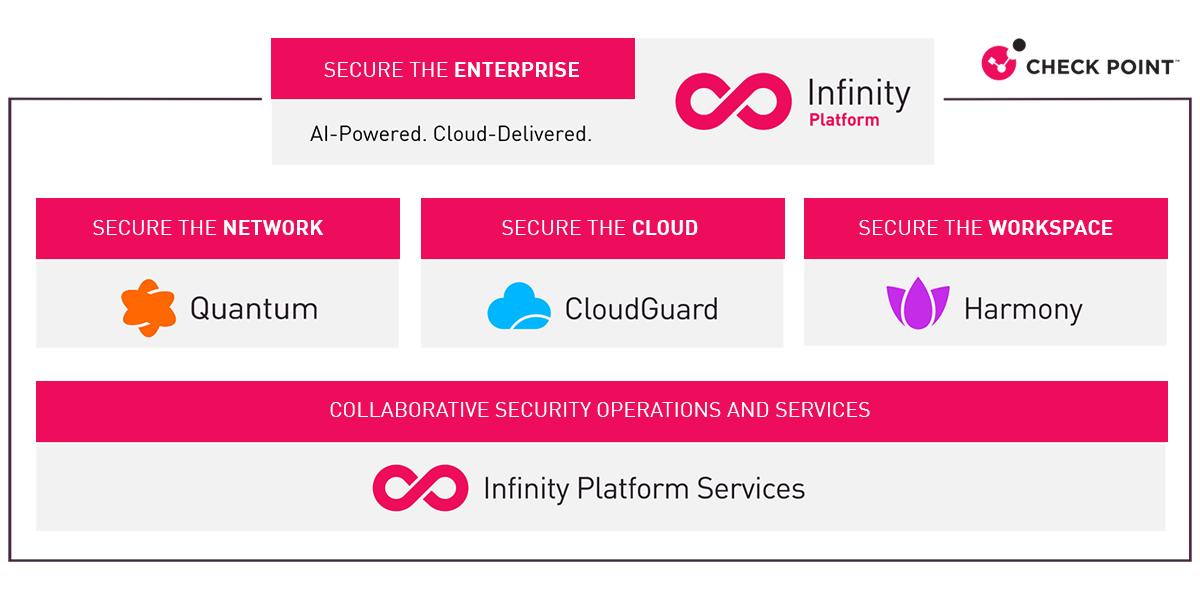
The Four Pillars of the Check Point Platform

Secure the Network
AI-powered threat prevention for securing mesh networks including the data center, perimeter, branch, and remote users.

Secure the Cloud
Prevention-first cloud security from code to cloud.

Secure the Workspace
Comprehensive workspace security, including endpoint, mobile, email, and SaaS applications

Secure Operations
Security operations that span External Risk Management, Extended Prevention and Response (XDR), and more.
Why Choose Check Point?
While other vendors offer a single-logo solution, Check Point has built a truly integrated platform that delivers the #1 catch rate for malware and phishing, sold as a simple, single per-annum subscription

The best security. Period.
Industry’s highest catch rate, leader in product integrity and leader in Zero Trust enablement

The most intuitive interface
One portal to manage it all, most intuitive policy management and support for the broadest set of use-cases

The only license to cover EVERYTHING you need
All-inclusive pricing with no hidden costs – hardware, software, subscriptions and support
Check Point is #1 in blocking threats
Our Customers Love the Check Point Cyber Security Platform
Why do more than 100,000 businesses choose to partner with Check Point?
See how Check Point customers have transformed their IT infrastructure using our advanced cyber security solutions, preventing sophisticated threats across their network, cloud, endpoints, and users. Your success story could be next.
Explore More about the Check Point Security Platform

Check Point Platform Solution Brief
The Check Point Platform is a CISO’s best friend. Learn why.
Explore the Check Point Portal
Signing up takes a minute. Start exploring the platform today.