Whether you currently support a remote workforce or you find yourself preparing to support one, we are here for you. CONTACT US HERE
Secure Mobile Access
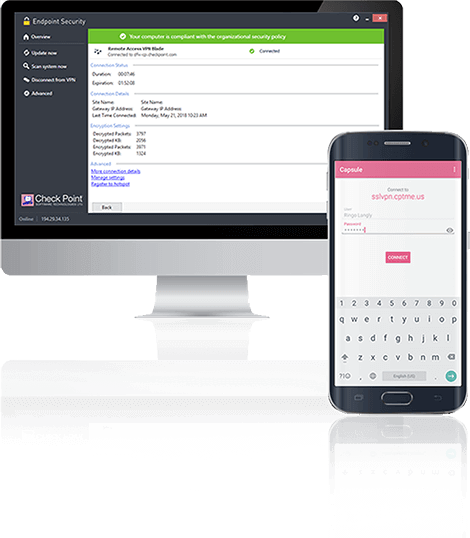
Check Point Mobile Access is the safe and easy solution to securely connect to corporate applications over the Internet with your Smartphone, tablet or PC. Integrated into the Check Point Next Generation Firewalls (NGFW), Mobile Access provides enterprise-grade remote access via both Layer-3 VPN and SSL/TLS VPN, allowing you to simply and securely connect to your email, calendar, contacts and corporate applications.

![]()
Flexible
Easy access for mobile workers – simply connect from mobile devices to secure connectivity for smartphones, tablets, PCs and laptops
![]()
Secure
Communicate securely with proven encryption technology, two-factor authentication, and User-Device pairing to eliminate network security threats
![]()
Integrated Security
Integrated in Next Generation Firewalls enables consolidation of security controls decreasing costs
Product Specifications
Remote Access with Encrypted VPN Technology
Check Point Mobile Access uses SSL/TLS VPN and IPsec technologies to secure encrypted communication from unmanaged Smartphones, tablets, PCs, and laptops to your corporate IT infrastructure. Mobile Access offers:
- Secure SSL VPN access
- Two-factor authentication
- Device/end-user paring
- Mobile business portal
- Provisioning of security features and email profile
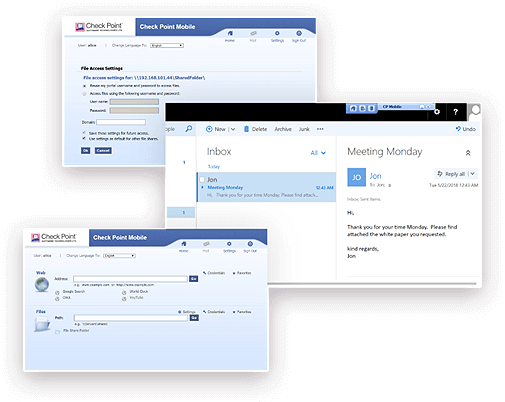
SSL/TLS Web Portal
The SSL/TLS VPN portal is best for connecting securely to corporate resources through a portal from a web browser.

Secure Authorization
Mobile Access can be configured to send a One-Time Password (OTP) to an end-user communication device (such as a mobile phone) via an SMS message. Or even with SMS two-factor authentication providing an extra level of security while eliminating the difficulties associated with managing hardware tokens.
A Next Generation Firewall for Any Deployment
Implement Zero Trust Security
![]()
Security teams must be able to isolate, secure, and control every device on the network at all times. Check Point solutions provide you with the ability to block infected devices from accessing corporate data and assets, including employees’ mobile devices and workstations, IoT devices and Industrial Control Systems. Integrated into the Check Point Architecture, Mobile Access secures connections to corporate applications over the Internet with your Smartphone, tablet or PC.
Interested in Mobile Security?
You Should Be.
Almost every organization experienced a mobile-related attack in 2020.*
Check out Check Point’s dedicated Mobile Threat Defense solution.
LEARN MORE*Check Point 2021 Mobile Security Report

