Event Management: SmartEvent
SmartEvent event management provides full threat visibility with a single view into security risks. Take control and command the security event through real-time forensic and event investigation, compliance, and reporting. Respond to security incidents immediately and gain network true insights.
GET A FREE DEMO
![]()
Full Threat
Visibility
SmartEvent provides a single view into security risks
![]()
Real Time Forensic and Event Investigation
Take control and understand your security status and trends
![]()
Command the
Security Event
Respond to security incidents immediately and gain network true insights
Check Point Named a Leader in the 2022 Gartner® Magic Quadrant™ for Network Firewalls
GET THE REPORT
Featured Specifications

Full Threat Visibility
Utilize the power of R81 single management console – Nothing goes undetected
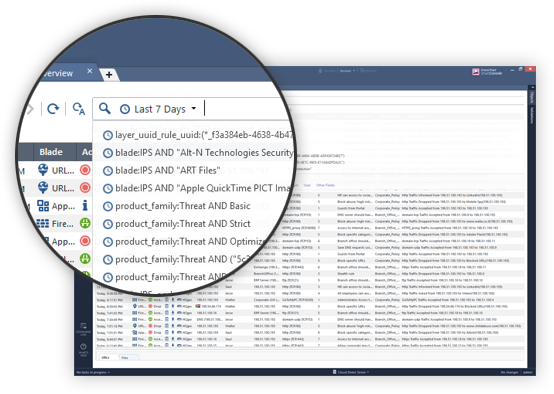
Instant Search Results
Free text search, auto suggestion and search history favorites
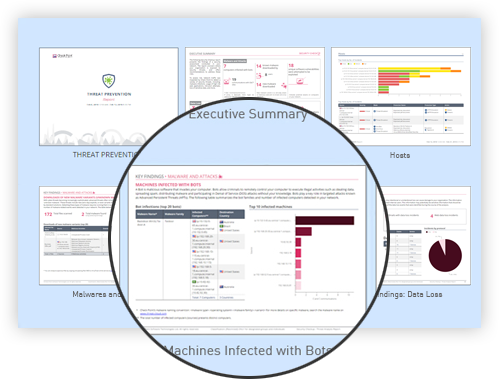
Customizable Views and Reports for Any Audience
With an intuitive dashboard, view high level graphs and pivots, and schedule periodic reports

R81 Security Management
Policy management, integrated threat management and performance all through a single pane of glass
Check Point Named a Leader in the Forrester Wave™ Enterprise Firewalls Q4 2022
SEE THE REPORT

Check Point Titan Release R81.20 WATCH WEBINAR REPLAY
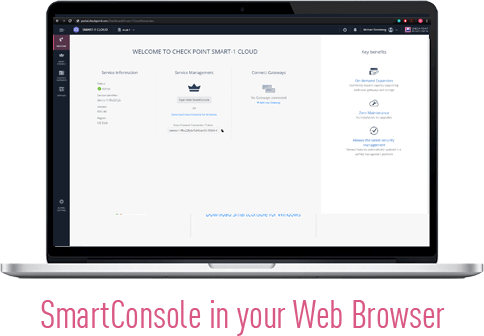
Unified Security Management Now Available as a Cloud Offering
![]()
Always the latest security management
keeps you automatically up-to-date
![]()
On-demand Expansion to seamlessly onboard more gateways
![]()
Zero Maintenance makes your environments more secure, manageable and compliant
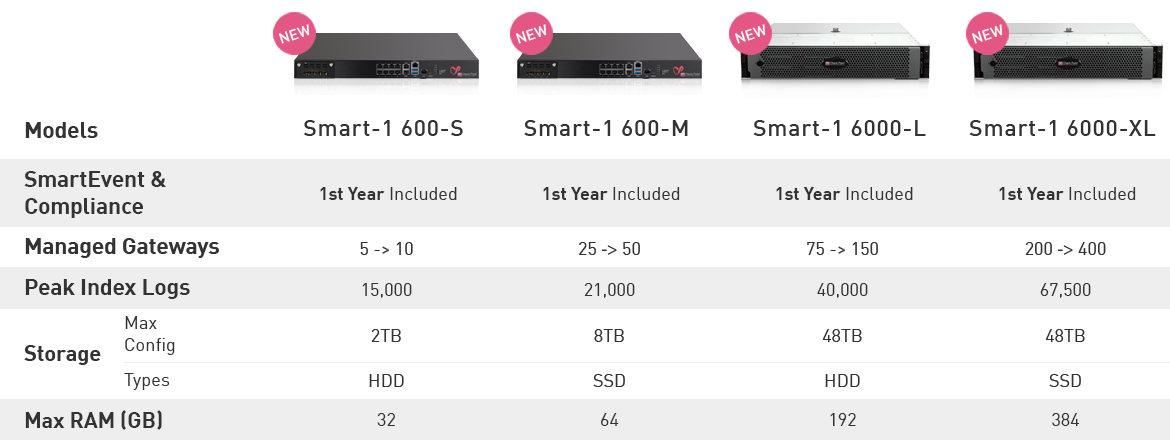
Dedicated Smart-1 Appliances with SmartEvent

“The integrated Check Point solution has increased our Cyber Security level and saves us around four hours’ work per week!”
-Christoph Andreas, IT Systems & Support Team Leader, Optimal Media
2023 Cyber Security Report
Geo-political conflicts trigger all-time high for cyberattacks.
See more trends and insights.