Check Point for
Workload Protection
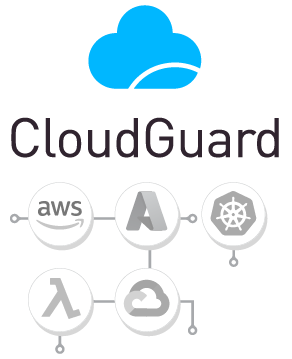
Check Point provides the first comprehensive, fully automated, cloud-native workload security solution. It provides unified visibility, compliance and threat prevention across applications, APIs and microservices (K8s containers & serverless functions), from development through runtime.
Webinar: Unified Workload Protection From CI/CD Through Runtime WATCH NOW
![]()
Security
Secure applications & microservices
to achieve zero trust
![]()
Automated
Auto-deploy & enforce security into
the DevOps pipeline
![]()
Everywhere
Security across all clouds and any workload architecture
Report: GigaOm Cloud Workload Security Radar DOWNLOAD NOW
Unified Workload Protection
From development through runtime, ensure that all applications, APIs, containers and serverless functions remain fully secured. Empower DevOps teams with a shift left tool to ensure that all code is automatically security centric.
Check Point Workload Protection – Image Assurance
Image assurance is an advanced security solution that identifies and detects any unauthorized changes to your system images, assuring that only trusted images are allowed to run in your environment. Image assurance also provides real-time visibility into the integrity of your images, allowing you to respond quickly to incoming threats.
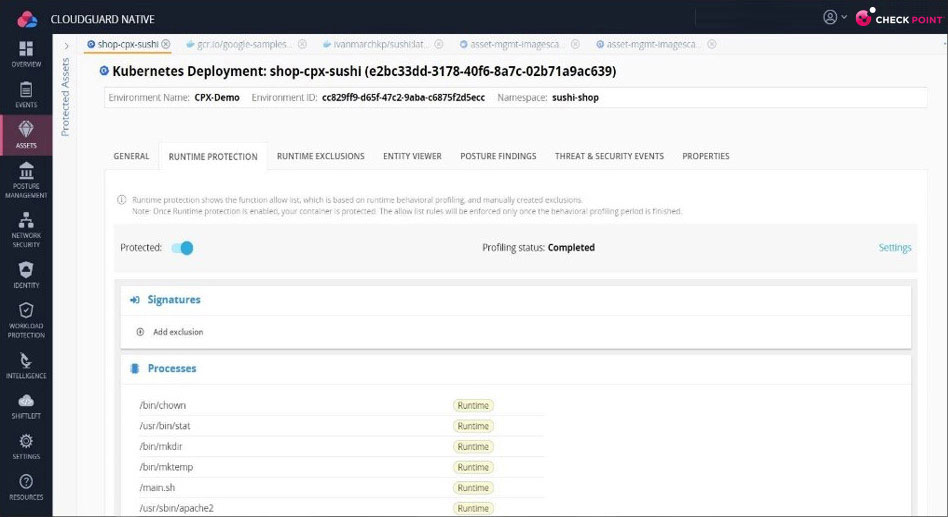
Check Point Workload Protection – Kubernetes Admission Control
Admission Control provides policy-based access control for workloads running in Kubernetes. It helps protect against malicious actors, unauthorized access, and data exfiltration by providing granular control over which workloads can access each other, as well as the Internet. Kubernetes Admission Control also helps organizations maintain compliance with internal security policies and industry regulations.
Check Point Workload Protection – Kubernetes Posture Management
Kubernetes Posture Management helps organizations secure their cloud-native applications by monitoring and enforcing the configuration of their Kubernetes clusters, ensuring that all workloads are running in a compliant, secure state. It provides an automated approach to continuously monitor and ensure the security posture of Kubernetes clusters and workloads.

“We selected Check Point as it seamlessly integrated into our ever-expanding use of AWS Lambda functions and helped automate security into our serverless infrastructure. Check Point also supports us as we move forward with integrating CI/CD pipelines, allowing us to easily and continuously defend our applications.”
