Security Compliance:
Your Automated Trusted Advisor
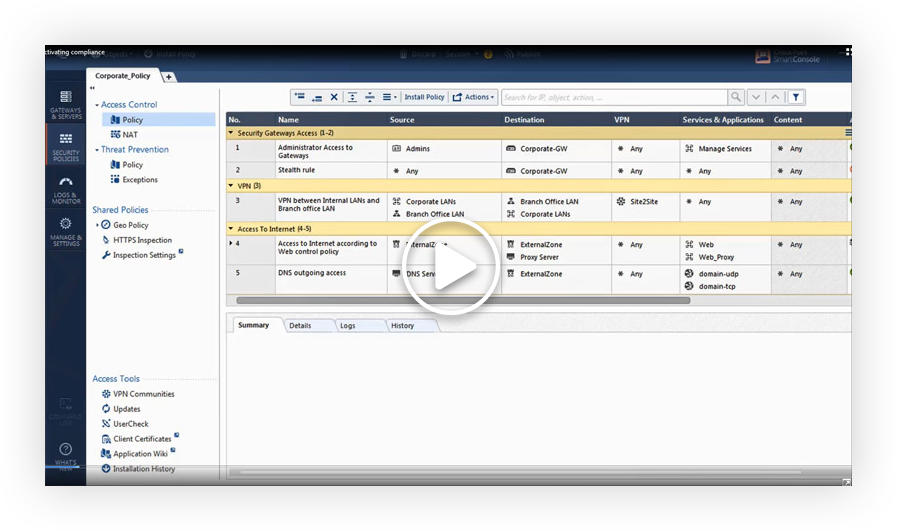
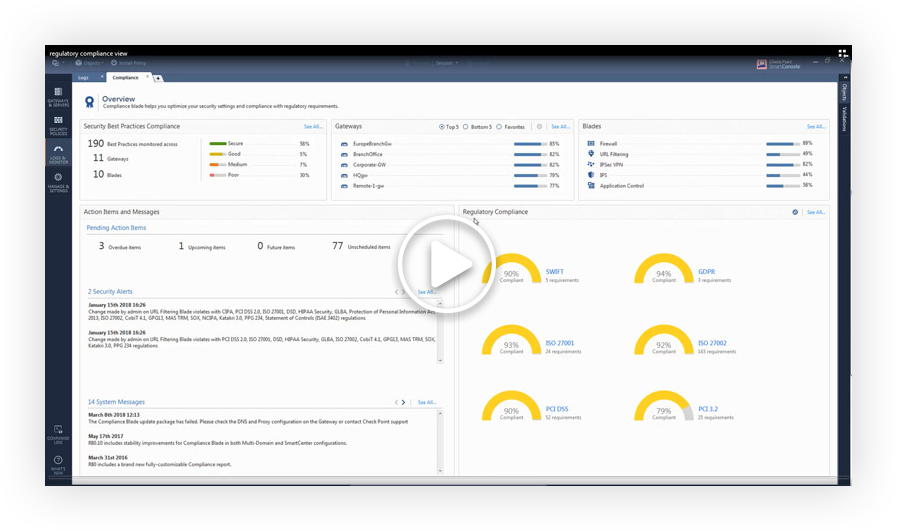
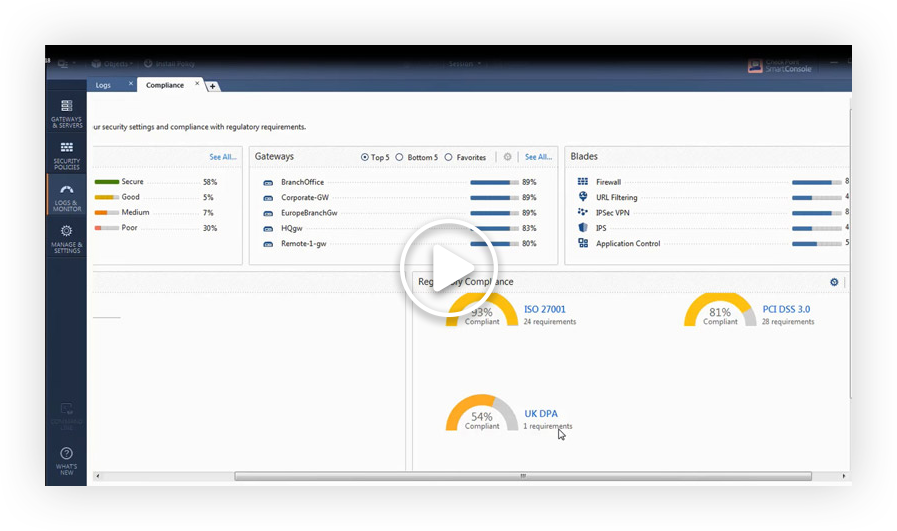
Boost your security level across your entire Check Point environment with a dynamic security compliance solution that continuously monitors your security infrastructure, gateways, blades, policies and configuration settings all in real time.
