Check Point Intrusion Prevention System (IPS)
Intrusion Prevention Systems detect or prevent attempts to exploit weaknesses in vulnerable systems or applications, protecting you in the race to exploit the latest breaking threat. Check Point IPS protections in our Next Generation Firewall are updated automatically. Whether the vulnerability was released years ago, or a few minutes ago, your organization is protected.
REQUEST A DEMO![]()
![]()
Secure
Check Point IPS delivers thousands of signature and behavioral preemptive protections
![]()
Efficient
Our acceleration technologies let you safely enable IPS. A low false positive rate saves your staff valuable time
![]()
Unified
Enable IPS on any Check Point security gateway reducing Total Cost of Ownership
Product Specifications
IPS Detects and Prevents:
- Specific known exploits
- Vulnerabilities, including both known and unknown exploit tools
- Protocol misuse which may indicate potential threats
- Tunneling attempts that may indicate data leakage
- Outbound malware communications
Timely IPS Updates
Real-Time Protections: IPS is constantly updated with new defenses against emerging threats. Many of the IPS protections are pre-emptive, providing defenses before vulnerabilities are discovered or exploits are even created.
Microsoft Vulnerability Coverage: Check Point is ranked #1 in Microsoft threat coverage, including preemptive protections against emerging vulnerabilities and exploits.
Virtual Patching
Patching is an incomplete security measure, which can leave your network open for attack. By taking a more comprehensive approach, which combines robust IPS functionality with a concerted patching strategy, network administrators can better equip themselves to handle ‘Patch Tuesdays’ and secure the network between upgrades and patches.
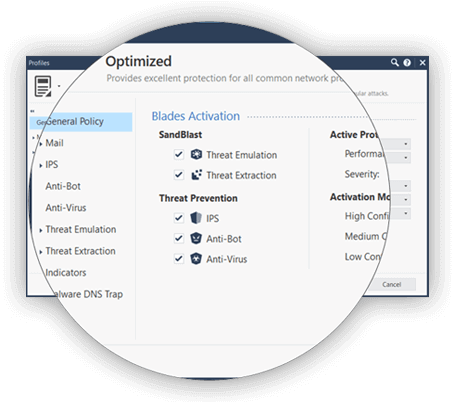
Efficient and Flexible Deployment
- Predefined recommended profiles allows out-of-the-box use and are tuned to optimize security
- Define signature activation rules that match the security needs of your network assets
- Optional detect-only mode sets all protections to only detect to allow you to evaluate your profile
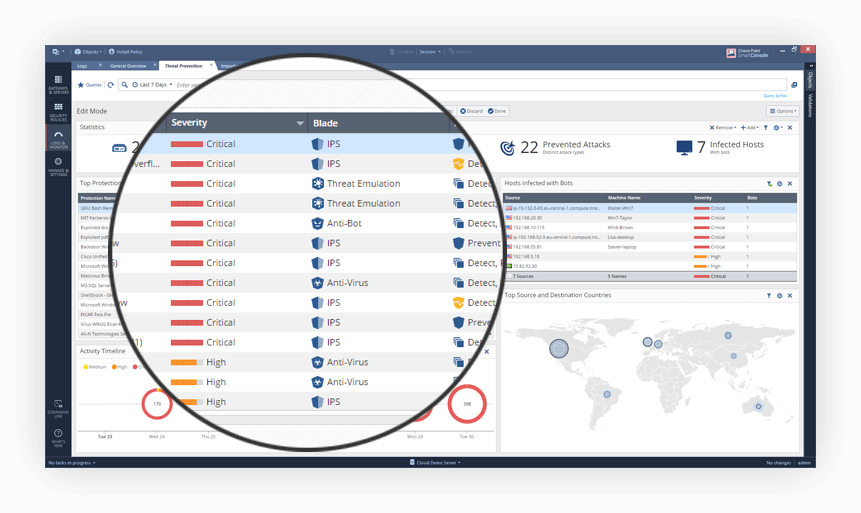
360° Visibility and Reporting
Achieve an unmatched level of visibility to detect and prevent threats. Check Point IPS seamlessly integrates with SmartEvent, enabling SOC (Security Operations Center) staff to respond to the highest priority events first, saving them time.
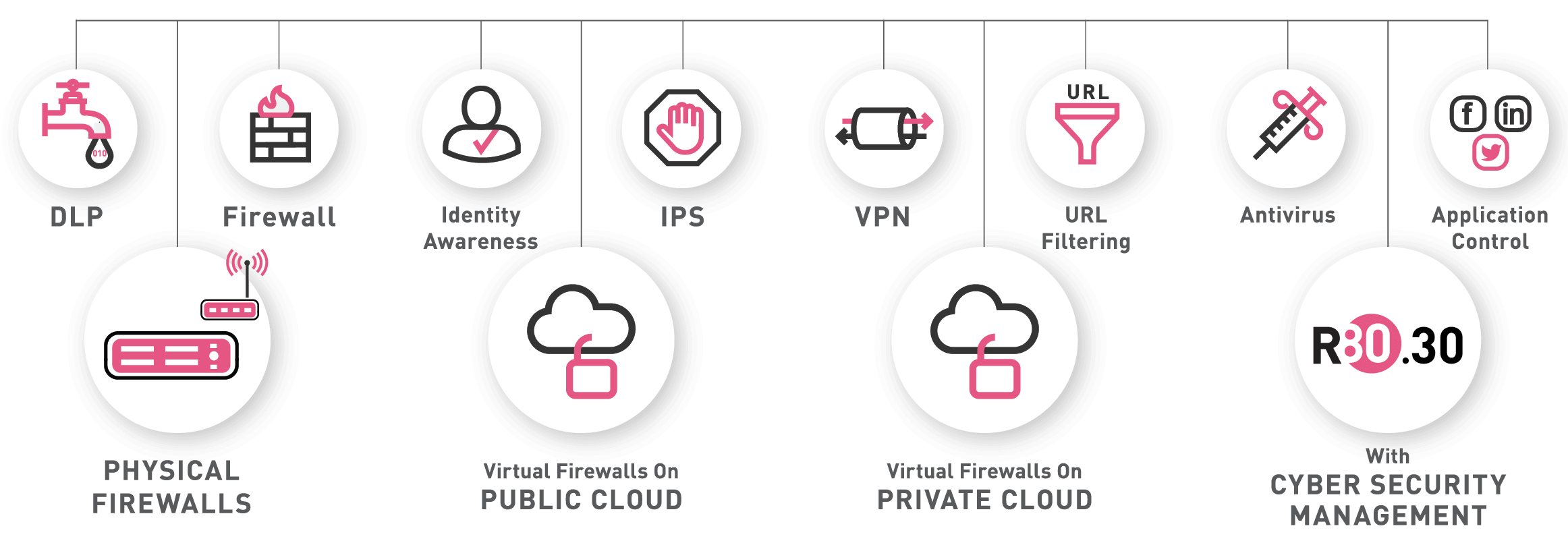
Our Next Generation Firewall Is
More Than Just a Firewall
2023 Cyber Security Report
Geo-political conflicts trigger all-time high for cyberattacks.
See more trends and insights.

