Advanced Phishing Prevention by Check Point Force
Secure your organization from phishing attacks with Check Point Force’s advanced solutions, preventing credential theft and securing your systems against malicious intrusions.
See how security protects customers around the globe
Phishing Protection Without Compromise
- Incident Response Automation
Automates the response to phishing attempts with immediate action against the threat - Behavioral Analysis
Analyzes user behavior patterns to detect anomalies that may indicate phishing attacks - Advanced Threat Detection
Leverages AI and machine learning to identify and block sophisticated phishing attempts
- Identify Supply Chain Attacks
Protects your business from phishing attacks disguised as familiar companies - Real-Time Email Scanning
Monitors emails in real-time to detect and quarantine phishing links and attachments - Seamless Integration
Easily integrates with your existing security infrastructure for enhanced protection
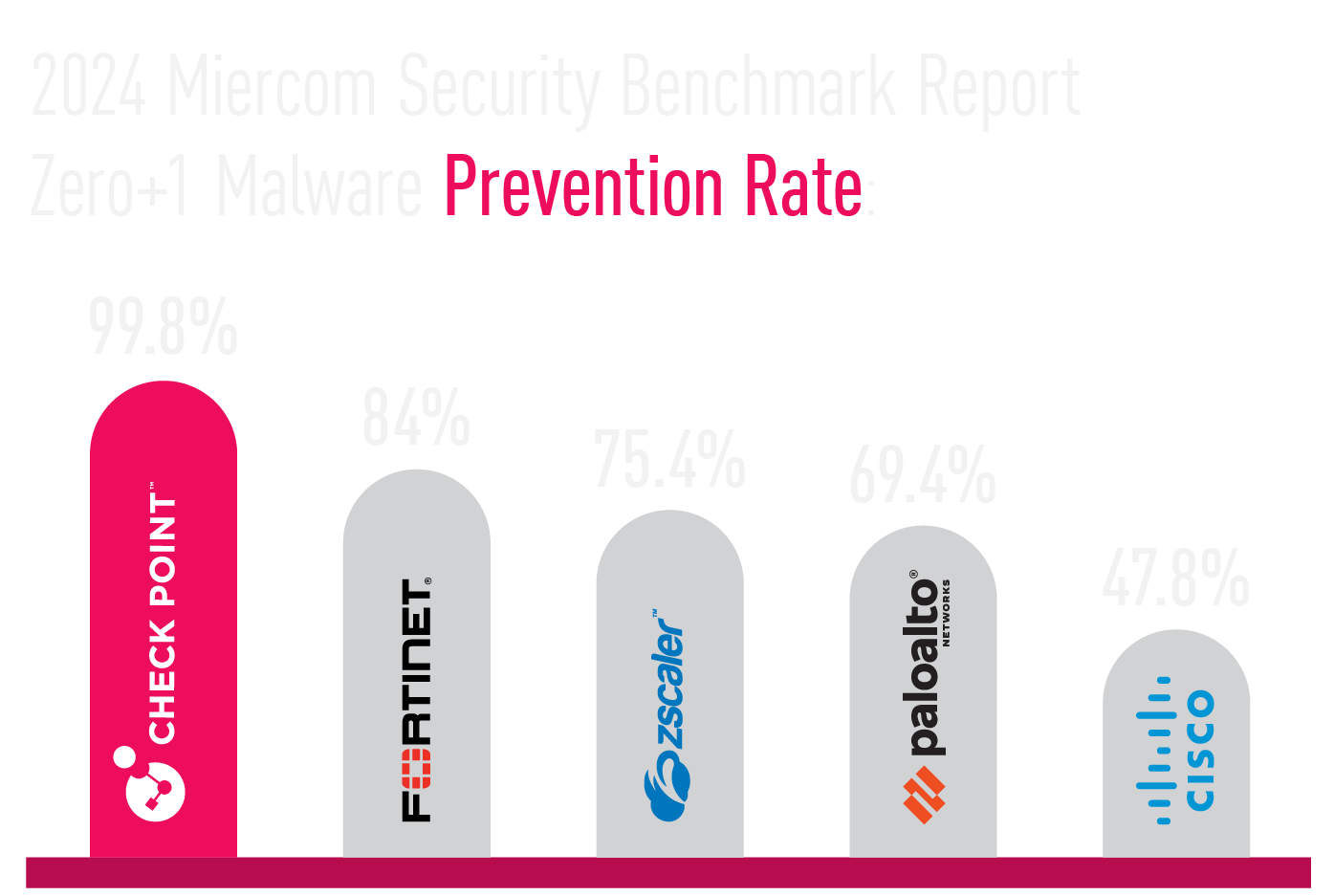
Rated #1 Threat Prevention
For the 2nd year in a row, Check Point was ranked # 1 in Miercom’s 2024 Security Benchmark report with a 99.8% malware block rate, 100% phishing prevention rate, and ultra-low 0.13% False Positive Detection rate (highest accuracy).
