Detect Threats with High Accuracy and Act Based on Your Policy
iOT365’s integrated IDS, SIEM, and SOC use multi-layer AI analysis to deliver real-time threat detection with 80–90% fewer false positives compared to solutions that rely on external SIEMs or SOCs. For any unknown or suspicious connection, iOT365 securely shares device information and metadata with Check Point Quantum IoT Protect, which enriches it with Check Point’s global threat intelligence. Customers can then choose how to respond, for Check Point to block malicious traffic at the firewall level or simply generate an alert, based on each organization’s risk tolerance and policy. This ensures maximum security without unnecessary disruption to operations.
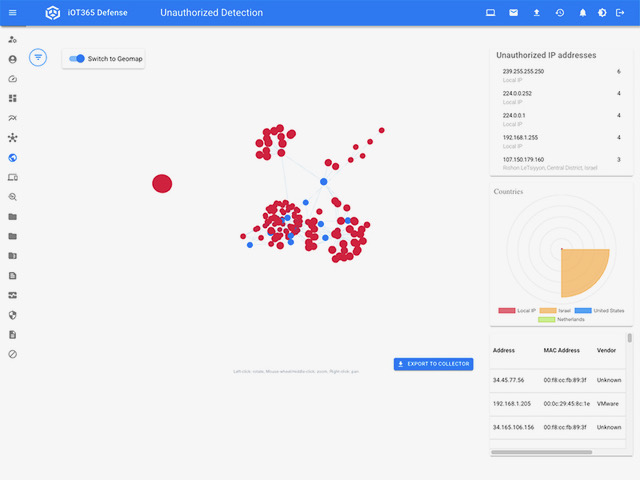
Full-Stack Threat Coverage
Detects anomalies, unauthorized protocols, and OT-specific threats passively without impacting production.
Automated & Rapid Response
Discovers assets, correlates events, classifies risks, and generates AI-driven playbooks.
Compliance & Risk Reduction
Continuously monitors and reports OT network behavior, ensuring compliance.