Cyber Security Consulting Services
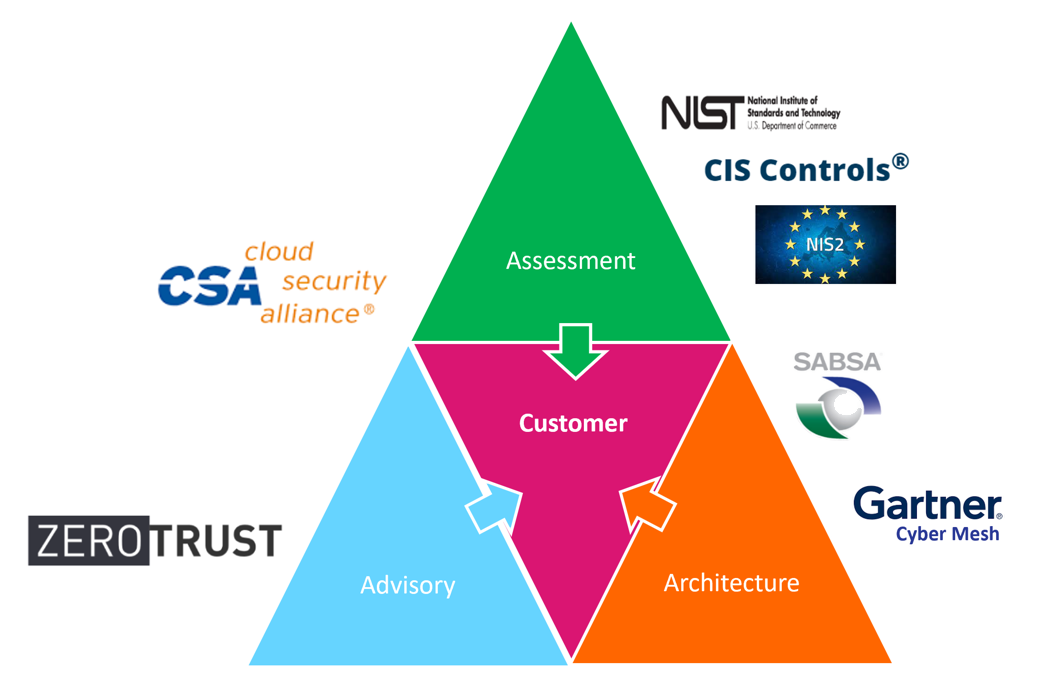
For nearly thirty years, Check Point has set the standard for Cyber Security. Across the ever-evolving digital world, from enterprise networks through cloud transformations, from securing remote employees to defending critical infrastructures, we protect organizations from the most imminent cyber threats. Check Point Security Consulting leverages this experience along with independent frameworks, such as NIST CSF, SABSA and Zero Trust Architecture, to provide advisory and assessment services to the company’s global customer community.
Our Methodology and Building Blocks
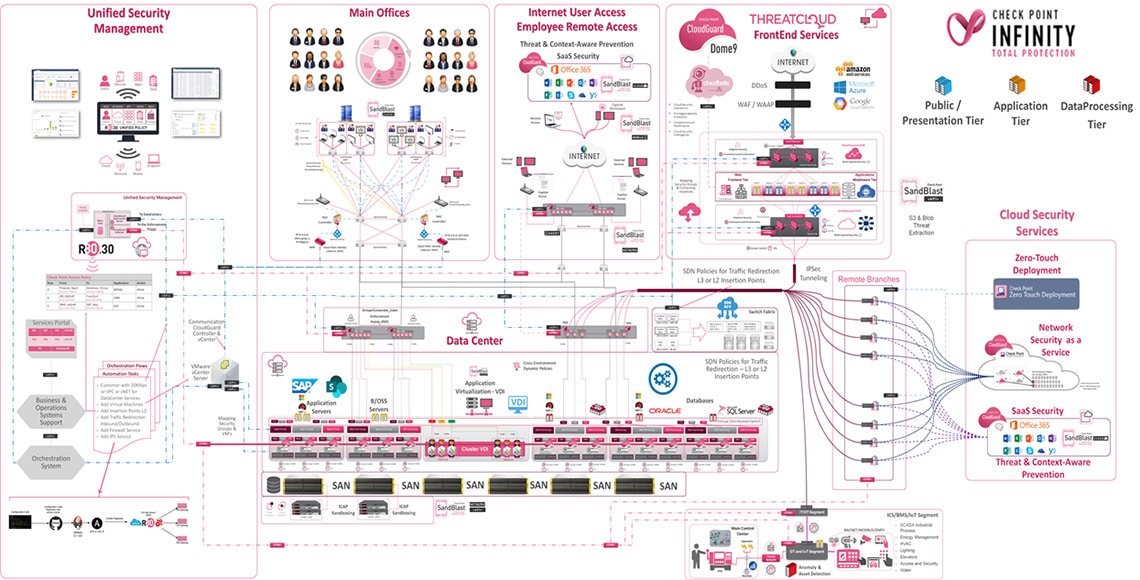
Check Point Security Consulting services help customers understand and adapt to trends impacting the information technology and cybersecurity markets. Our offerings operate in two primary domains: Assessments and Architecture. Assessment engagements follow NIST CSF principles to identify risk within the organization: people, processes and technologies. Architectural engagements foster dialog around Zero Trust and include design and modeling sessions intended to help customers formalize next generation security frameworks.