Harmonize Security for Users, Devices & Access
Best Prevention. Simple for Everyone.
Protecting today’s hyper-distributed workspace requires endless security functions across user devices, applications and networks. However, stitching together point solutions often leaves security gaps and creates a cumbersome infrastructure that is difficult to manage and scale. Workspace Security offers an alternative that saves you the overhead and increases security.
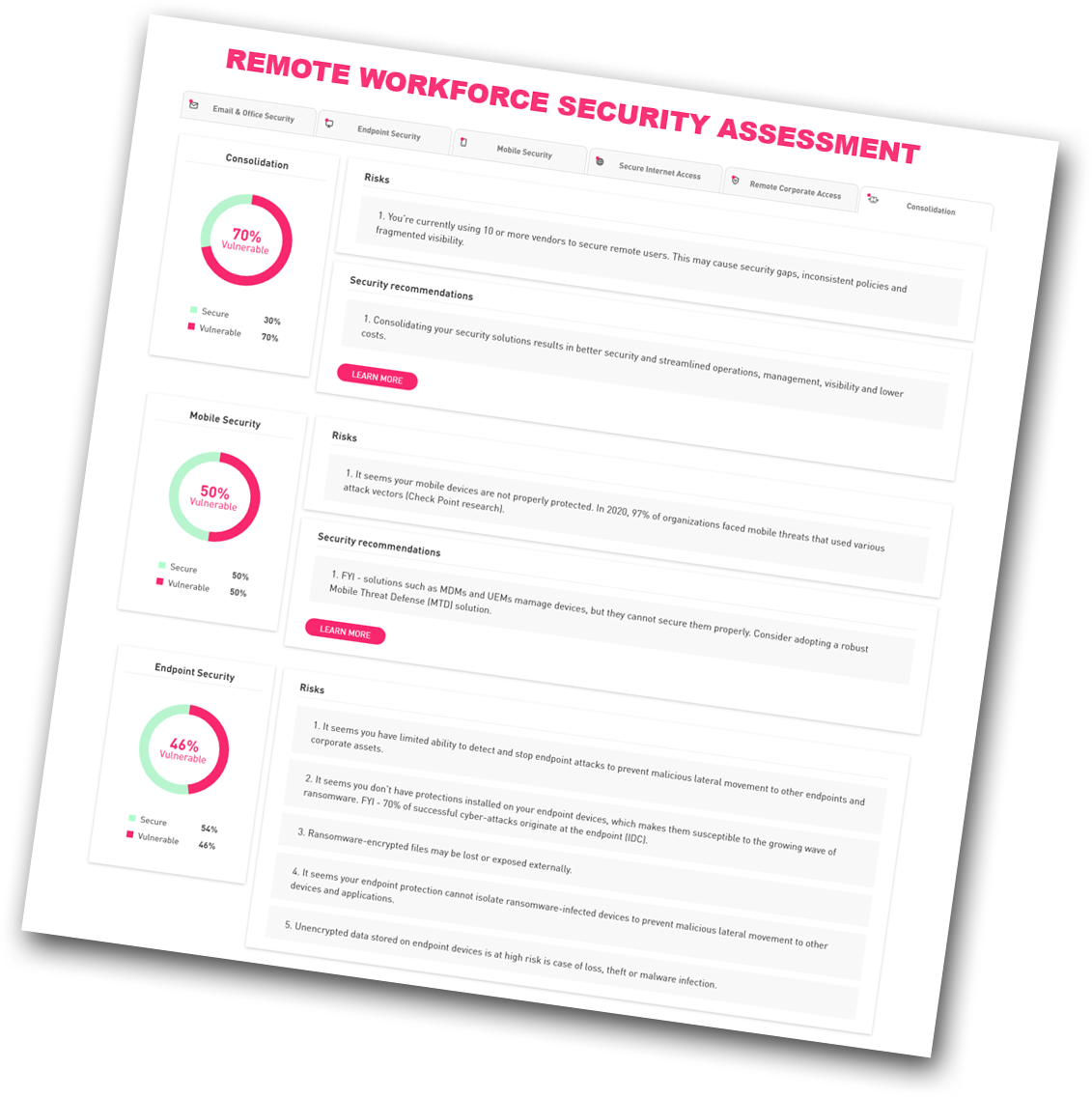
Find Your Security Gaps in 5 Minutes
Take our online remote workforce security assessment to understand your organization’s security gaps and how to close them, including insights into your:
- Endpoints’ resilience to ransomware
- Internet access risk exposure
- Remote access strategy strength
- Office 365 and G Suite protection level
- Vulnerability to mobile-related attacks