Miercom, a leading security testing lab, challenged the industry’s top firewalls with the latest generation of cyber-attacks, including Zero+1 day malware and phishing.
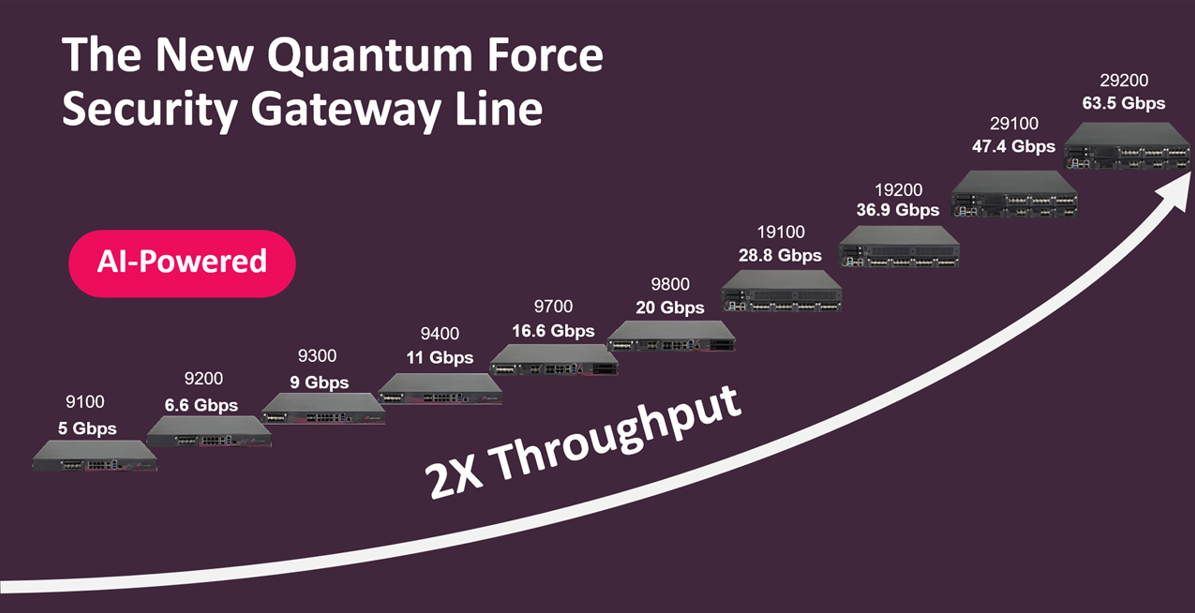
Flexible, Modular, Efficient
Flexible, Modular, Power Efficient
The Check Point Force series features a modular architecture with interchangeable network interfaces and connection speeds in power efficient 1RU/2RU appliances.
- 100G for Core Networks
- High density 1/10G direct server connections
- Macro & Micro Segmentation
- ASIC firewall acceleration for 100G ports

Check Point Force Across the Enterprise
AI-Powered Firewalls for Every Requirement
- High performance data center interconnections
- Service providers supporting millions of customer connections
- High-volume financial transactions with ultra-low latency
- Campus and Perimeter security
- Small organizations with limited security staff