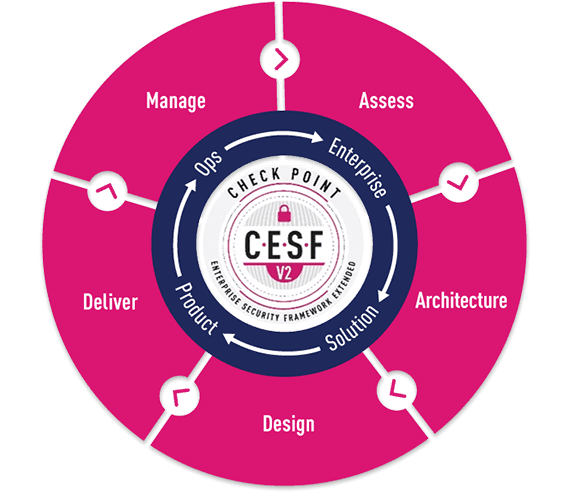
Check Point Enterprise Security Architecture Framework
Our practical experience protecting enterprise information systems. We believe that informed architectural, business-driven decisions are more cost-effective and provide sustainable, scalable security architecture.
CESF is open and accessible to all cyber security professionals and enables organizations of all sizes and industries to envision a security architecture that evolves with the changing security landscape while embracing well-formulated processes.
ARCHITECTURE / STRATEGIC CONSULTING
Security Assessment:
- Cyber Risk Assessments (NEW)
- Risk Management Frameworks (NEW)
- Penetration Testing
- Governance, Risk and Compliance assessments (NEW)
- NIS2 Readiness Advisory (NEW)
- Gap Analysis and NIST/CIS assessments (NEW)
- Treat Intelligence
- Vulnerability and inventory scans
- Cloud Security Posture analysis
Architecture and Consulting:
- Security workshops for (as is) and (to be) security architecture
- Zero Trust target architectural models
- Compliance and regulatory requirements
- Target Check Point Architecture and HLD
- Governance Framework development
- Cloud Transformation consulting / DevSecOps
- SDN Data Center (NSX / Cisco ACI)
- SOC Architecture
- CISO Advisory
CLOUD AND DIGITAL TRANSFORMATION
Check Point Secure Transformation Workshop Service is all about transforming initiatives and related technology for customers. The secure transformation workshop includes baseline of current state and desired future state, alignment to Enterprise Security Reference Architecture Frameworks and provides in-depth analysis report architecture and design best practices and opportunities, and recommendations with a “journey” roadmap with targets and waypoints.
- Hybrid Cloud modeling
- ZTNA/ SASE / SDWAN
- DevSecOps
- CNAPP / Meshed Security
- Cloud network segmentation
NETWORK ARCHITECURE AND DESIGN
Check Point Security Architecture and Design Service is primarily technical and the focus is cyber security architecture and design initiative, provides in-depth technology review and analysis. Delivers design and architecture best practices and opportunities, and recommendations.
