URL Filtering
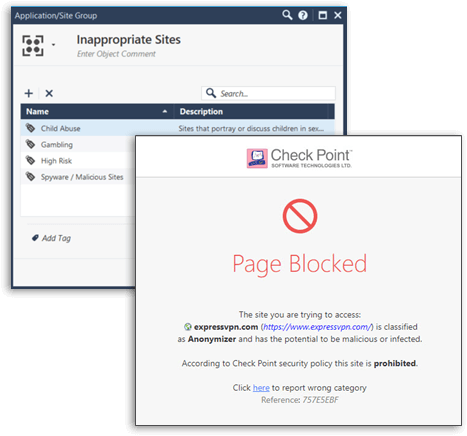
Web access is a predominant route for attacks on enterprises. Check Point URL Filtering controls access to millions of web sites by category, users, groups, and machines to protect users from malicious sites and enable safe use of the Internet. URL Filtering employs UserCheck technology, which educates users on web usage policy in real time.

![]()
Secure
Protects users with cloud-based categorization and UserCheck technology
![]()
Efficient
Enable on any Check Point security gateway reducing Total Cost of Ownership
![]()
Unified
Unified security across all aspects of the web with full Application Control integration
Product Specifications
Extensive and Dynamic URL Coverage
URL Filtering provides organizations with the ability to dynamically allow, block or limit access to certain websites in real-time. URL