Cyber Security for Manufacturing
Secure IT, OT, and remote access – without disrupting production.
One platform for centralized control and scale.
Manufacturing is under attack. Here’s what you need to know in 2026
What Keeps Manufacturing Running Is Exactly What Makes It Vulnerable
Manufacturing carries a different kind of risk: when something gets through, it can quickly spread into OT – disrupting production, safety, and compliance.
Manufacturing Is Ransomware’s Most Targeted Sector
The calculus is brutal: the longer a line stays down, the more pressure to pay. At ~$260k/hour of unplanned downtime, manufacturers are prime target. The industry accounts for 1 in 10 ransomware victims, with incidents causing direct physical impact up 146%.
The Weakest Link Is Probably Outside Your Walls
Over a third of breaches start with a third party – a vendor, contractor, or remote access tool you didn’t configure. Meanwhile, 40% of organizations have OT assets exposed to the internet. Manufacturing attack surface now extends far beyond the plant floor.
Stop Threats Before They Stop Production
We help secure manufacturing across IT, OT, and third-party access through a unified platform built for live production – with centralized control, local flexibility, and safe enforcement without disrupting production.
- One platform, not a pile of toolsconsistent policy + AI-powered intelligence, with less complexity and lower cost
- Roll out without downtime built for live production, no disruption
- Hybrid Mesh, built to scale consistent across sites, flexible locally, scales without redesign/forklift upgrades
- Bigger than OT, stronger when unified one approach across IT, OT, and remote access, with consistent policy and shared intelligence
- Governance you can prove audit-ready evidence across plants and teams
Shut Down Attack Paths.
Not Production.
Control what enters OT
IT and OT are more connected, creating more paths for attackers. One IT compromise can become an OT incident without a hard boundary.
What We Enforce:
- No direct IT-to-OT connection—traffic routed through industrial DMZ
- Block by default—only pre-approved connections allowed
- Pre-connection rules for every access attempt
- Admin authentication with full logging
- Block attacks on approved connections
Result: Only approved connections reach OT. IT attacks stay contained at the boundary.
Control vendor access into OT
Vendor and OEM access is necessary – but it has to be specific, enforceable, and auditable.
What We Enforce:
- Least-privilege access – vendors connect only to approved OT assets and applications
- Strong authentication (MFA where required)
- Segmented reach by user, role, application, and zone – not flat network access
- Session visibility and logging – who accessed what, when, and what they did
- Explicit approvals and exception handling for any expanded access
Result: Vendors get only the access they need. If a vendor is compromised, access stays contained, with a clear audit trail.
Control how far issues can spread
Inside OT, the difference between a local issue and a plant-wide event is whether movement is controlled.
What We Enforce:
- Default-deny between zones/cells – only required OT flows allowed
- Allow-only policy between segments based on operational need
- Protocol-aware inspection and enforcement for OT traffic (DPI)
- Visibility and logging for east-west OT movement between zones
- Exceptions governed with ownership and change history
Result: Only required flows run between zones. If one area is impacted, it stays local – with clear visibility and audit logs.
Control risk when patching isn’t possible
Always-on OT systems can’t wait for the next maintenance window – exposure needs control in the meantime.
What We Enforce:
- Network-layer compensating controls to reduce exploitability without touching the machine
- IPS protections aligned to real exposure and the traffic behind the asset
- Block known exploit attempts at enforcement points (where deployed)
- Visibility into exploit attempts and applied mitigations for proof and prioritization
- Exceptions governed with ownership and change history
Result: Exposure drops immediately while systems keep running – with documented mitigations and blocked attempts.
Manufacturing is evolving – your security should too.
Specialized OT Controls for Live Environments

Ruggedized Gateways
Industrial-grade gateways built to survive any harsh conditions – so enforcement can run on the plant floor without compromising reliability

IoT Security and OT Discovery
Connects Check Point IoT security with leading OT discovery platforms to turn OT context into enforcement, investigation, and remediation – without rip-and-replace