- SDN Data Center modernization using VMWare NSX-T / Cisco ACI / Arista etc
- Technology Adoption
- Zero Trust Segmentation principles
- Operation modeling
- Security Automation and Orchestration (IaaC / SECaaC)
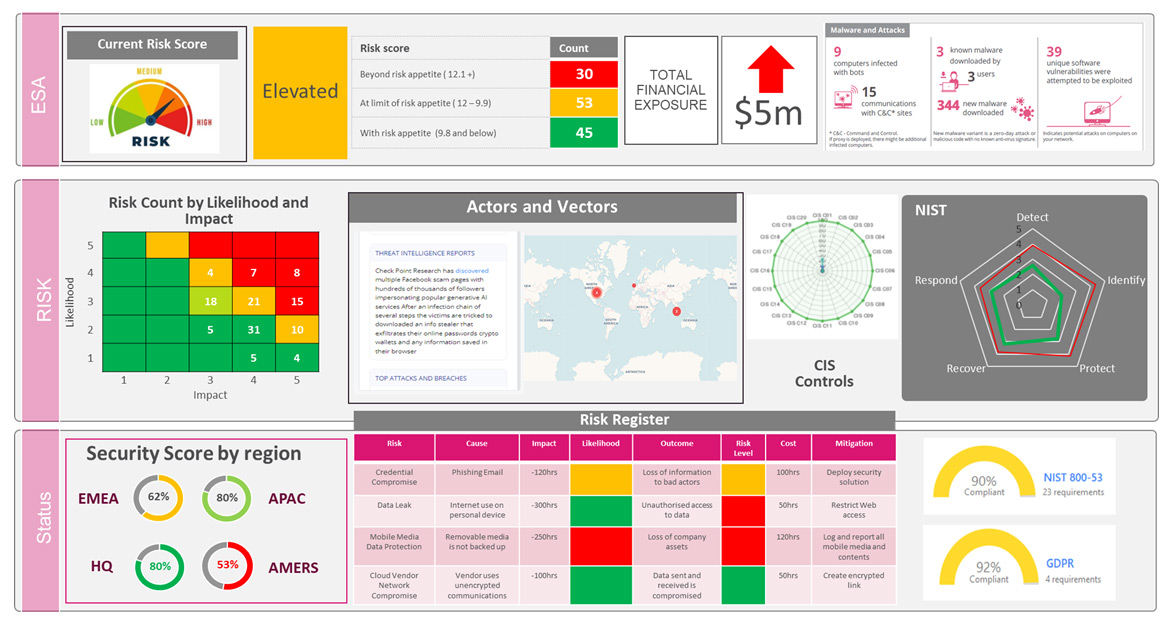
CYBER SECURITY RISK ASSESSMENT
- Check Point’s Cyber Security Risk Analysis Service is designed to assess how well organization is currently performing in compliance with existing or future GRC framework(s). Stakeholders are primarily Governance, Risk, and Compliance, CISO, CTO and CFO.
- Baseline existing state cybersecurity strategic goals to tactical objectives, reviews current policies
- Identify performance and gap analysis, along with roadmap of priorities and recommendations
- Great fit for privately held companies preparing for IPO or adopting new cyber security GRC standards and frameworks (NIST CSF, NIST 800-53, NIST RMF, CIS, CSA CMM), or seeking to advance the organization’s cyber security maturity level.
THREAT INTELLEGENCE
Real-time threat intelligence derived from hundreds of millions of sensors worldwide, enriched with AI-based engines and exclusive research data from the Check Point Research Team with the following services
DAILY DIGEST
- Daily report that summarizes the main cyber events and publications of the day.
- Focuses on items from open sources, darkweb , telegram channels and more.
