Cloud Security Solutions
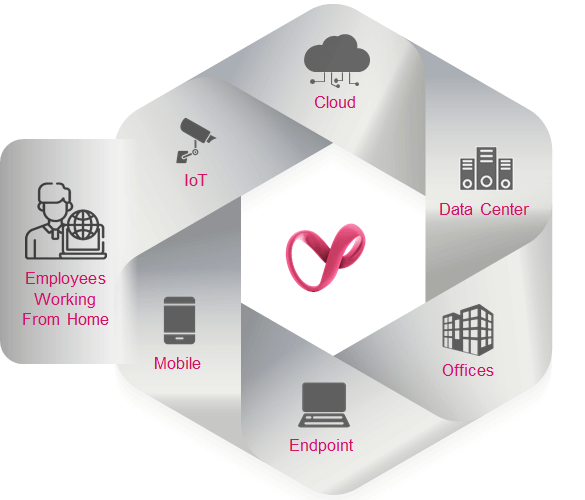
In order to keep up with today’s cloud threats, your cloud security solution needs to be in context, and provide advanced threat prevention for all your assets and workloads across your public, private, hybrid and multi-cloud environment.

Cloud Security Report 2025 DOWNLOAD NOW
35% of organizations have more than 50% of their workloads in the cloud and developing new applications at such velocity that it makes it nearly impossible for security teams to stay ahead. Modern cloud security deployments need security, automated, everywhere.
![]()
Advanced Threat
Prevention
Advanced threat prevention
for all your cloud assets
![]()
Automated
Security
Automated security across
your cloud environment
![]()
Unified Security for
Multi-Cloud
Visibility & control across your
entire multi-cloud environment
3,000+
Loyal Check Point
Customers
#1
Security Partner for
Microsoft Azure
300+
Cloud Native
Service Integrations
Cloud Native Application Protection
Managing cyber risk is always complex, and managing risk in the cloud is even harder- as cloud native applications change and scale 100 times faster then ever before. Today’s cloud environment needs more context in order to provide better security, and cloud speed and scale. Only Check Point CNAPP goes beyond simple posture management and workload protection to automate security throughout the software development lifecycle- from code to cloud.
LEARN MORE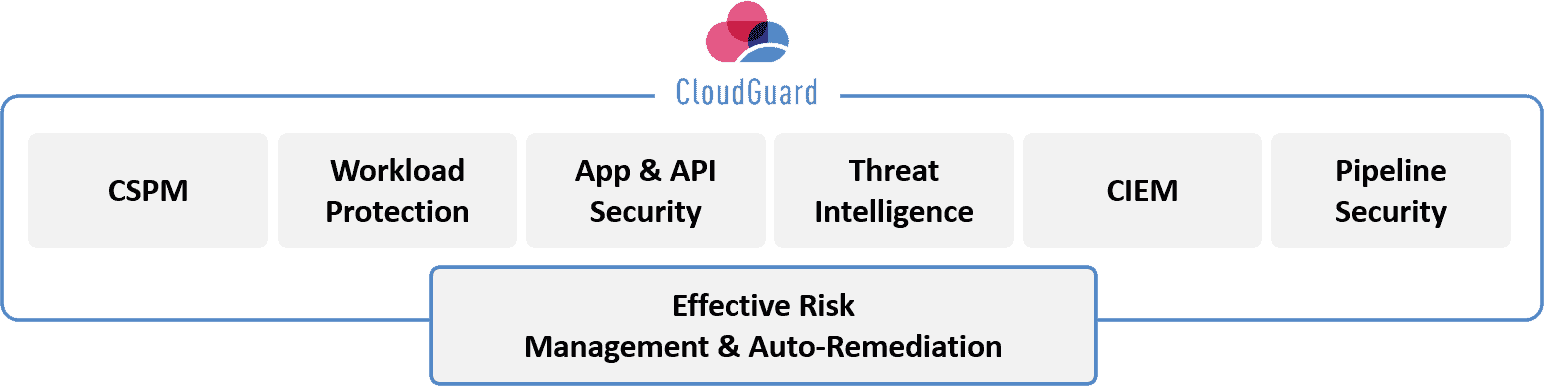
Cloud Network Infrastructure Security
Did you know that 76% of enterprises are now using two or more cloud providers? To keep up with today’s threat landscape, organizations need to further enhance the security around their cloud network—across providers. Check Point provides industry-leading advanced threat prevention and cloud network security for your public, private and hybrid-clouds, as well as efficient and consistent unified security management of clouds and on-premises networks with a single pane-of-glass
LEARN MORE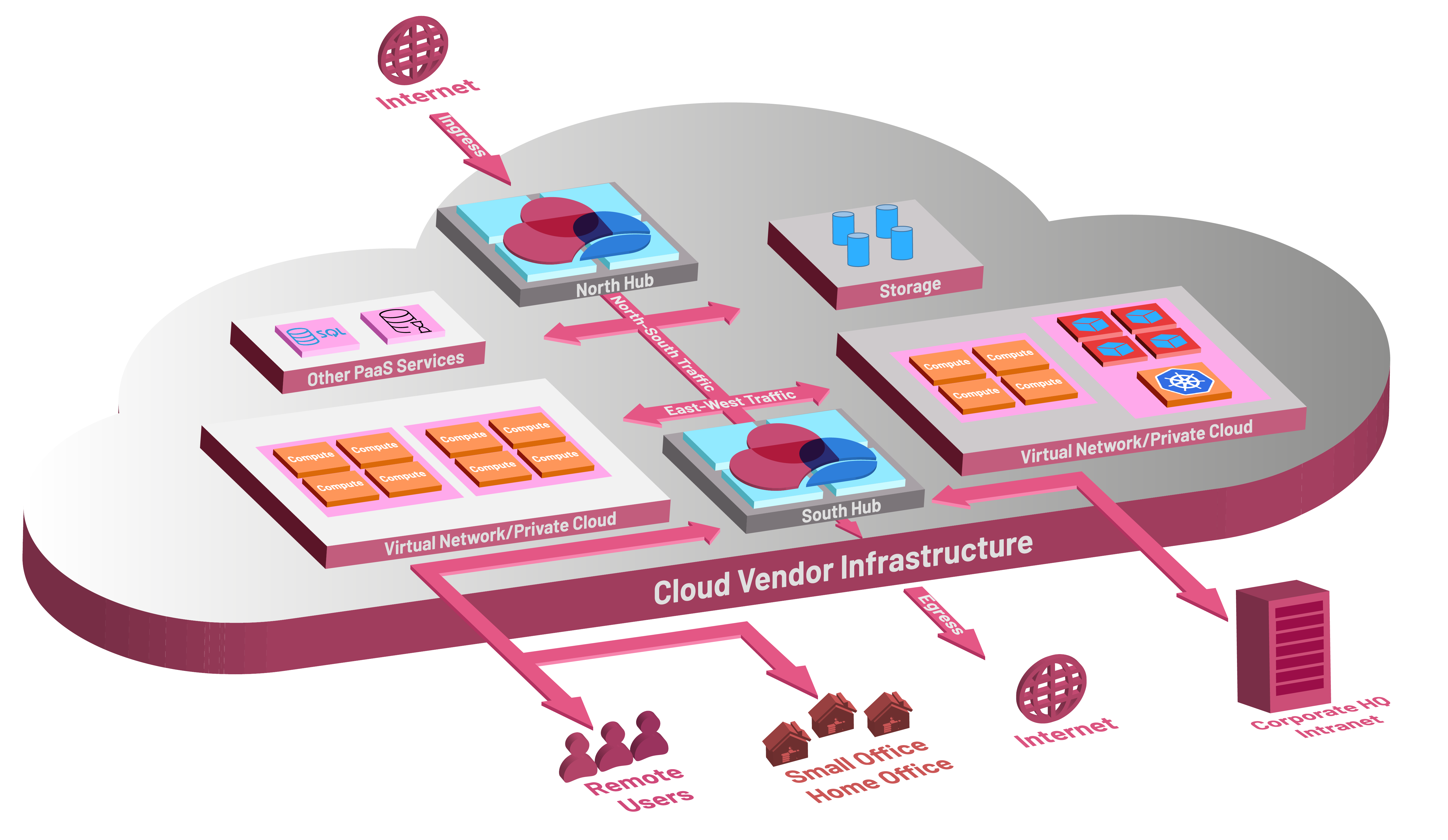
Developer Security
Monitor, classify, and protect your code, assets, and infrastructure for exposed API keys, tokens, credentials,
and high-risk security misconfigurations in a simple way, without noise. Check Point Spectral integrates with developer tools to automatically detect code vulnerabilities, identify secrets in the code before deployment, and prevents unauthorized use to nefarious ends.
Cloud Security Use Cases
![]()
Cloud Migration Security
