Check Point Endpoint Security
Check Point Endpoint Security provides comprehensive endpoint protection at the highest level, which is crucial for avoiding security breaches and data compromises.
Check Point achieves 100% detection in the 2024 MITRE ATT&CK® Evaluations
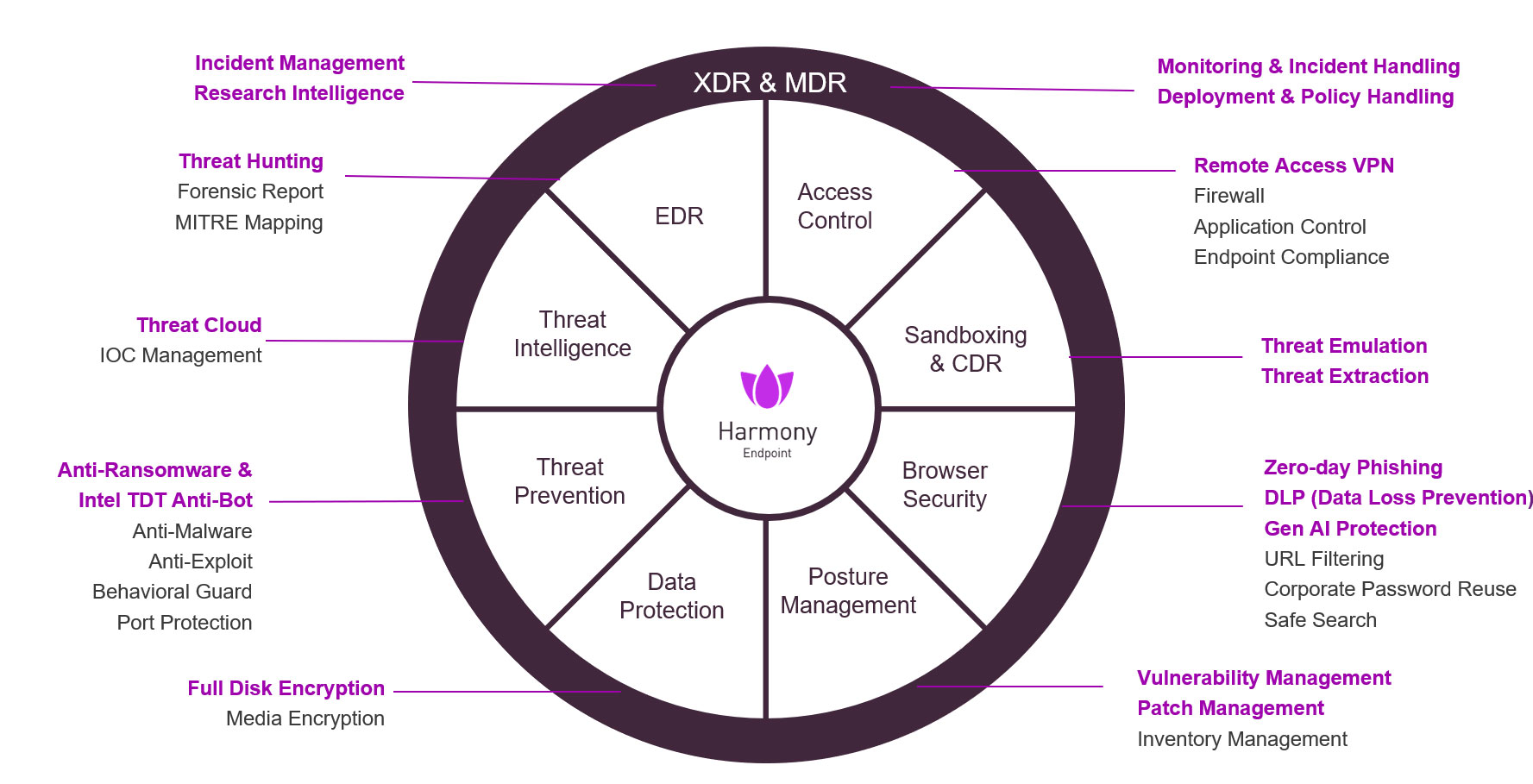
360° endpoint protection with advanced capabilities — all in a single client
Check Point Endpoint Security is a complete and consolidated endpoint security solution with advanced EPP, EDR and XDR capabilities, built to protect the remote workforce from today’s complex threat landscape.
- Single Agent EPP, EDR & XDR, all in a single client and management console.
- Flexible Management With an easy deployment for On-Prem, Cloud, or MSSP Management.
- Extensive OS Support With wide range of supported Operating Systems, including Windows, Mac, Linux, Servers, VDI, Browsers and Mobile Devices
- Threat Intelligence Check Point’s Threat Cloud Al provides Zero-Day protection with more than 60 AI engines.