INTELLIGENCE REPORTS
- Specific weekly/monthly reports that focus on areas of interest of the client:
- Specific nation state actors/APTs , Threat actors profiles
- Darkweb exposure of the client
- Industry/country specific darkweb intelligence
- Daily list of TOP IOCs relevant to the industry/country based on Check Point data
ELITE INTELLIGENCE
- Deep technological research by one of the top cp
analysts - Vulnerability research
- Dedicated analyst for a given time frame for a specific project
- Reverse engineering (malware/ APK)
- Analyst as a Service
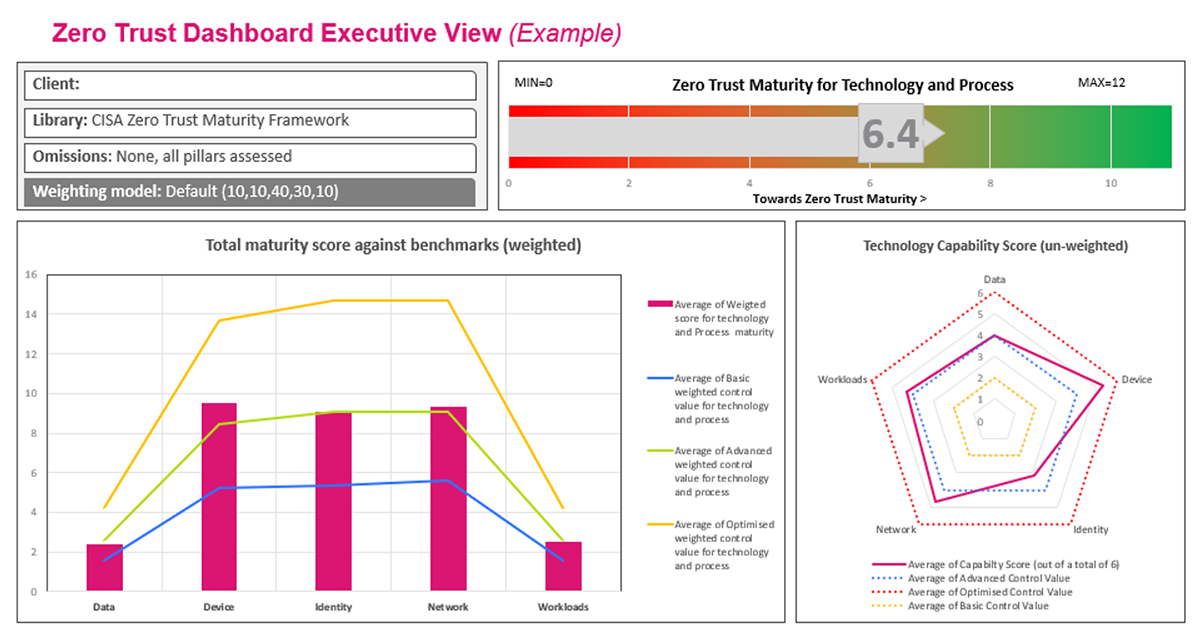
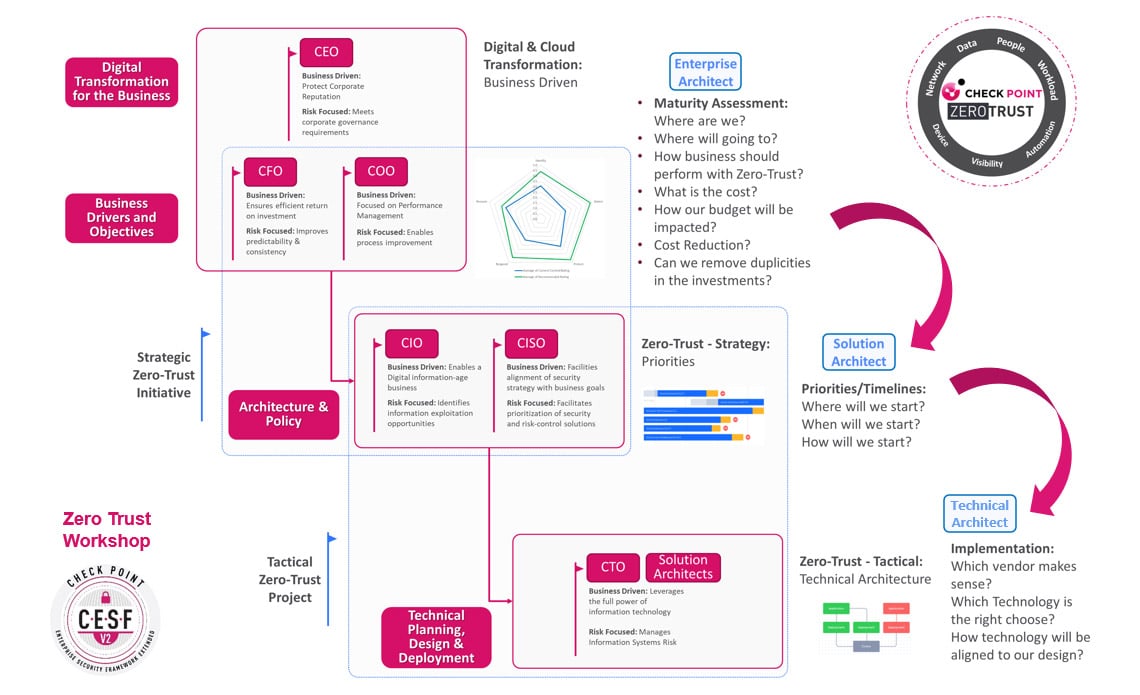
Zero Trust Advisory Service
The enterprise security architecture team developed a Zero-Trust Workshop program designed to address the demand for architectural assistance with defining ZT strategy customized to the customers needs and aspirations. This workshop is fully aligned with Zero Trust principles and Check Point products and services portfolio and it can be delivered as an advisory session which can lead to road map recommendations or a full architecture assessment engagement with a detailed implementation plan & blueprint.