Filtering can control access to entire websites or just pages within a website, with fine-tuning policies incorporated to white list and black list specific URLs.
Inspect SSL/TLS Encrypted Traffic
Equipped with Check Point’s SSL inspection technology, Application Control scans and secures SSL/TLS encrypted traffic passing through the gateway. Organizations can granularly define exceptions for SSL/TLS inspection to protect user privacy and comply with corporate policy.
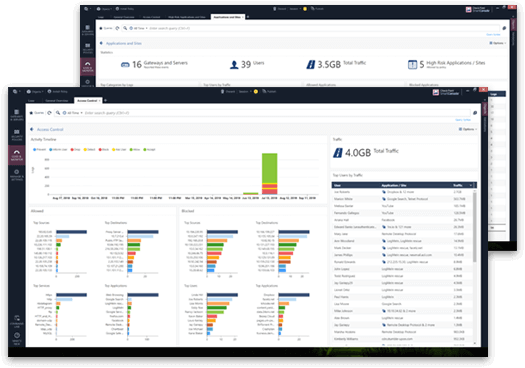
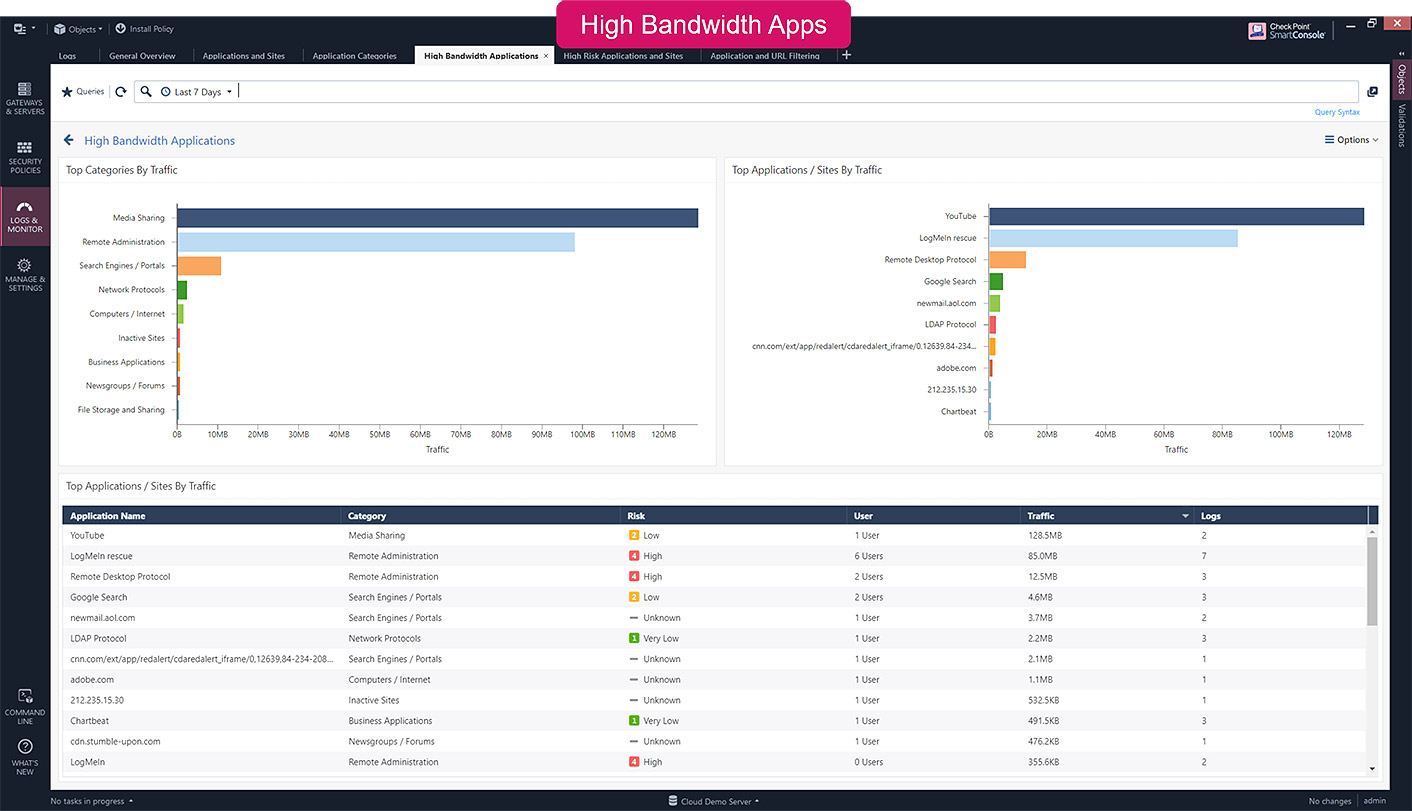
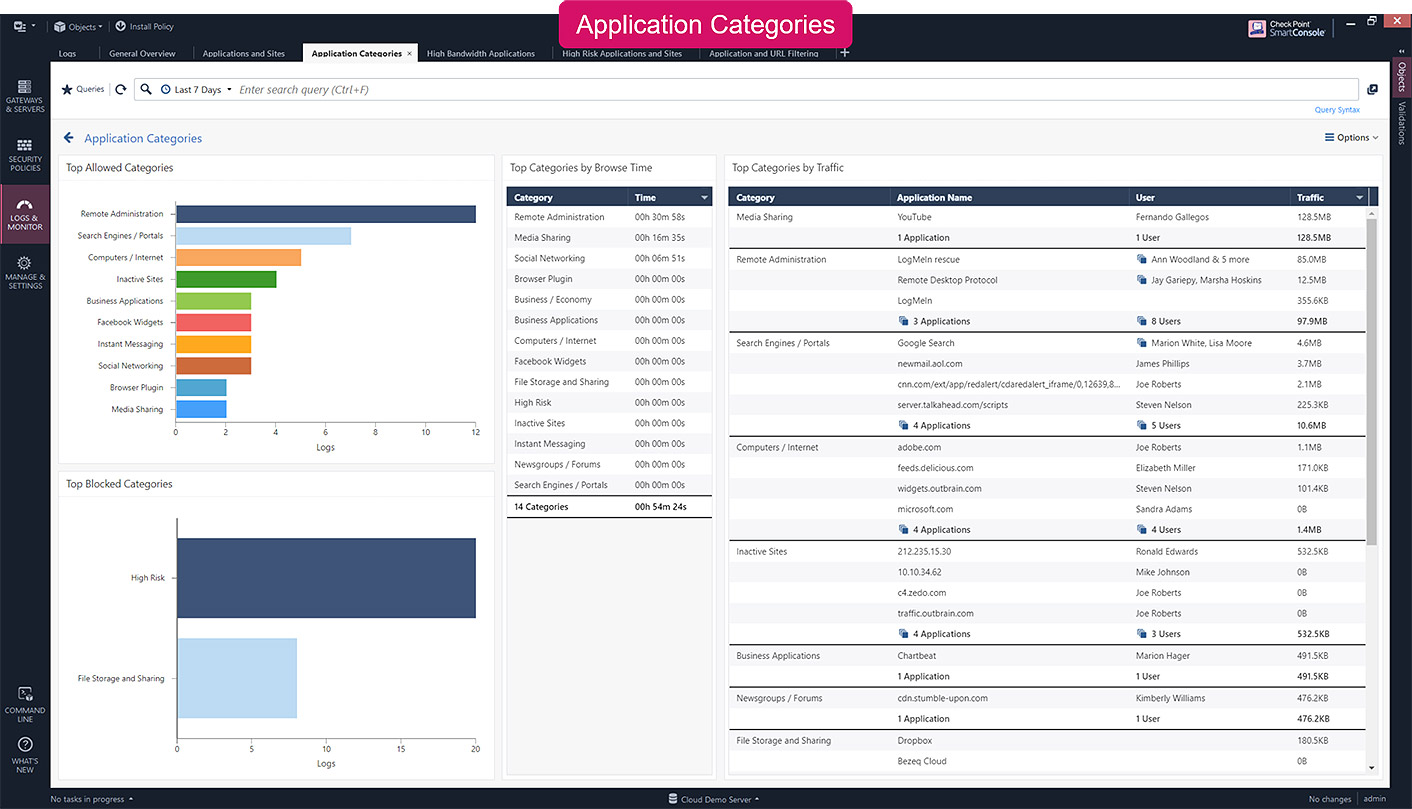
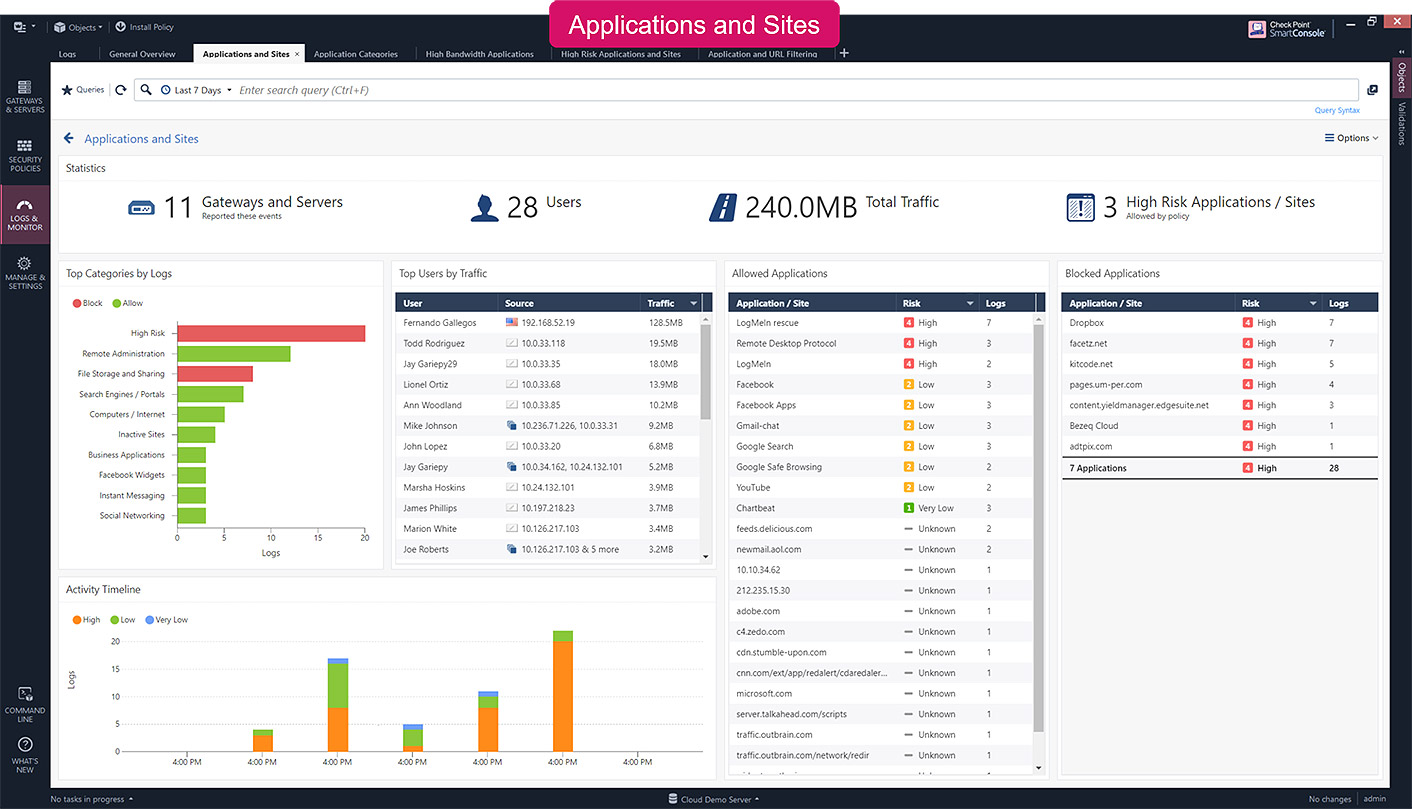
360° Visibility and Reporting
Achieve an unmatched level of visibility to detect web access security events and prevent them. Check Point URL Filtering seamlessly integrates with SmartEvent, enabling Check Point to prevent web access related security events rather than just detecting them or simply missing them.
A Next Generation Firewall for Any Deployment
Consolidated Firewall Logging and Actionable Reporting
Implement Zero Trust Security
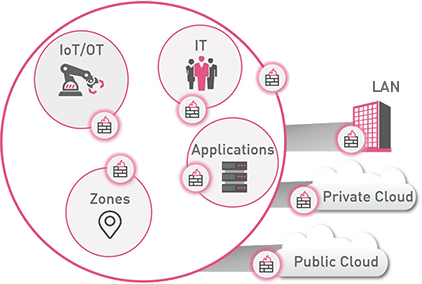
Zero Trust security is about having the ability to “Divide and Rule” your network in order to reduce the risk of lateral movement. Check Point NGFWs enable you to create granular network segmentation across public/private cloud and LAN environments. With detailed visibility into the users, groups, applications, machines and connection types on your network, they allow you to set and enforce a “Least Privileged” access policy. So, only the right users and devices can access your protected assets.
2023 Cyber Security Report
Geo-political conflicts trigger all-time high for cyberattacks.
See more trends and insights.