Industrial Control Systems (ICS) Security
Enhancing the security of Industrial Control Systems (ICS) presents distinctive challenges for companies. Ensuring service uptime, preserving data integrity, complying with regulations, and safeguarding public safety necessitate proactive security measures to protect these mission-critical assets.
Securing ICS requires comprehensive discovery and visibility of the system, followed by the implementation of targeted and appropriate security measures.
REQUEST A DEMO SOLUTION BRIEFCheck Point is a Leader in the 2022 Gartner® Magic Quadrant™ for Network Firewalls
DOWNLOAD REPORT
![]()
Transportation
![]()
Oil
![]()
Manufacturing
![]()
Energy
![]()
Utilities
![]()
Smart Cities
Strengthen the Security of your ICS and Operational Technology (OT) Environments
The industrial attack surface is continuously expanding due to various reasons, including nation-state actors, technology advances, IT-OT convergence and more.
The Check Point ICS security solution offers a proactive strategy, minimizing risk across both environments, blocking threats before critical assets are affected, and enhancing industrial operations seamlessly.

“With Check Point Rugged Firewall Security Gateways, we built
security capabilities into our most important facilities, in a swift,
agnostic way. Our project demonstrates the value of choosing the
right partner.”
– Nuno Medeiros, CISO, E-REDES

Check Point Rugged Firewall
Security Gateways
Secure. Built for OT. Rugged.
The NEW Check Point Rugged Firewall 1595R security gateways deliver industry-leading threat prevention, integrated AI security, secure 5G connectivity and more to protect ICS for manufacturing, energy, utilities, and transportation.
LEARN MOREIntroducing the Check Point Rugged Firewall 1595R Security Gateway
Uncompromised IT & OT Security
The Check Point Rugged Firewall 1595R empowers key industries for an ‘Industry 4.0 future with harsh environment resilience, 400Mbps threat prevention, advanced OT discovery/segmentation, high-speed secure 5G connectivity at 1Gbps, and support for 1,830 SCADA and ICS protocols & commands.
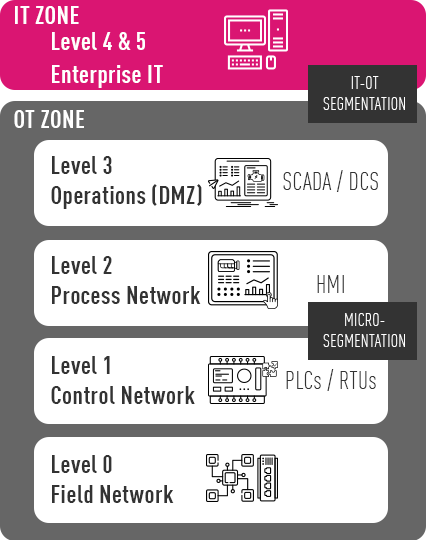
WATCH THE VIDEOIT/OT Network Segmentation
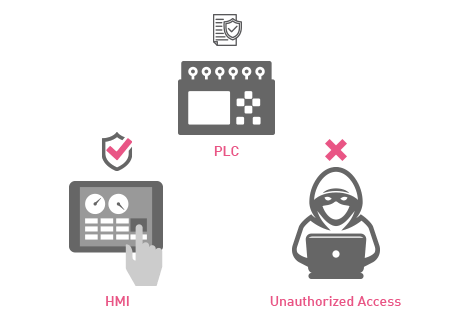
Check Point Next-Generation Firewalls, available as physical or virtual appliances, provide boundary protection between the IT and the OT network and micro segmentation among product lines and departments on the shop floor.
With granular visibility into SCADA protocols and commands, these firewalls provide access control throughout the OT environments.
Secure OT Assets
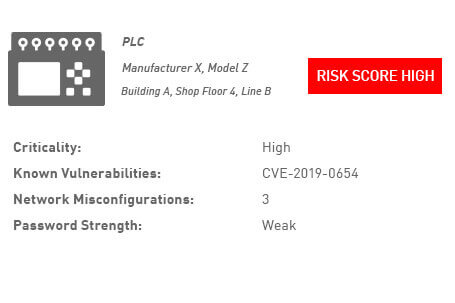
OT Asset Discovery and Visibility
Passively monitor OT networks to discover asset types, risk, attack vector and baseline behavior
From a single console, view all assets classified based on their risk level and drill down for a risk analysis per asset.
Auto-generated Policy Recommendations
Instantly minimize your risk exposure
Save months of manual policy configurations and ensure your OT assets are secure from the first moment they connect to the network.
- Ensure systems use only communication protocols they were designed to use
![]()
Virtual Patching
Blocks attacks before they reach critical assets
Protect vulnerable ICS components from known exploits, without the need to physically patch them. Almost 200 prevention signatures against OT related attacks.
Threat Prevention for IT
Many of the recent attacks on OT and ICS networks were found to be based on IT attack vectors, such as spear phishing, Endpoint and Ransomware. Using Check Point Threat Prevention solutions, such as SandBlast, Endpoint, IPS and others will prevent and eliminate those attacks prior to breaching the ICS equipment.
Advanced Network Threat Prevention
Mobile Security
Advanced Endpoint Threat Prevention

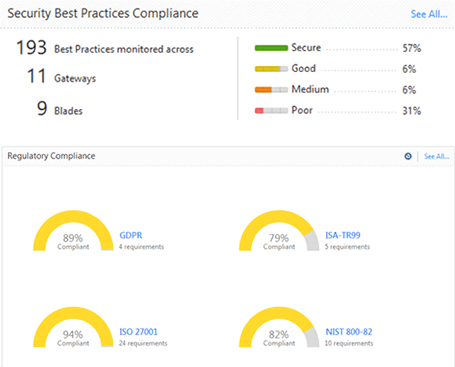
Maintain Regulatory Compliance
As governments worldwide issue new guidelines to enhance the security of critical infrastructures, regulatory compliance pressure is increasing.
Check Point Security Compliance, part of Check Point Unified Security Management, lets you improve security practices, safeguard data, and maintain compliance with regulations such as NERC CIP, NIST SP800-82, ISA-TR99, IEC 62443.
LEARN MORE ON COMPLIANCE