Cloud Security Maturity Assessment
Check Point Cloud advisory service is all about transforming initiatives and related technology for customers. The secure transformation workshop includes Cloud Security Maturity Model baseline of current level review and desired future state, alignment to Enterprise Security Reference Architecture Frameworks and provides in-depth analysis report architecture and design best practices and opportunities, and recommendations with a “journey” roadmap with targets and waypoints.
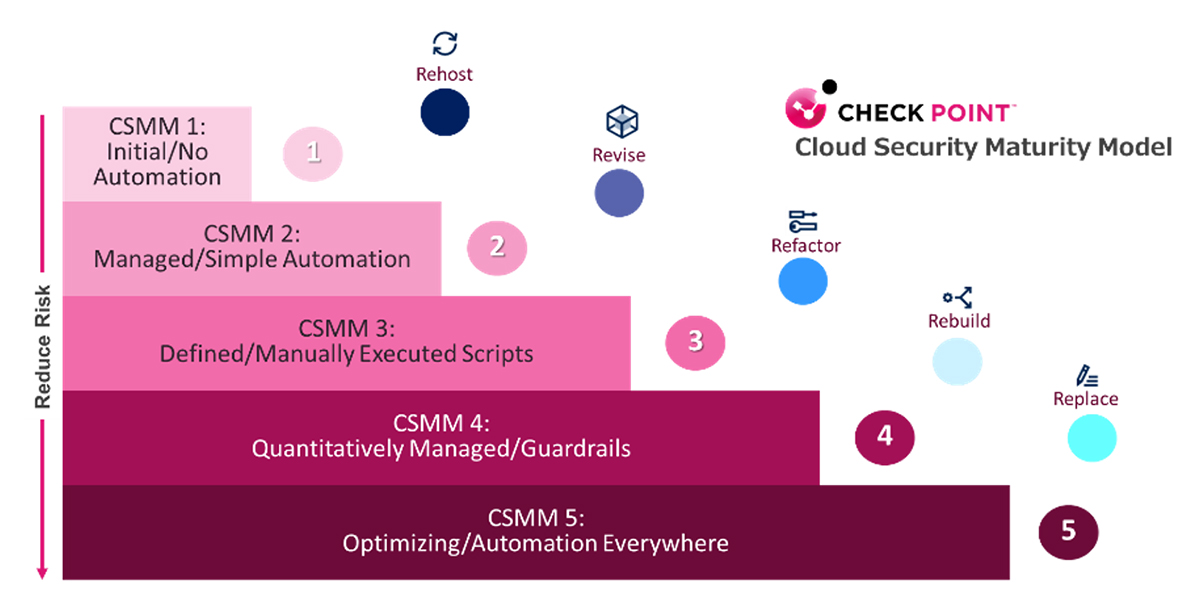
- CSMM assessment
- ZTNA / SASE / SDWAN
- DevSecOps
- CNAPP / Meshed Security
- Cloud network segmentation
Contact our consulting team for help with your Public, Private, or Hybrid Cloud Architecture. We will assess your maturity level and guide you to ensure your organization’s safety and security.
