Sécurité des périphériques IoT pour les fabricants
Si vous construisez des appareils embarqués destinés aux consommateurs et à l’Internet des objets (IoT), l’expansion du paysage des menaces vous oblige à protéger vos clients contre les cyberattaques grâce à une sécurité du firmware prête à l’emploi.
From IP cameras and smart elevators, to routers, medical devices and industrial controllers, Check Point IoT Embedded provides on-device runtime protection against zero-day cyber attacks – serving as the most powerful line of defense for your IoT devices.
DEMANDER UNE DÉMONSTRATION DE NANO AGENTCheck Point IoT Embedded
ÉVALUEZ. RENFORCEZ. CONTRÔLEZ.
La protection révolutionnaire de l’exécution sur l’appareil vous permet de développer des appareils IdO connectés avec un firmware de sécurité intégré
qui protège contre les cyberattaques les plus sophistiquées.
![]()
Évaluer le risque
Découvrez les risques de sécurité dans
votre firmware IdO
![]()
Renforcer
Renforcez le dispositif avec une protection d’exécution sur l’appareil pour empêcher les attaques de type zero-day
![]()
Contrôle
Définir et appliquer des politiques par appareil pour l’accès continu au réseau
Comprendre les règlements relatifs à la sécurité de l'IdO
En tant que responsable de la cybersécurité de votre organisation, vous avez été témoin de la croissance sans précédent des dispositifs IdO au sein de votre entreprise. Pour bon nombre de ces appareils, la sécurité de l'appareil et de ses données est souvent déficiente, ce qui expose l'organisation à divers risques de sécurité comme les attaques par déni de service, les logiciels malveillants, les logiciels rançonneurs et l'usurpation d'identité DNS.
Téléchargez ce document pour en apprendre davantage sur la réglementation récente de la sécurité de l'IdO, comprendre son importance et apprendre comment vous préparer efficacement à faire face à ces cyberattaques sophistiquées.
TÉLÉCHARGER MAINTENANT

Guide de sécurité de l'IdO : défis et solutions
Empêchez et combattez les attaques cybernétiques sur vos
réseaux et appareils.

Les défis modernes en matière de sécurité de l'IdO
Une fois compromis, les cybercriminels peuvent se déplacer librement pour accéder à des applications plus critiques et à des données sensibles. Ils peuvent détenir ces informations contre une rançon, ce qui risque de mettre à l'arrêt le réseau de l'entreprise au cours du processus. Une solution complète de sécurité de l'IdO est nécessaire pour protéger votre entreprise contre ces risques et constitue un élément essentiel de la stratégie de cybersécurité de chaque entreprise. Découvrez comment protéger votre entreprise dans cet e-book informatif.

