Autonomous IoT Security Solution that Prevents Network & Device Attacks
Using Internet of Things (IoT) devices across enterprises, healthcare, and industrial applications delivers productivity benefits, but it also exposes you to evolving cyber threats.
From IP cameras, and smart elevators, to medical devices and industrial controllers, Check Point IoT Protect secures your company against IoT network and on-device cyber attacks.
Check Point IoT Protect
AUTONOMOUS PREVENTION. NETWORK AND ON-DEVICE PROTECTION.
Automatically identifies and maps IoT devices and assesses the risk, Prevents unauthorized access to and from IoT/OT devices with zero-trust profiling and segmentation, Blocks zero-day IoT attacks with industry leading threat intelligence, 300+ IPS signatures and on-device run-time protection.
![]()
Autonomous Zero Trust Protection
Autonomously analyze, map and protect devices with zero trust profiles
![]()
Prevent Network IoT Attacks
Block zero-day attacks with virtual patching and real-time IoT threat intelligence
![]()
On-Device Run-Time Protection
Harden device firmware to prevent zero-day run time attacks
Are Your IoT Devices Secure?
Think Again
The first two months of 2023 have seen a 41% increase in the average number of weekly attacks per organization targeting IoT devices, compared to 2022 (CPR).
In this paper, we explore some of the common security vulnerabilities associated with IoT devices, an example of a real use case, and how you can best keep those devices protected from cyberattacks.
DOWNLOAD NOW
Modern Challenges for IoT Security
Once compromised, cyber criminals can move freely to access more critical applications and sensitive data. They can hold this information for ransom, potentially shutting down the business network in the process. A comprehensive IoT security solution is needed to protect your business from these risks and is a vital component of every company’s cybersecurity strategy. Learn how you can protect your business in this informative e-book.
Making IoT Simple, Effective and Valuable for Any Organization
With 63% of enterprises, 92% of industrial and 82% of health care organizations using IoT, there are large numbers of unmanaged IoT devices connected to the network. Each of these IoT devices is an entry point for hackers, making almost every company vulnerable to cyber-attacks.
Learn how IoT Protect Autonomous Network and On-Device Protection can:
- Autonomously analyze IoT risk and protect IoT device with zero trust profiles
- Block zero-day attacks with virtual patching and real- time IoT threat intelligence
- Harden IoT device firmware to prevent zero-day run time attacks
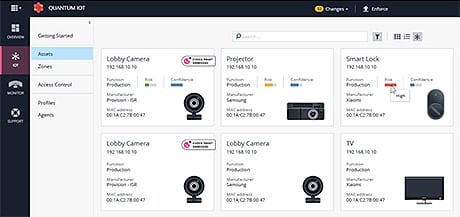
IoT Discovery & Risk Analysis
Automatically map, profile and assess device risk levels
Real-time risk analysis based on IoT networks discovery, firmware risk assessment and threat intelligence.
From a single console, view all your IoT devices classified based on their risk level. You can even drill down for a risk analysis per device.
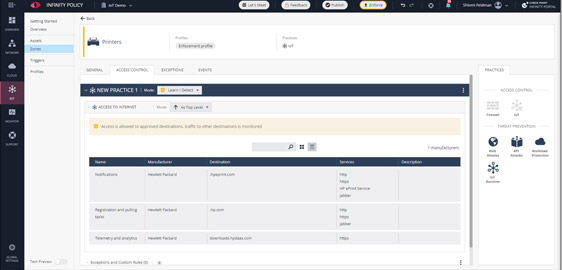
Zero-Trust Profiles
Automatically minimize attack surface
- Prevent unauthorized access and malicious intent from reaching IoT devices
- Prohibit infected devices from moving laterally and accessing malicious sites
- Auto-generated policies: Minimize your risk exposure and save months of manual policy configurations
- See and control over 1,500 IoT/OT
protocols & commands
IoT Threat Prevention
Block Known and Zero-Day IoT Related Attacks
![]()
IoT-specific Threat Intelligence
Stay ahead of the latest IoT threats with threat intelligence shared between 100 million endpoints, gateways and IoT devices worldwide.
![]()
Virtual Patching
Protect vulnerable devices from known exploits, without the need to physically patch them. Over 300 prevention signatures against network-based IoT attacks.
On-device Runtime
Self-Protection
Mitigate device level attacks before devices are compromised with the IoT Nano-Agents.
IoT Device Security Solution for Manufacturers
Get a powerful last line of defense for connected devices with on-device firmware-security
Embedded device manufacturers seek to offer customers devices that are secured against cyber threats arising from 3rd party supply-chain components, outdated firmware, newly discovered firmware CVEs and state-sponsored backdoors.
To gain and instill confidence in customers, manufacturers need firmware-specific risk visibility and on-device runtime protection that blocks firmware attacks as they happen in real time.
Tailored for Any IoT Environment
Protect thousands of IoT devices across smart office, smart building, healthcare and industrial environments.

Enterprise IoT

Healthcare IoT

Industrial IoT

IoT Manufacturers
Tight Integration with Leading IoT Discovery Platforms
Check Point IoT Protect leverages a powerful Check Point IoT Protect API, providing a secure and dependable foundation for your IoT ecosystem. At Check Point, we forge strategic partnerships with leading IoT discovery vendors, empowering us to deliver state-of-the-art discovery capabilities that cater to specific market sectors such as healthcare, industrial, and critical infrastructure.
Innovative Partnerships with Industry-Leading Device Vendors
From IP cameras and smart elevators, to routers, medical devices and industrial controllers, Check Point provides on-device runtime protection against zero-day cyber attacks – serving as the most powerful line of defense for device manufacturers, enabling them to produce “Secure by Design” devices.
Ready to Experience Check Point IoT Protect?
Try it Now
Talk to a Specialist
Get Pricing
Our Customers Love Us
Versatile Security Protection –Like A Swiss Army Knife For Security
Checkpoint Next Generation Firewall proves to be a great solution for our small business infrastructure. R80 Security Management has allowed our company to easily (and significantly) improve our protections over time. read more >
CheckPoint Next Gen FW, The Best Way To Protect A Corporation Against The Latest Threats
Our experience with CheckPoint has been very satisfactory for the advanced security approach, being able to provide our corporation with the latest generation security mechanisms and being able to have maximum control and visibility of our perimeter security. read more >
Apple In The World Of Firewalls
The Check Point Next Generation Firewall is like Apple in the world of Firewall and Security. It is an old, but still modern and competitive solution, and Check Point is always on the edge of security technologies. read more >