Advanced Cyber Security Assessment
Check Point also provides pure-play consulting services that enable organizations to prepare for compliance and audit activities and accelerate their maturity benchmarking efforts. Our assessment offerings include:
- Assurance reviews based on industry standard frameworks, such as NIST 800-53, NIST CSF, CIS, and NIS2
- Cloud security posture engagements based on best practices from AWS, Azure and Google
- Vulnerability assessment and penetration tests on external and internal zones, including compromise assessments
- Comprehensive security posture assessments, including incident preparation, tabletop exercises and SOC design reviews
NIS2 Readiness Advisory
NIS2 has been released to all countries within the European Union. In 2024 NIS2 will be adopted into local law and become relevant for a large amount of companies. Check Point can help you in preparing your company for NIS2 and assist you in improving your security standards and procedures.
Benefits
- Verify if your company is affected by NIS2 and by what measures you will be affected
- Get an overview of the necessary technical requirements for NIS2
- Review the processes needed to be compliant
- Learn about trainings regarding NIS2
Delivery
The Check Point Team will deliver this during a one day workshop with one of our senior experts. We will provide materials and solutions around the requirements of NIS2 and can follow up with an in depth assessment of your environment.
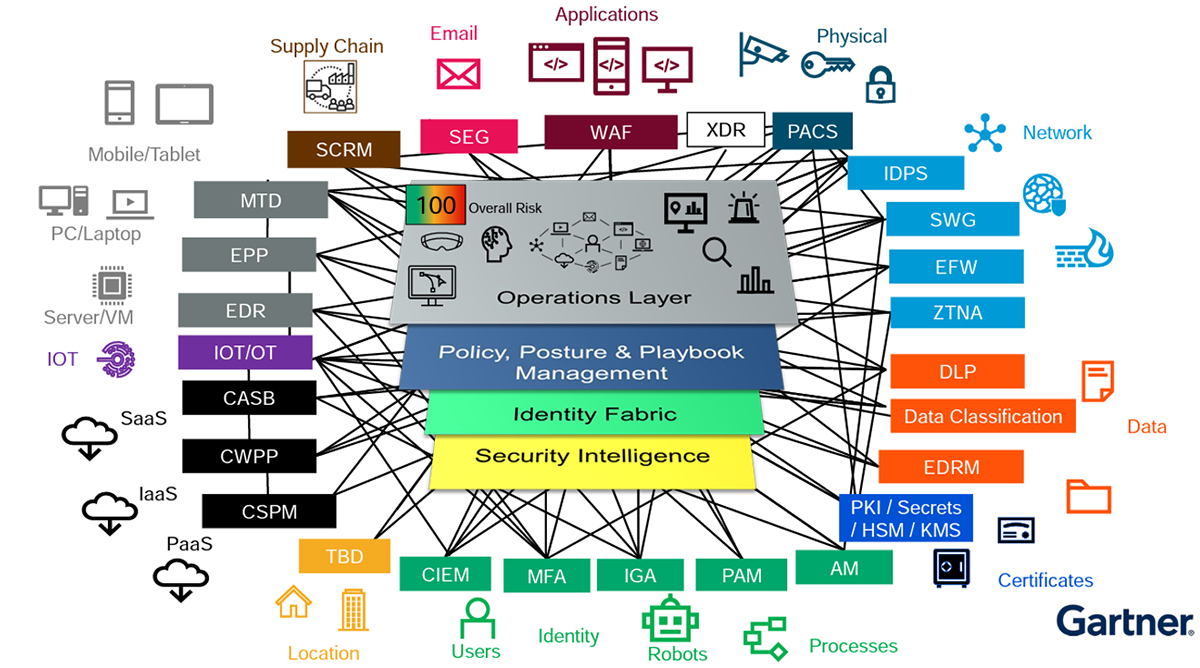
Cyber Mesh Security Architecture
Enterprise Architecture Workshop
The Enterprise Security Architecture program provides a unique opportunity for organizations around the world to review their current and future security programs with Check Point’s most senior consultants. During these multi-day sessions the teams examine the organization’s business processes, security strategies, design, deployment and operational methods and compare these with industry and Check Point’s best practices. The outcome of the sessions is a customized security architecture intended to help ensure resilience to evolving attacks as well as optimized operational costs, consolidated controls and streamlined management, monitoring and maintenance practices.