« Check Point IoT Protect Agent nano nous offre une solution de sécurité robuste
et de bout en bout pour nos clients. Les caméras Provision-ISR seront équipées d'une cybersécurité de nouvelle génération prête à l'emploi, avec une mise en œuvre plug-and-play. »
–Yonatan Pick, directeur de la technologie, Provision-ISR
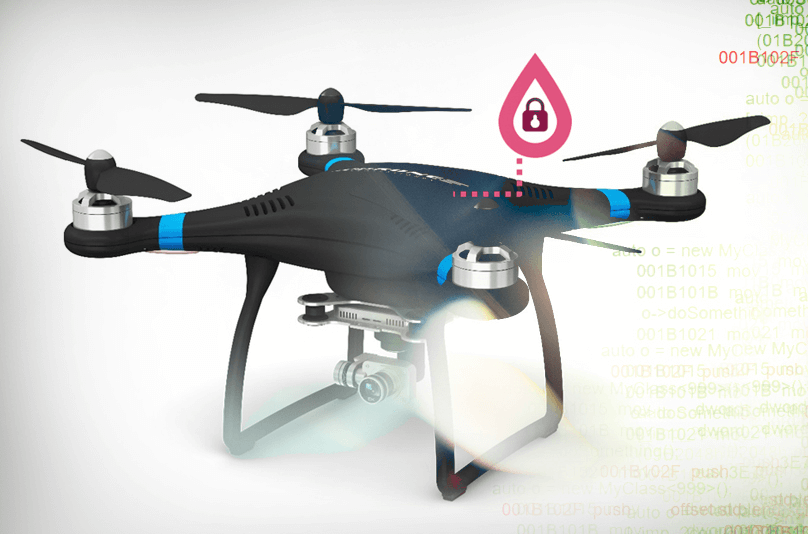
Comment la sécurité du firmware permet d’éviter les exploits réels
Découvrez comment la sécurité intégrée fonctionne
- Le firmware du routeur est compromis par une vulnérabilité connue
- Une fois dépassé, une analyse du réseau révèle d’autres actifs, notamment une caméra IP, que l’attaquant expose à Internet
- Check Point IoT Protect™ Agent nano® est installé
- La même vulnérabilité du routeur est bloquée par le Nano Agent® et ne peut plus être exploitée
Découvrez les risques liés à la sécurité des appareils IoT
Check Point IoT Embedded Risk Assessment
En ce qui concerne la sécurité du firmware, les risques sont nombreux, qu’il s’agisse de composants tiers de la chaîne d’approvisionnement, de micrologiciels obsolètes, de portes dérobées commanditées par l’État ou d’autres vulnérabilités.
Pour commencer à proposer des appareils IdO sécurisés dès la sortie de l’emballage, les fabricants d’appareils IdO doivent comprendre la posture de sécurité en temps réel de leur firmware afin de pouvoir identifier les failles et les corriger.
Inscrivez-vous pour une évaluation automatisée gratuite des risques liés au firmware afin de découvrir les risques inhérents à votre appareil, et obtenez un rapport complet comprenant des mesures d’atténuation rapides.
RECEVEZ UNE ÉVALUATION GRATUITE DES RISQUES DU FIRMWARE IOT
Prévenir les attaques grâce à la protection au moment de l’exécution sur l’appareil
Le révolutionnaire Check Point IoT Protect™ avec Agent nano® fournit une protection d’exécution sur l’appareil permettant aux appareils connectés de bénéficier d’une sécurité intégrée au firmware. Basée sur la technologie de pointe Control Flow Integrity (CFI), la solution légère Check Point IoT Protect™ avec Agent nano® vous permet de repousser les attaques d’appareils les plus sophistiquées, notamment les injections de shell, la corruption de la mémoire, le détournement du flux de contrôle et même les vulnérabilités zero-day du firmware qui n’ont pas encore été découvertes.
DEMANDER UNE DÉMONSTRATION DE NANO AGENTDéployer la sécurité du firmware en trois étapes : évaluer
les risques, renforcer et contrôler
La sécurité du firmware offre la protection la plus étroite et la ligne de défense la plus solide pour votre appareil IoT.
Découvrez les risques associés aux appareils IoT, les mesures de défense en profondeur qui peuvent être prises pour sécuriser les écosystèmes IoT et pourquoi la sécurité du firmware est essentielle.
TÉLÉCHARGEZ LE LIVRE BLANCManage IoT Device Security from
the Cloud with Check Point
Définir et appliquer des politiques pour les appareils sécurisés
par IoT Protect Agent nano
API de gestion
- API de gestion ouverte disponible sur swagger.io
- Prend en charge les appareils connectés à Internet et les appareils dans les environnements de type air gap
Définir et appliquer des politiques
- Contrôler les communications du réseau IoT vers et depuis l’appareil
- Définir les pratiques de sécurité pour les appareils protégés par l'Agent nano®
Définir et appliquer des politiques
- Rapports, journaux et alertes complets
- Intégration aisée avec les principaux SIEM
- Console unifiée pour la gestion de l’informatique et des appareils IoT
Check Point révèle les vulnérabilités
des appareils IdO
des appareils IdO
Consultez les recherches et commentaires originaux de Check Point sur la sécurité des dispositifs IoT :
- Le côté obscur de l’éclairage intelligent
- Vulnérabilités découvertes sur Alexa d’Amazon
- UltraHack : les risques de sécurité de l’IoT médical
- Pourquoi la sécurité du routeur IoT est cruciale pour les individus, les organisations et les États
- Les entreprises de sécurité de l’IoT innovent alors que les normes sont à la traîne
Ready to Experience Check Point IoT Protect?
Essayer dès maintenant
Parler à un spécialiste
Obtenir un devis
2023 Cyber Security Report
Les conflits géopolitiques sont à l'origine de cyberattaques sans précédent.
Voir plus de tendances et de perspectives.

Ressources supplémentaires
Téléchargements
Présentation de la solution IdO pour les entreprises
Présentation de la solution IdO pour le secteur de la santé
Présentation de la solution IdO pour l'industrie
Présentation de la solution embarquée IdO
Whitepaper: Absolute Zero Trust, Only with Check Point
Infographique : 9 étapes pour une sécurité Zero Trust absolue