Hybrid SASE
Robust Network Security, Optimal User Experience
Get 10x faster internet security, high-performance Zero Trust access, and comprehensive SaaS Security with Check Point’s hybrid Secure Access Service Edge (SASE).
Check Point named a leader in the 2025 Gartner Magic Quadrant for Hybrid Mesh Firewalls.
Check Point SASE Boosts Network Security and User Experience
Converge network security and optimization into a single, cloud-based platform built for the modern enterprise
- Superior User Experience Securely connect users to company resources and the web without sacrificing performance
- Full-Mesh Connectivity Global any-to-any connectivity—users to resources, data center to cloud or cloud to cloud—whatever your network requires
- Reduce Operating Complexity Manage users, resource access, and the network from a single, unified cloud dashboard
Discover Stronger Security, Smarter Access
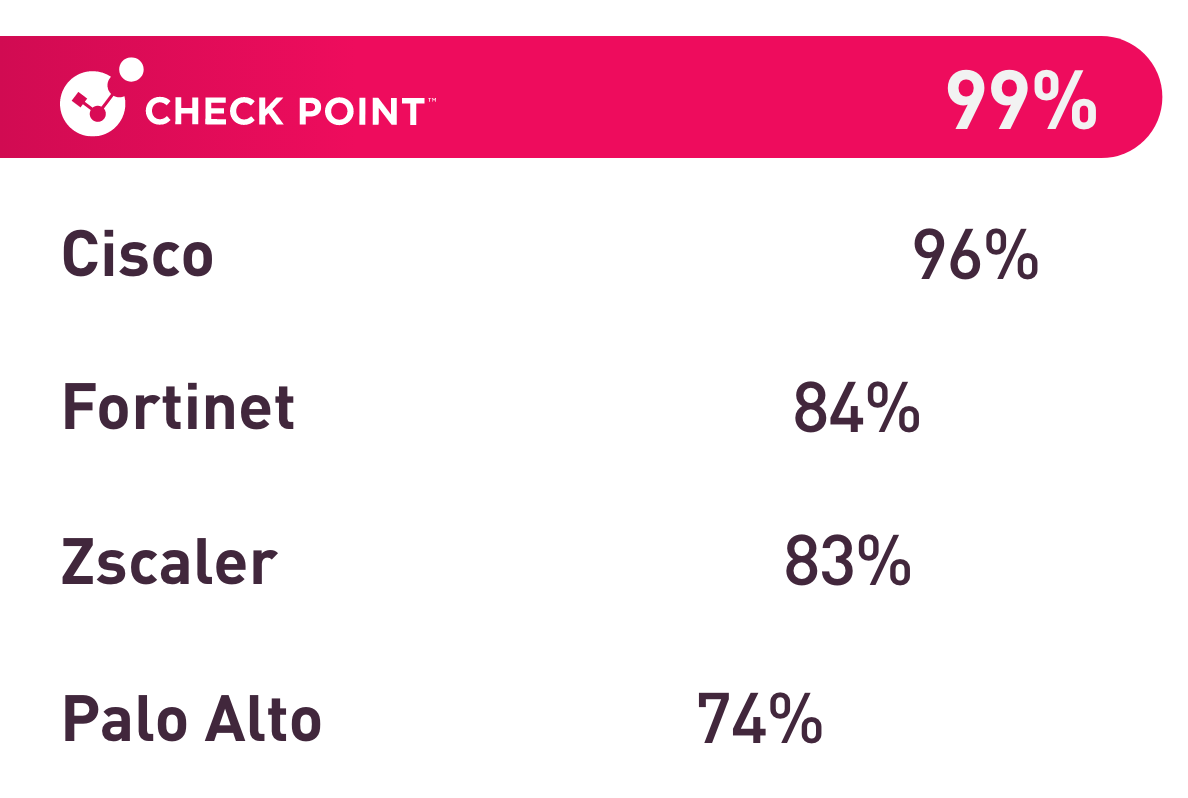
Top-Rated Threat Prevention
Check Point SASE achieved the industry’s highest threat prevention rate in Miercom’s 2025 Enterprise and Hybrid Mesh Firewall Security Report.
With a block rate of 99%, get the best protection against the latest generation of cyber attacks.
Why Check Point SASE
Single-vendor SASE solution with unmatched user and management experience
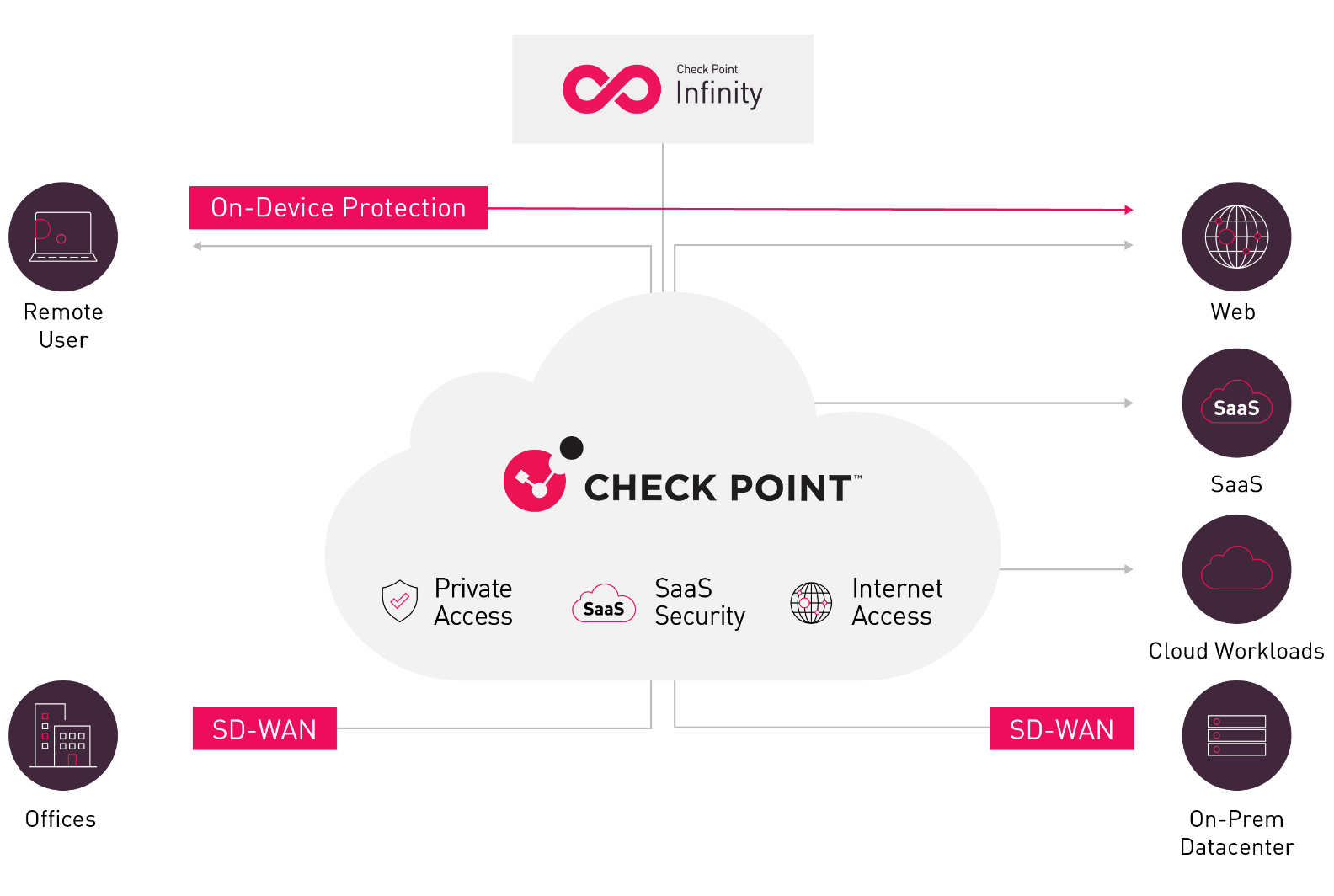
- Hybrid Internet Access Let your employees connect directly to the web without sacrificing security thanks to on-device, in-browser, and cloud protections
- Full-Mesh Private Access Granular, secure zero trust Private Access from any user or site to any user, site, or resource.
- SaaS Security End-to-end SaaS protection with inline and API-based enforcement. Application Control, tenant restrictions, AI-powered DLP, threat prevention powered by ThreatCloud AI, out-of-band scanning for data security, over-sharing remediation, shadow SaaS discovery, and posture management.
- GenAI Security Monitor prompt-level GenAI usage for secure AI adoption across the organization.
- Secure SD-WAN Optimized connectivity for over 10,000 business applications. Full suite protection with ThreatCloud AI – the industry’s most effective threat prevention technology.
Check Point SASE Suite
Discover the most complete and robust solution for securing employees and the network.