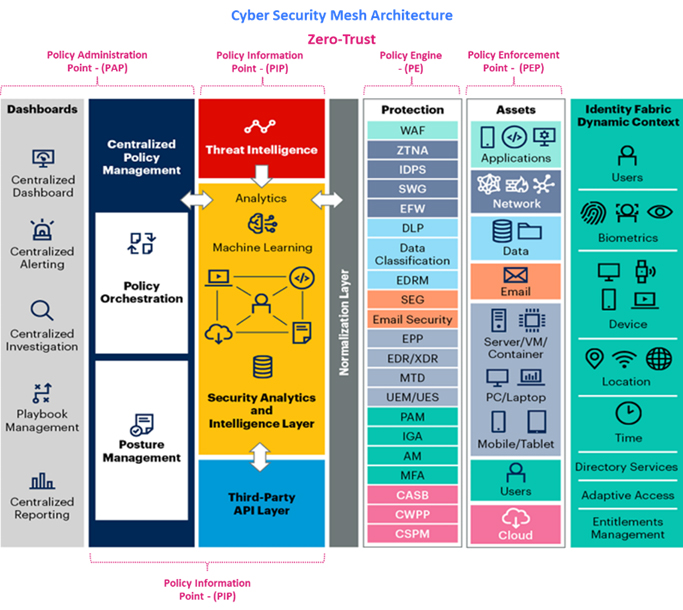
In the ever-evolving cybersecurity landscape, two prominent concepts stand out as game-changers in the industry: the “Cyber Security Mesh Architecture (created by Gartner) and the Zero-Trust Framework (by NIST-CISA and Forrester)”.
These approaches collectively empower organizations to fortify their digital environments against threats more effectively than traditional perimeter-based security models that are becoming less effective.
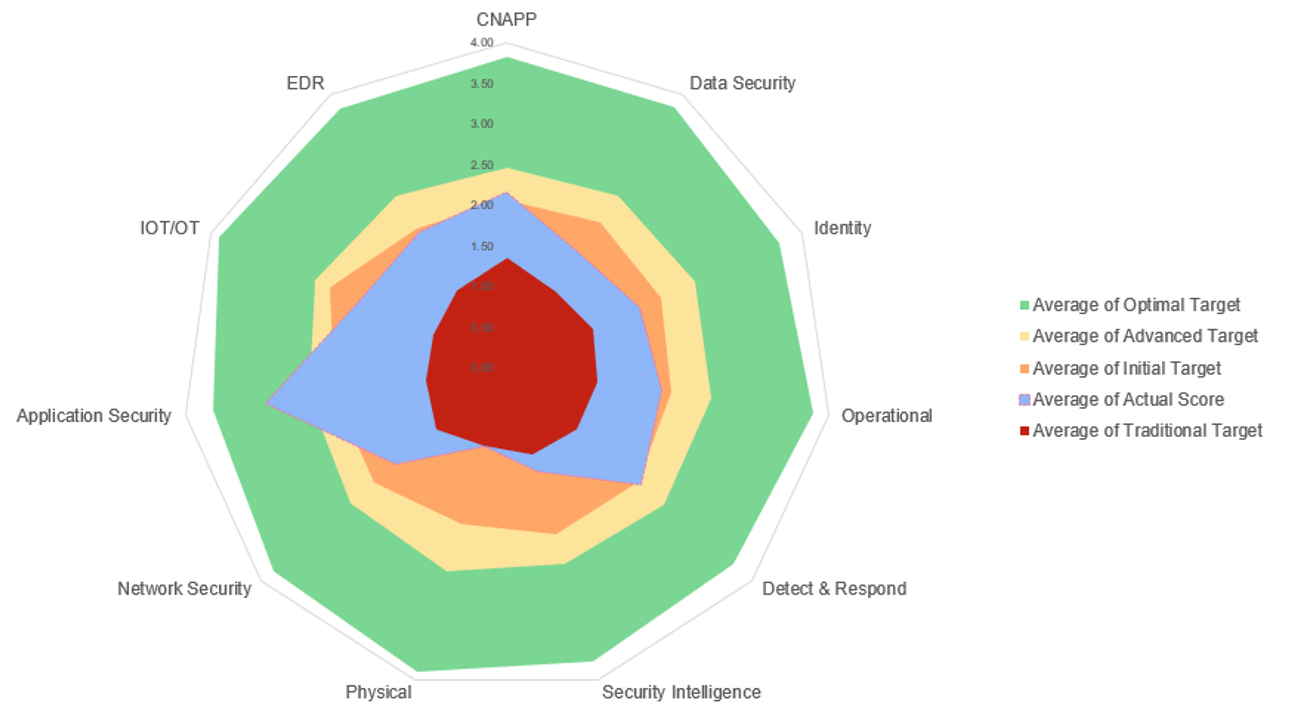
Check Point’s Strategic Consulting Team has found a relationship between the Zero-Trust Maturity Model and CSMA.