Professional Services
End-to-end security support across complex environments – from risk assessment, and penetration testing to MDR and incident response
This is bigger than OT – and stronger when it’s unified
One security architecture across IT, OT, and supply chain – unified where it matters, flexible where it’s needed
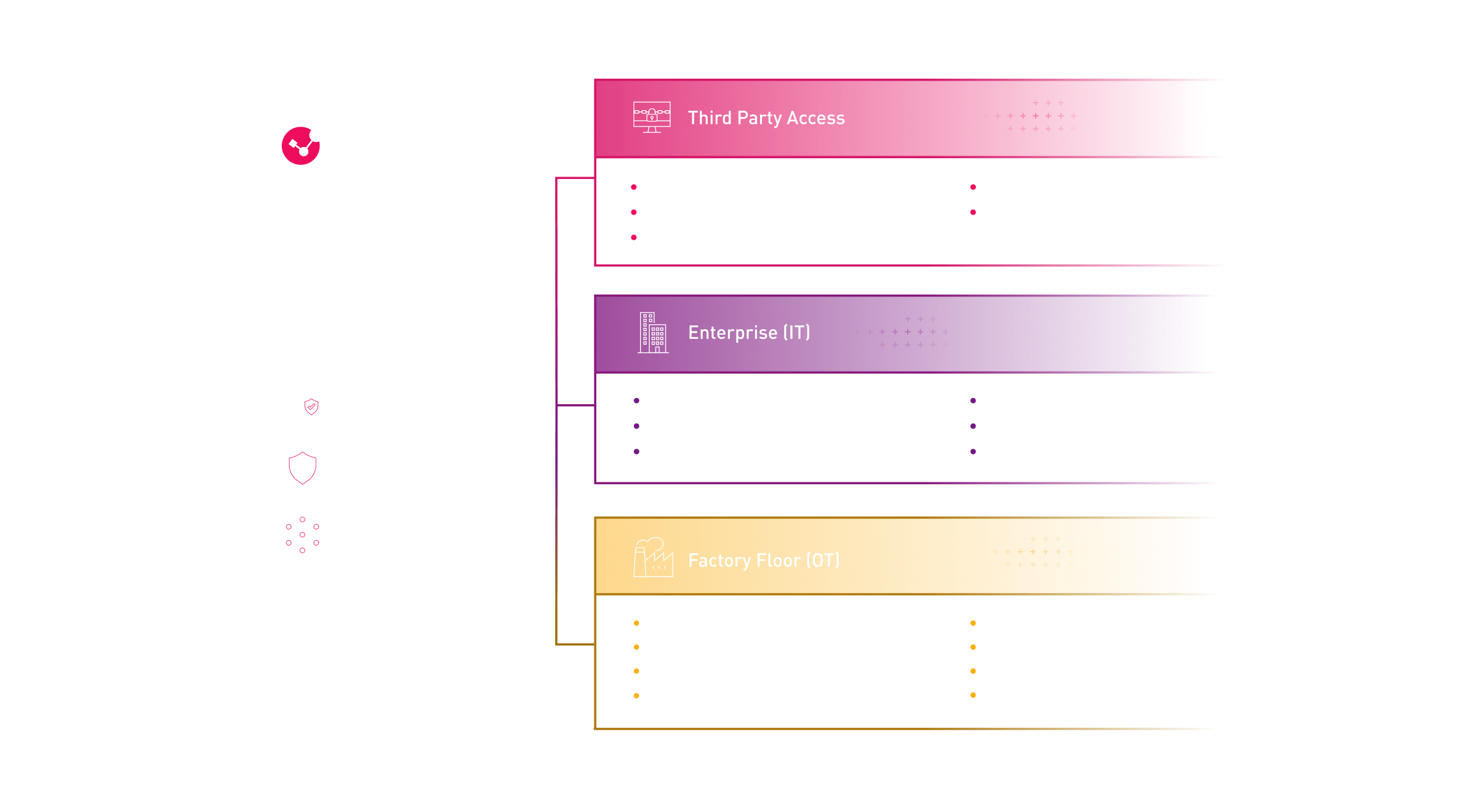
Purdue Model-based architecture view of IT-OT boundaries, remote access paths, and enforcement points – supporting OT and ICS security, OT segmentation, and virtual patching.
What’s hitting manufacturers hardest — and how resilient leaders respond
What This Looks Like in the Real World
Your Manufacturing Security Toolkit
Cyber Security for Manufacturing: What You Need To Know
Manufacturing is the most targeted industry for ransomware. Here’s what you need to know in 2026
Stop Threats – Without Stopping Production
We’ll help you identify the paths that matter most – and build a rollout plan your teams can enforce, scale, and prove.