– Brent Bain, Lead Cloud Architect and System Engineer at Best Friends Animal Society
Webinar: How to Layer Security into Modern Cloud Applications WATCH NOW
End-to-End Cloud Workload Protection
From CI/CD Through Runtime
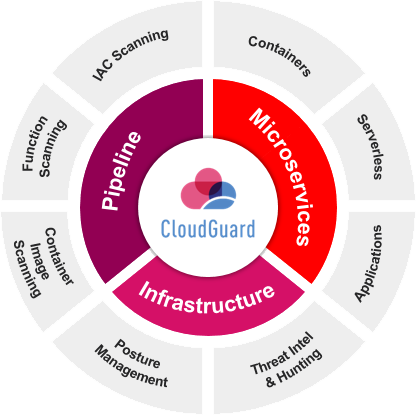
Security needs and considerations. DevSecOps and cloud providers are tasked with scanning each layer and every component for security issues, corporate compliance and best practices, and to ensure that they remain protected against threats.
Check Point unifies workload protection, providing visibility, security controls and scanning across the entire cloud workload from the first line of code through to runtime.
- Achieve zero trust security across applications, APIs, K8s and serverless functions
- Auto-deploy & enforce security controls
- Remain cloud & architecture agnostic with protection on multi and hybrid cloud deployments
Featured Capabilities
Container Security
Maintain posture management and gain visibility into your dynamic K8s environment. Provide CI tools for DevOps to scan container images in development. Govern all cluster operations with a central admissions controller and enforce least privileged access rights. Detect & block incidents in real time – ensure container integrity with active threat prevention
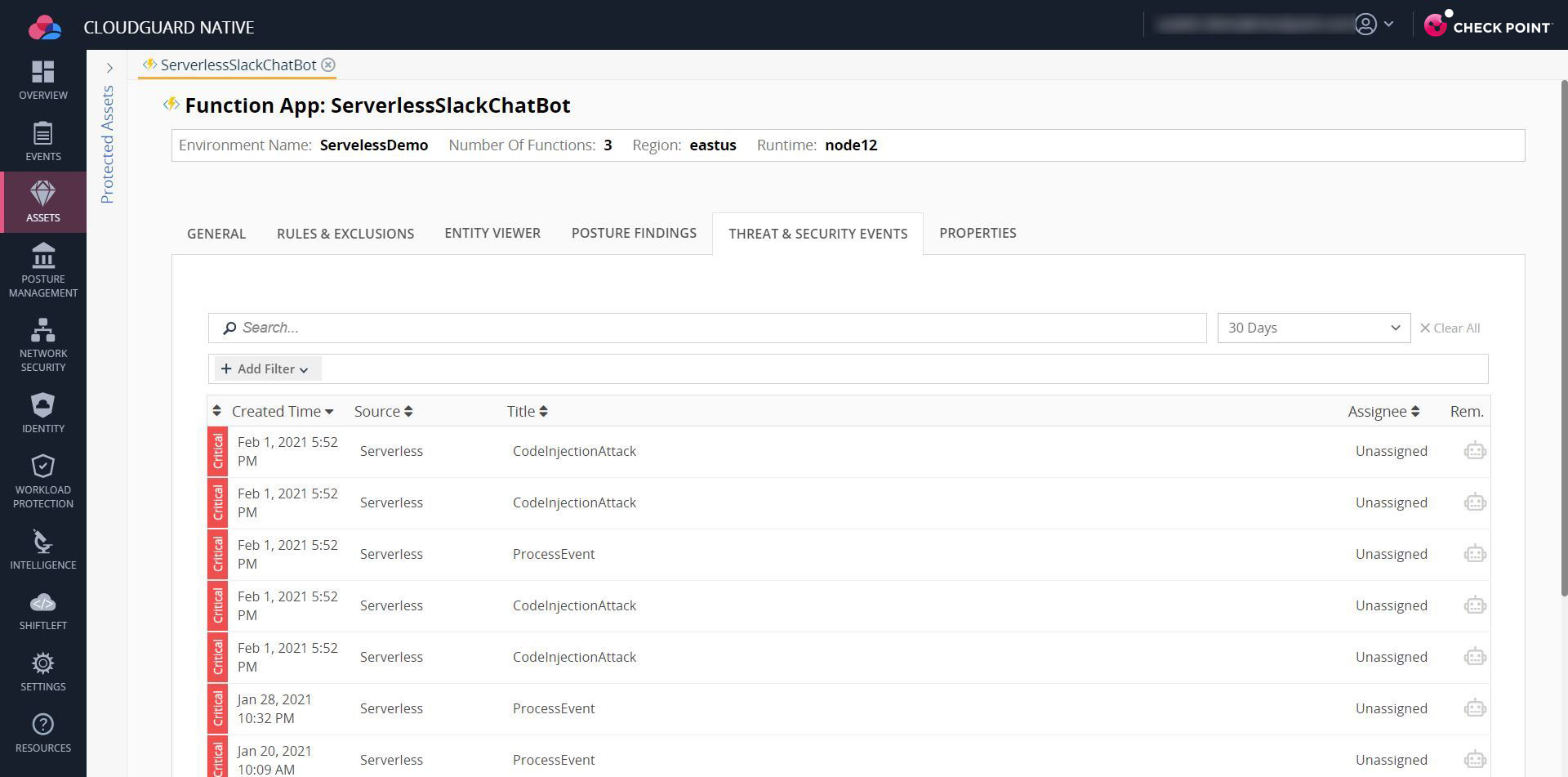
Serverless Security
Check Point automates serverless security while still empowering application developers to move at the speed of serverless. Check Point seamlessly applies behavioral defense, and least-privilege, to automatically protect serverless functions, with nearly no overhead in function performance. This ensures a continuous security posture, protecting the serverless functions from known and unknown attacks, while also meeting compliance and governance.