The Zero-Trust Maturity Model enables us to guide the strategic implementation of Zero-Trust principles.
At the same time, the Cyber Security Mesh Architecture operationalizes those principles by spreading security controls across the digital landscape.
Together, they provide a comprehensive approach to cybersecurity that promotes proactive risk management, continuous monitoring, and adaptive defense mechanisms, ultimately enhancing an organization’s ability to withstand and respond to evolving cyber threats.
“Information Security is a journey and not a destination.”
Our Consulting Services provide the CSMA and Zero Trust maturity assessment and advisory workshops, where our team will review your current readiness to appropriately define the priorities and roadmap implementation.
Our Consulting Services provide the CSMA and Zero Trust maturity assessment and advisory workshops, where our team will review your current readiness to appropriately define the priorities and roadmap implementation.
Our services can help you to evaluate your current Zero-Trust and CSMA maturity stage, validate the wins, and provide a prescriptive plan to help you take the next step successfully.
Benefits
- Identify the crown jewels: if you are just starting off, we will help you identify high-priority areas for protection.
- Assess your current state (AS-IS): we will review your existing identity, access the control environment, and policies to determine how they fit into a zero-trust framework.
- Visualize what’s next (TO-BE): we will help you to prioritize zero trust strategy and CSMA implementation milestones to align with business objectives.
- Plan the deployment: receive a detailed plan and roadmap with defined next steps for implementation readiness and actual deployment.
Contact our consulting team for help with your Zero-Trust Strategy and Cyber Security Mesh Architecture. We will assess your maturity level and guide your organization to ensure your organization’s safety and security.
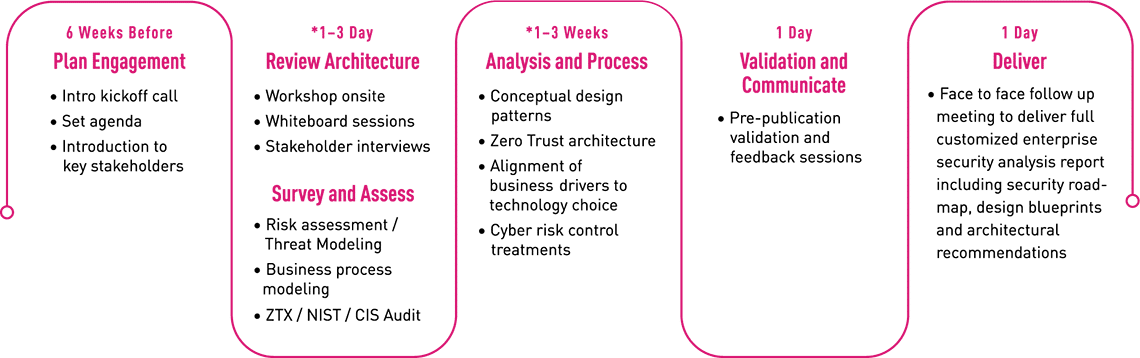
Timeline
ARCHITECTURE WORKSHOPS
Our consulting service engagement process involves key stakeholder discussions with detailed review of the business perspectives, drivers, strategy, challenges, current state, desired future state, and target security architecture.
Business and Architecture Review:
Check Point teams capture multiple data-points relating to business context, strategy, organizational aspirations, security posture, etc. though a tailored face-to-face workshop. The framework is used because it meets the customers’ requirements for a structured systematic approach to the design, architecture and ongoing digital transformation.
Design and Build Security Architecture:
Check Point architects develop a response to the business and security requirements aligned with security best practices to enable the clients’ digital transformation. Open standards, such as Zero Trust, are used as architectural design principles. The Security Architecture Workshop and CESF process take a business requirement and translate it to a working, physical solution that protects the customer and reduces their cyber risk.