REQUEST A DEMO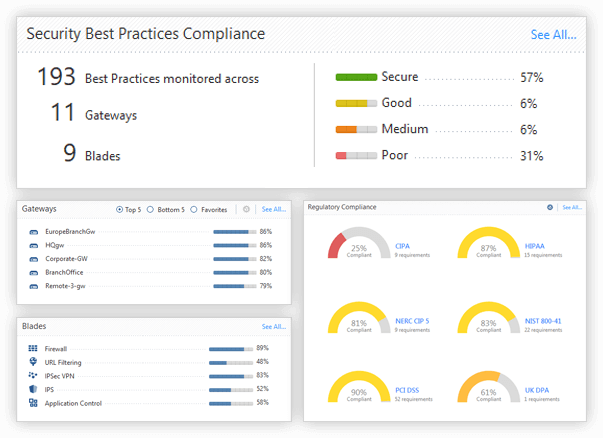
![]()
Increased Security
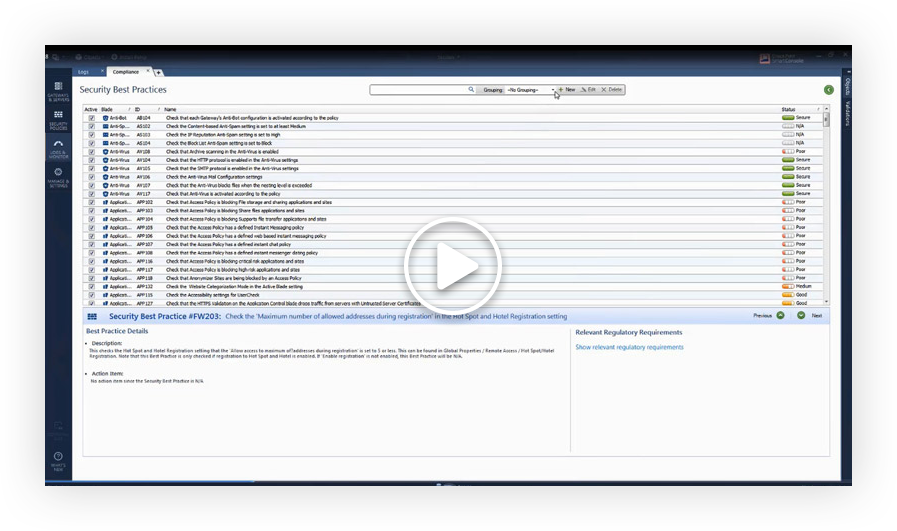
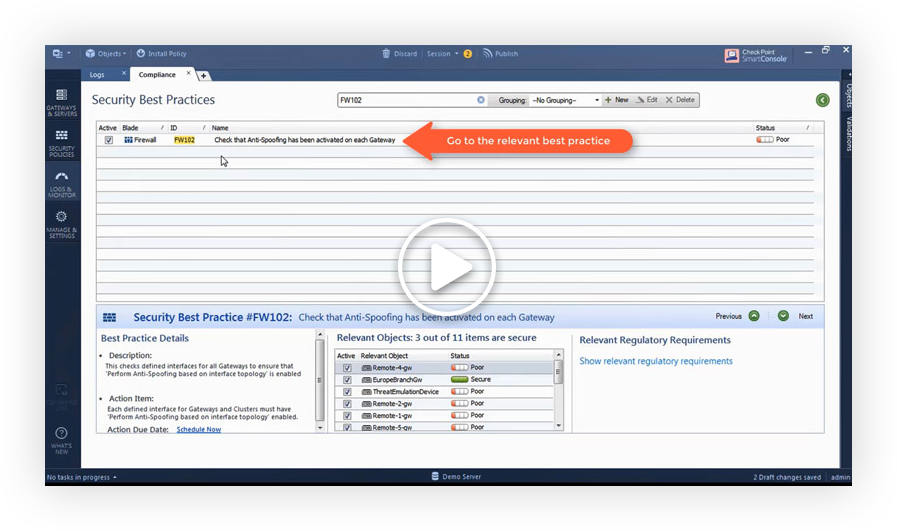
Detects poor configurations against 300+ Check Point Security Best Practices
![]()
Avoiding Human Error
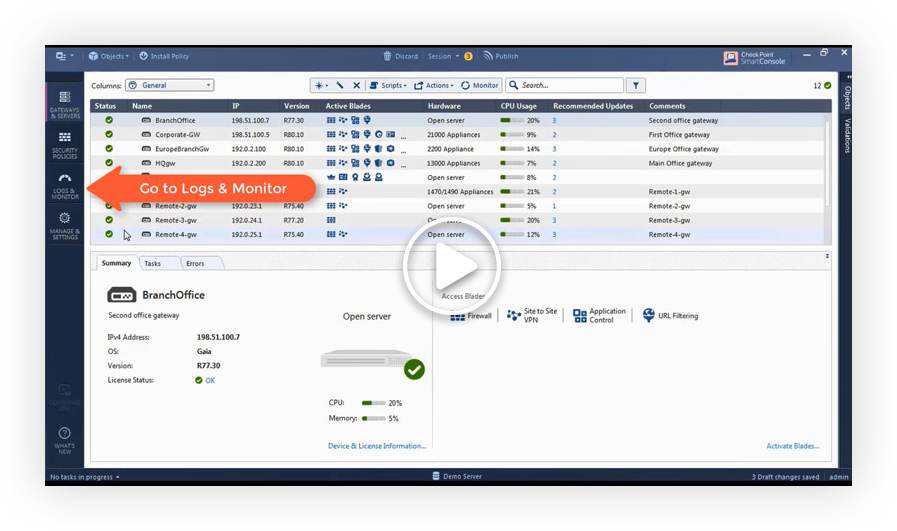
Monitor policy changes in real time, providing instant alerts and remediation tips
![]()
Security Compliance
Translates thousands of complex regulatory requirements into actionable security best practices
Feature Specifications
Featured Customers
Our Customers Love Us
Versatile Security Protection –Like A Swiss Army Knife For Security
Checkpoint Next Generation Firewall proves to be a great solution for our small business infrastructure. R80 Security Management has allowed our company to easily (and significantly) improve our protections over time. read more >
CheckPoint Next Gen FW, The Best Way To Protect A Corporation Against The Latest Threats
Our experience with CheckPoint has been very satisfactory for the advanced security approach, being able to provide our corporation with the latest generation security mechanisms and being able to have maximum control and visibility of our perimeter security. read more >
Apple In The World Of Firewalls
The Check Point Next Generation Firewall is like Apple in the world of Firewall and Security. It is an old, but still modern and competitive solution, and Check Point is always on the edge of security technologies. read more >
2023 Cyber Security Report
Geo-political conflicts trigger all-time high for cyberattacks.
See more trends and insights.