Application Security
Check Point AppSec represents a new paradigm in application security. Leveraging machine learning and a patent pending contextual AI engine, Check Point learns how an application is typically used, profiles the user and the app content and scores each request accordingly. This approach has proven to eliminate false positives while maintaining the highest standards of application security. With deployment to protection in a matter of hours, maintain application security with a solution that can keep up even with the fastest Devops teams.
Whitepaper: Your Guide to Containers & Kubernetes Security DOWNLOAD NOW
Learn How to Evaluate
a Cloud Workload
Protection Platform
DOWNLOAD BUYER’S GUIDE
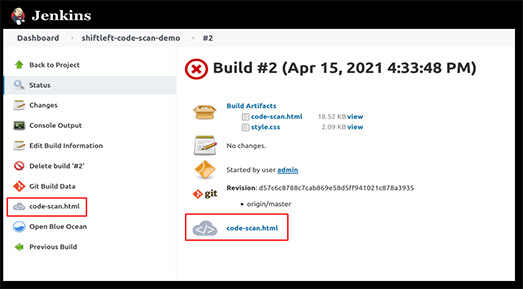
Empower DevSecOps – ShiftLeft
Use Check Point’s ShiftLeft tool to further increase DevOps’ agility. Automate and streamline security and governance within DevOps pipelines to ensure that all code is security-centric. Reduce risk and prevent delays, with continuous code scanning for K8s, Lambda functions & Azure FunctionApps.
REQUEST A DEMOBook a Live Demo to Check out Check Point for Yourself
Already a customer? Login or contact support.
Resources of Interest
eBook: AWS Lambda Serverless Best Practices DOWNLOAD NOW
Cloud Security
Knowledge Center
From Udemy courses to videos, check out the latest cloud security educational resources.
LEARN MORE
Take Your Security to the Next Level
Explore popular DevSecOps use cases and learn how to seamlessly automate security through the entire application lifecycle
Our Customers Love Us
Versatile Security Protection –Like A Swiss Army Knife For Security
Checkpoint Next Generation Firewall proves to be a great solution for our small business infrastructure. R80 Security Management has allowed our company to easily (and significantly) improve our protections over time. read more >
CheckPoint Next Gen FW, The Best Way To Protect A Corporation Against The Latest Threats
Our experience with CheckPoint has been very satisfactory for the advanced security approach, being able to provide our corporation with the latest generation security mechanisms and being able to have maximum control and visibility of our perimeter security. read more >
Apple In The World Of Firewalls
The Check Point Next Generation Firewall is like Apple in the world of Firewall and Security. It is an old, but still modern and competitive solution, and Check Point is always on the edge of security technologies. read more >
Ready to Automate Workload Protection?
How it Works
Try it Now
Get pricing
2023 Cyber Security Report
Geo-political conflicts trigger all-time high for cyberattacks.
See more trends and insights.

Check Point is powered by ThreatCloud AI
ThreatCloud AI, the brain behind all of Check Point’s products, combines the latest AI technologies with big data threat intelligence to prevent the most advanced attacks, while reducing false positives.