Private Access
- Applies an identity-centric zero trust access policy
- Accommodates any employee, third party or branch office
- Delivers high performance with a full mesh global private backbone
- Seamless deployment and intuitive administration

Internet Access
- 10x faster browsing thanks to on-device inspection
- Accurate localization
- Improved user privacy and compliance
- Comprehensive protections such as web and DNS filtering, malware protection and more

SaaS Security
- Inline and API-based enforcement with Application Control for 10,000+ cloud apps, tenant restrictions, DLP, and Threat Prevention powered by ThreatCloud AI
- Out-of-band API scanning protects data contained in SaaS apps
- AI-powered data classification with 800+ predefined data types
- SaaS posture management

SD-WAN
- Optimized routing for 10,000+ applications and users
- Auto-steering based on link health e.g. latency and packet loss
- Sub-second failover to any WAN link: MPLS, 5G, broadband
- Zero-touch provisioning with full branch-level security
See how Check Point SASE helps IT professionals simplify network management with seamless Zero Trust access
Why Customers Choose Check Point SASE
Explore Check Point SASE
Check Point SASE Datasheet
Discover Check Point SASE, a simpler, more robust solution for securing remote access to on-prem and cloud resources
The Essential SASE for Enterprises eBook
Secure your network with SASE for flexibility, security, and performance.
FAQs
Check Point SASE combines secure Internet Access, Zero Trust Network Access, and SaaS security into a unified platform. It delivers simplified management, full-mesh connectivity, and 10x faster internet security for your hybrid workforce.
Check Point SASE integrates advanced security services with optimized networking by merging Zero Trust Network Access, threat prevention, and SD-WAN capabilities. This ensures secure, high-performance connectivity for remote users, branches, and cloud applications.
Check Point SASE supports auto-optimized SD-WAN routing for 10,000+ apps and users with subsecond failover, and a global high-performance backbone to deliver faster, more reliable connections. It ensures secure access to applications and data while minimizing latency for remote and hybrid workforces.
Check Point SASE uses a hybrid architecture with on-device and cloud security inspection options. It can also integrate with existing on-premises infrastructure, allowing organizations to adopt SASE at their own pace.