IoT Device Security for Manufacturers
If you build embedded consumer and Internet-of-Things (IoT) devices, the expanding threat landscape requires you to protect your customers from cyber attacks with out-of-the-box firmware security.
From IP cameras and smart elevators, to routers, medical devices and industrial controllers, Check Point IoT Embedded provides on-device runtime protection against zero-day cyber attacks – serving as the most powerful line of defense for your IoT devices.
REQUEST A NANO AGENT DEMOCheck Point IoT Embedded
ASSESS. HARDEN. CONTROL.
Revolutionary on-device runtime protection enables you to develop connected IoT devices with built-in firmware security that defends
against the most sophisticated cyber attacks.
![]()
Assess Risk
Uncover security risks in your
IoT firmware
![]()
Harden
Harden device with on-device runtime protection to prevent zero-day attacks
![]()
Control
Define and enforce policies per device for ongoing network access
Understanding IoT Security Regulations
As your organization’s cyber security executive, you have witnessed firsthand the unprecedented growth of IoT devices in your organization. For many of these devices, security of the device and its data are often underwhelming; promoting active security risks, including Denial of Service attacks, malware, ransomware, and DNS spoofing.
Download this paper to learn about the recent IoT security regulations, why it should matter to you, and how to best prepare in the fight against these sophisticated cyberattacks.
DOWNLOAD NOW

IoT Security Guide: Challenges and Solutions
Prevent and combat cyber attacks on your
networks and devices.
Modern Challenges for IoT Security
Once compromised, cyber criminals can move freely to access more critical applications and sensitive data. They can hold this information for ransom, potentially shutting down the business network in the process. A comprehensive IoT security solution is needed to protect your business from these risks and is a vital component of every company’s cybersecurity strategy. Learn how you can protect your business in this informative e-book.

“Check Point IoT Protect Nano Agent gives us a robust, end-to-end security
solution for our customers. Provision-ISR cameras will have next-generation
cybersecurity provided right out of the box, with plug-and-play implementation.”
– Yonatan Pick, Chief Technology Officer, Provision-ISR
How Firmware Security Prevents Real Exploits
Watch How Embedded Security Works
- Router firmware is compromised by a known vulnerability
- Once overtaken, a network scan reveals other assets, including an IP camera, which the attacker exposes to the internet
- Check Point IoT Protect™ Nano Agent® is installed
- The same router vulnerability is blocked by the Nano Agent® and can no longer be exploited
Uncover IoT Device Security Risks
Check Point IoT Embedded Risk Assessment
When it comes to firmware security, the risks are numerous – from 3rd party supply-chain components, to outdated firmware to state-sponsored backdoors and other vulnerabilities.
As a first step to offering IoT devices that are secure out-of-the-box, IoT manufacturers need to understand their firmware’s real-time security posture so they can identify any gaps and fix them.
Sign up for a free automated firmware risk assessment to uncover the inherent risks in your device, and obtain a comprehensive report that includes quick mitigation steps.
GET A FREE IOT FIRMWARE RISK ASSESSMENT
Prevent Attacks with On-Device Runtime Protection
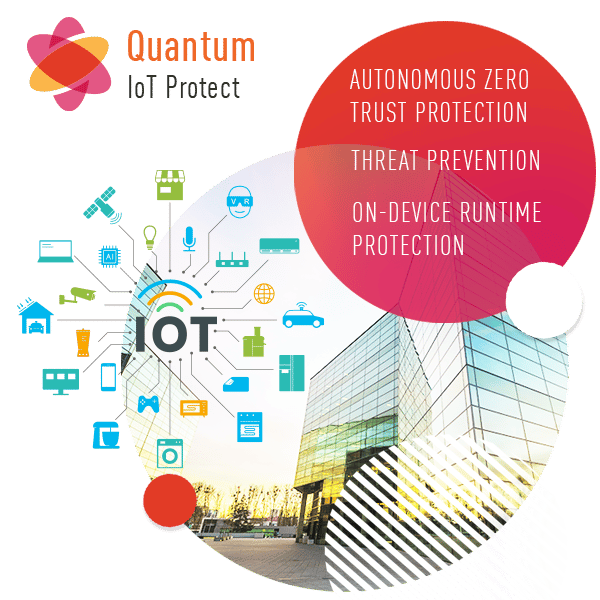
Revolutionary Check Point IoT Protect™ with Nano Agent® provides on-device runtime protection enabling connected devices with built-in firmware security. Based on cutting edge control flow integrity (CFI) technology, the lightweight Check Point IoT Protect™ with Nano Agent® allows you to fend off the most sophisticated device attacks, including shell injections, memory corruption, control flow hijacking and even zero-day firmware vulnerabilities that have yet to be discovered.
REQUEST A NANO AGENT DEMODeploy Firmware Security in Three Steps: Assess
Risks, Harden and Control
Firmware security offers the tightest protection and strongest line of defense for your IoT device.
Learn the risks associated with IoT devices, what defense-in-depth measures can be taken to secure IoT ecosystems, and why firmware security is critical.
DOWNLOAD THE WHITE PAPERManage IoT Device Security from
the Cloud with Check Point
Define and Enforce Policies for Devices Secured by the
IoT Protect Nano Agent
Management API
- Open Management API available on swagger.io
- Supports internet-connected devices and devices in air-gapped environments
Define and Enforce Policies
- Control IoT network communications to and from the device
- Set security practices for devices protected by the Nano Agent®
Define and Enforce Policies
- Full reporting, logging and alerting
- Easily integrate with leading SIEMs
- Unified console for IT and IoT device-level management
Check Point Uncovers IoT Device
Vulnerabilities
Vulnerabilities
Check out original IoT device security research and commentary from Check Point:
Ready to Experience Check Point IoT Protect?
Try it Now
Talk to a Specialist
Get Pricing
2023 Cyber Security Report
Geo-political conflicts trigger all-time high for cyberattacks.
See more trends and insights.