Check Point vs.
Palo Alto Networks
Discover why businesses choose Check Point
Miercom Enterprise & Hybrid Mesh Firewall Benchmark 2025 REQUEST A DEMOSee How Check Point Stacks Up Against
Palo Alto Networks
Next-Gen Firewall
Next-Gen Firewall
Malwares are blocked before getting in the network
See Comparison Here
See Comparison Here
Download the report
Download the report
*based on the number of high and critical CVEs identified in each vendor’s firewall and management platforms between 2021 and 2024. The values represent the operational patching cost of a medium-sized enterprise.
![]()
90%
of organizations are using outdated cyber security tools
![]()
77%
of security professionals anticipate a significant breach in the near future
![]()
95%
of breaches will likely occur as a result of customer misconfigurations, or other human errors
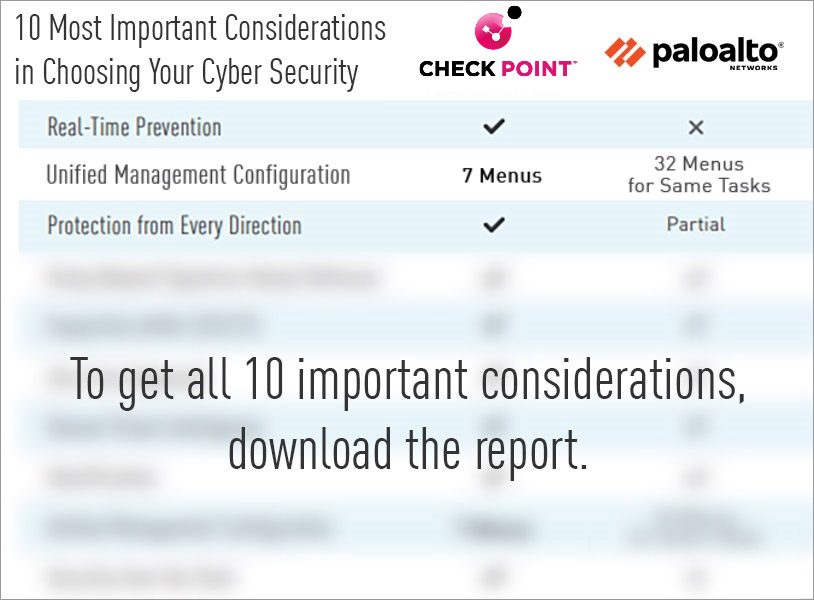
The 10 Most Critical Considerations in
Choosing Your Cyber Security
Real-Time Prevention
Your prevention platform should include cutting-edge technologies, like behavioral detection and machine learning algorithms, that can identify and block exploits on networks, cloud, and endpoints, before they execute and infiltrate your network. The ability to prevent patient-zero, so to speak, is critical.
![]()
![]()
Unified Management Configuration
When you invest in a single security management console, you not only reduce complexity and improve security, you also improve workflow. Multiple consoles means toggling back and forth across 10 or more different systems, leaving some systems unattended while you examine others.
Protection from Every Direction
Locking down everything is critical. The only way to ensure that your network is secure is by ensuring that everything connected to it is secure. Secure your individual computers, phones, tablets, and other extensions of your network.
![]()
See all 10 critical considerations in choosing your cyber security solution
Network Security Through the Voice of the Customer
Our Customers Love Us
Versatile Security Protection –Like A Swiss Army Knife For Security
Checkpoint Next Generation Firewall proves to be a great solution for our small business infrastructure. R80 Security Management has allowed our company to easily (and significantly) improve our protections over time. read more >
CheckPoint Next Gen FW, The Best Way To Protect A Corporation Against The Latest Threats
Our experience with CheckPoint has been very satisfactory for the advanced security approach, being able to provide our corporation with the latest generation security mechanisms and being able to have maximum control and visibility of our perimeter security. read more >
Apple In The World Of Firewalls
The Check Point Next Generation Firewall is like Apple in the world of Firewall and Security. It is an old, but still modern and competitive solution, and Check Point is always on the edge of security technologies. read more >