Evidence-Based Exposure Management with Astelia and Check Point
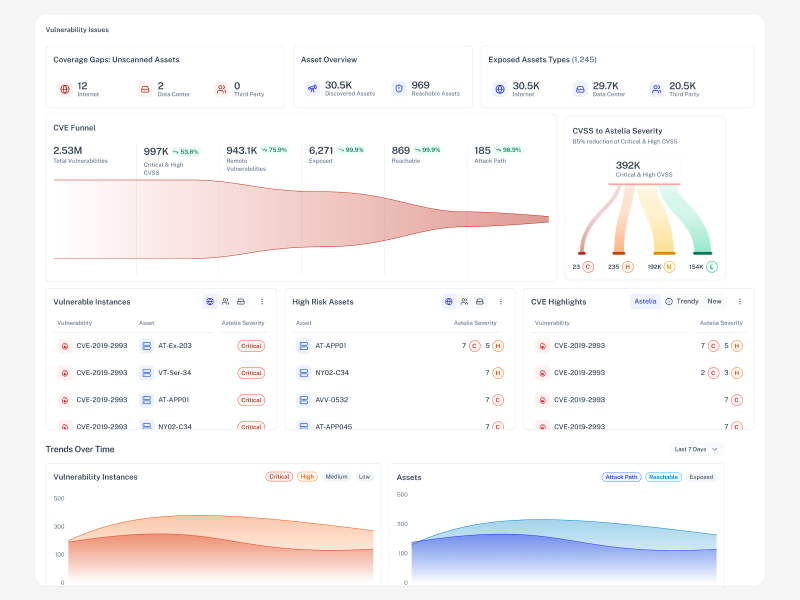
Organizations face thousands of “critical” vulnerabilities without knowing which are exploitable. Astelia and Check Point solve this by correlating CVEs with real network reachability and firewall enforcement. The joint solution surfaces only true exposure, enabling faster remediation, fewer tickets, and defensible risk decisions across security and network teams.
Astelia and Check Point replace legacy vulnerability prioritization based on abstract risk models and limited context with evidence-based exposure analysis, correlating CVEs with network reachability and firewall enforcement, so teams focus only on truly exploitable vulnerabilities.
Identify vulnerabilities that are truly reachable and exploitable
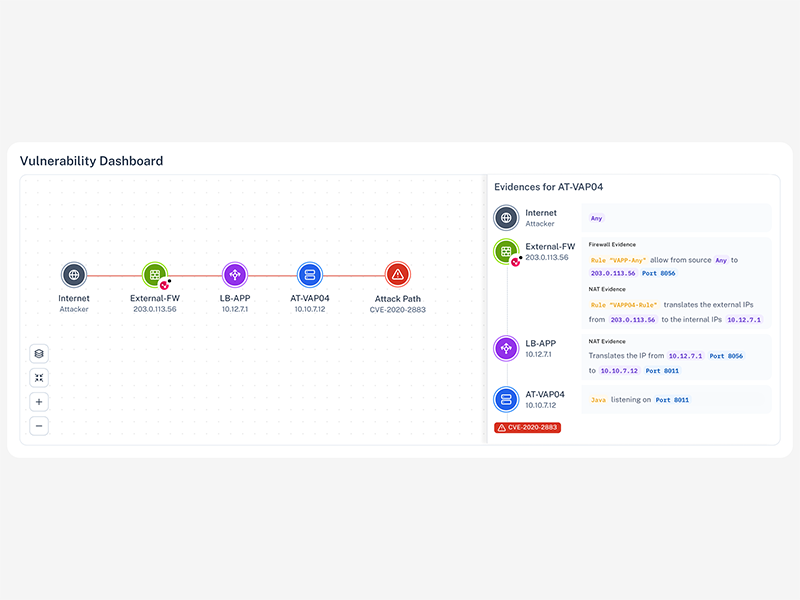
Full visibility into vulnerability reachability across real network paths for full visibility into vulnerability reachability across real network paths
Eliminate false positives using Check Point firewall enforcement data
Detect elusive threats with a combined cloud and endpoint security context to expose exploitable CVEs using firewall rules and exploit prerequisites
Prioritize remediation with evidence, not severity scores
Device and identity context that informs access decisions and prioritizes remediation with concrete evidence instead of assumptions