Unleash secure productivity with Check Point Endpoint Security Data Loss Prevention
with Gen AI tools
360° Endpoint Security
Protects against highly sophisticated threats
Cyberattacks are constantly increasing in volume and sophistication with a 38% rise in the number of cyberattacks year-over-year.

Check Point Endpoint Security protects against the most imminent threats:
- Ransomware & malware protection: Fortifying organizational data against sophisticated ransomware attacks.
- Posture management: Reduce the attack surface with automated vulnerability & patch management.
- Zero-phishing & browser protection: Blocks the most sophisticated phishing attacks with zero impact on end users.
- Data protection: Safeguarding Sensitive Data Loss with advance DLP. Capabilities and unique Full Disc Encryption, to keep valuable data safe and maintain compliance and regulation
Unlock the Power of GenAI with Check Point Endpoint Security
Concerned about your workforce’s use of generative AI tools?
Check Point Endpoint Security uncovers which generative AI tools are used by your workforce, assesses their risk level and applies AI-powered data classification to ensure compliance and data protection.
Secure the Workspace
Keep your users and devices protected. Free up your employees to focus on getting the job done.

Workspace Security Email & Collaboration
Prevents malicious emails from reaching inboxes, guarding against the No.1 attack vector for threat actors.

Check Point Mobile Security
Complete protection across all mobile attack vectors, including SMS
Keep your corporate data safe by securing mobile devices across all attack vectors: apps, files, network, and OS

Check Point SASE
2x faster internet security
Simplified, unified SASE management and threat prevention
Experience the power and simplicity of Workspace Security
Explore More About Check Point Endpoint Security

Securing Data in the AI Era with Workspace Security DLP
AI revolutionizes work. Check Point Workspace Security DLP ensures security while embracing productivity in this new era.
Auto Detect, Prioritize & Patch Vulnerabilities
Learn how Check Point Endpoint Security automatically detect vulnerabilities and remediate those weaknesses, enterprise-wide, in a single click.
FAQ
Check Point Endpoint Security is Check Point’s advanced endpoint protection solution designed to secure laptops, desktops, and servers against the most imminent cyber threats, including ransomware, malware, and phishing attacks.
Check Point Endpoint protects a wide range of endpoints, including Windows and macOS laptops, desktops, and servers, ensuring comprehensive coverage for both on-premises and remote work environments.
Check Point Endpoint uses multiple layers of defense:
Anti-Ransomware & Anti-Malware: Detects and blocks sophisticated ransomware and malware attacks.
Zero-Phishing: Prevents access to known and unknown phishing sites.
Behavioral Guard: Identifies file-less attacks and malicious behaviors before they cause harm.
No. Check Point Endpoint can operate independently without constant cloud connectivity, while still offering cloud-based management options for centralized visibility and control.
Check Point Endpoint integrates seamlessly with Check Point’s broader security architecture, including network, cloud, and mobile security solutions, enabling unified policy management and threat intelligence sharing across all environments.
Check Point Endpoint offers centralized dashboards for real-time visibility, detailed threat analytics, compliance reporting, and automated alerts, helping organizations monitor endpoint health and respond quickly to incidents.