A Holistic Zero Trust Approach in an Evolving Threat Landscape
With the Check Point Platform, organizations can embrace the principles of Zero Trust and leverage a consolidated security platform that covers your entire environment, from network and cloud to workspaces and devices
Check Point named a leader in the 2025 Gartner Magic Quadrant for Hybrid Mesh Firewalls.
Implementing a Zero Trust Security Framework With Cross-Environment Policy Application
The Check Point Platform provides comprehensive capabilities to implement Zero Trust across your environment form a unified, integrated security architecture.
Simplified Deployment and Management
Disparate technologies can create security gaps in Zero Trust implementations. Consolidate your Zero Trust security under a single pane of glass to streamline deployment and ongoing administration.
The Result
Centralized security management gives unified visibility into all users, devices, and traffic. This enhanced awareness supports more informed, risk-based decisions that continuously verify trust.
Proactive Enforcement Across All Assets
Apply the same Zero Trust policies and controls uniformly to users, devices, applications, and data – whether on-premises, in the cloud, or in hybrid environments.
The Result
Quickly deploy policies across environments with Check Point Platform. Benefit from deep security intelligence and multilayered defenses that enhance awareness, support better decision-making, and provide proactive protection against the latest threats.
A Single Consolidated Absolute Zero Trust Security Architecture
Check Point Platform provides a unified cybersecurity architecture that streamlines industry-critical security capabilities — including next-generation firewalls, advanced threat prevention, and secure access solutions under a single pane of glass.
Zero Trust Networks
Don’t let your network be a playground for cyber threats. By “Dividing and Ruling” your network, you can dramatically reduce the risk of lateral movement and safeguard your most valuable assets. Set and enforce a “Least Privileged” access policy so that only the right users and devices can access your most valuable assets.
- By leveraging a Zero Trust Network Access (ZTNA) policy, connect users, sites, clouds, and resources with a high- performance, private global backbone.
- Security Gateways empower you to create granular network segmentation across your public/private cloud and LAN environments.

CHECK POINT RELATED PRODUCTS/SOLUTIONS
ZTNA-AS-A-SERVICE
Boost remote access security with granular zero trust policies and network segmentation
Zero Trust Devices
Security teams must be able to isolate, secure, and control every device on the network at all times. Check Point solutions enable organizations to block infected devices from accessing corporate data and assets, including employees’ mobile devices and workstations, IoT devices, and Industrial Control Systems.
- Protect employees’ mobile devices and workstations from advanced attacks, zero-day malware, malicious app installation, and more.
- Automatically discover and protect smart office and building devices, Industrial Control Systems (ICS), and medical devices.

CHECK POINT RELATED PRODUCTS/SOLUTIONS
MOBILE SECURITY
Detect both known and unknown threats to provide complete mobile threat prevention.
IOT SECURITY
Minimize your exposure to the IoT cyber risk and prevent the next cyber attack.
ICS SECURITY
Specialized ICS/SCADA security technology, ruggedized gateways and 5G connectivity
Zero Trust People
With 81% of data breaches involving stolen credentials, traditional username and password-based authentication is no longer sufficient. Check Point’s Identity Awareness solution ensures that access to valuable data is granted only to authorized users after their identities have been strictly authenticated.
- Process includes Single Sign-On, Multi-Factor Authentication, context-aware policies (e.g., time and geo- location of the connection), and anomaly detection.
- Enhance identity-centric access control by applying least privileged access to any enterprise resource, accommodating both internal and external identities.

CHECK POINT RELATED PRODUCTS/SOLUTIONS
IDENTITY AWARENESS
Access control of users, firewalls, apps, cloud, and more in a single console.
ZTNA-AS-A-SERVICE
Boost remote access security with granular zero trust policies and network segmentation.
EMAIL SECURITY
Block the no. 1 attack vector. Stop the most advanced phishing attacks before they reach your users.
CLOUD ENTITLEMENT MANAGEMENT
Identify over permissive entitlements and ensure least privilege access across users and cloud services.
Zero Trust Data
Zero Trust is all about protecting data as it is continuously shared between workstations, mobile devices, application servers, databases, SaaS applications, and corporate and public networks. The Check Point Platform delivers multi-layered data protection, preemptively protecting data from theft, corruption, and unintentional loss wherever it resides.
- Encrypt data wherever it resides or is transferred to render stolen data useless.
- Track and control data movements across the network to ensure sensitive information does not leave the organization.
- Ensure least privilege access to sensitive data in applications and data security posture management.

CHECK POINT RELATED PRODUCTS/SOLUTIONS
DATA LOSS PREVENTION
Protect against unintentional loss of valuable and sensitive information.
SECURE EMAIL AND OFFICE APPS
Secure data residing in email and collaboration applications.
Zero Trust Workloads
Securing workloads, particularly those running in the public cloud, is essential as these cloud assets are vulnerable and attractive targets for malicious actors. Check Point includes cloud security solutions that integrate with any public or private cloud infrastructure, providing full visibility and control over these ever-changing environments.
- Seamless integration with any cloud infrastructure including AWS, GCP, Microsoft Azure, Oracle Cloud, IBM Cloud, Alibaba Cloud, NSX, Cisco ACI, Cisco ISE, OpenStack, and more.
- Easy-to-deploy solution secures any private or public cloud workload with least privileged access for any user from any device.
- Keep your cloud-based workloads secure from vulnerabilities and threats with runtime protection.

CHECK POINT RELATED PRODUCTS/SOLUTIONS
DEVOPS ACCESS
Evolve beyond costly hardware VPNs and complicated open- source software stacks.
PUBLIC CLOUD SECURITY
Protect assets and data while staying aligned to the dynamic needs of public cloud.

Check Point is #1 in the 2025 Miercom Enterprise & Hybrid Mesh Firewall Security Report
Visibility & Analytics
You can’t protect what you can’t see or understand. A Zero Trust Security model constantly monitors, logs, correlates, and analyzes every activity across your network.
Through its Platform Services, Check Point provides security teams full visibility into their entire digital estate’s security posture; so they can quickly detect and mitigate threats in real-time.

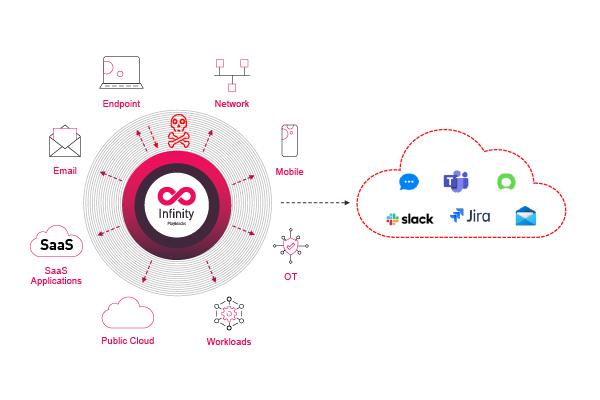
Automation & Orchestration
A Zero Trust architecture should support automated integration with the organization’s broader IT environment to enable speed and agility, improved incident response, policy accuracy, and task delegations.
Check Point Platform Services include a rich set of APIs that support these goals. Our platform services integrate with third party security vendors, leading cloud service providers and ticketing tools, among others.
Our APIs are also used by Check Point’s technology partners to develop integrated solutions.
Zero Trust Security Resources