Cloud migration can reduce costs and increase efficiency, but IT resources must remain secure. You need robust management and seamless integrations to reduce risk.
![]()
Cloud Threat Hunting
Simplify incident analysis across your configurations, posture, network traffic and identity activity. Automate ongoing intrusion detection, monitoring and threat intelligence.
![]()
DevSecOps
Deploy new applications at the speed of development, without jeopardizing your security posture. Check Point offers automated full lifecycle security for your modern day applications.
![]()
Cloud Security Compliance
Cloud infrastructure is subject to a wide variety of industry and government regulations. Leverage streamlined, automated compliance and governance across all public cloud environments.

“When deploying a multi-cloud environment, you need to have a consistent tool that plays across all the platforms. Using the cloud-agnostic Check Point service, I only need to train an individual on one set of tools and he can manage our total cloud environment very effectively.”
– Sreeni Kancharla, CIO & Sr. Group Director, Cadence
READ MORE
“We selected Check Point as it seamlessly integrated into our ever-expanding use of AWS Lambda functions and helped automate security into our serverless infrastructure. Check Point also supports us as we move forward with integrating CI/CD pipelines, allowing us to easily and continuously defend our applications.”
– Brent Bain, Lead Cloud Architect and System Engineer at Best Friends Animal Society
READ MORE
“In the new SD-WAN environment with Check Point, we can deploy a site in five minutes or less—including getting a cup of coffee in the middle of the process. It is a phenomenal solution that is quick to deploy, built on a very secure platform that we’re comfortable with.”
– David Antlitz, Global Manager, Security and Firewall Technologies, Grace
READ MORE
“Check Point has been a saving grace for Gas South. It
is the only solution that gives us secure, stable, complete access to our
critical applications and services in Azure.”
– Rajiv Thomas, Senior Systems Engineer, Gas South
READ MORECheck Point is the only fully unified cyber security architecture that future-proofs your business and IT infrastructure across all networks, cloud and mobile. The architecture is designed to resolve the complexities of growing connectivity and inefficient security. It provides complete threat prevention which seals security gaps, enables automatic, immediate threat intelligence sharing across all security environments, and consolidated security management for a powerfully, efficient security operation.
LEARN MORE