Featured Technology Partner Solutions
Technology partners, system integrators and DevOps can use our open APIs to integrate with the Check Point cyber security architecture across networks, endpoint, cloud and mobile to protect businesses from sophisticated cyber-attacks.
Check Point Cloud Security
Check Point integrates with leading public cloud vendors to protect data in the cloud, reduce risk and achieve compliance. Using Check Point Posture Management, organizations can visualize and assess their security posture, detect misconfigurations, model and actively enforce security best practices, and protect against identity theft and data loss in the cloud. Check Point Posture Management delivers security capabilities across Amazon Web Services, Microsoft Azure, and Google Cloud Platform (GCP).
Check Point and IAM
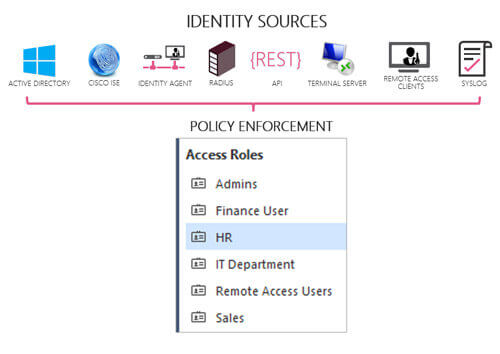
Every IT organization can greatly enhance their security posture and increase the overall value of their network security deployment with contextual identity-based metadata.
Check Point Identity Awareness and the Check Point Controller included in Check Point Next Generation security platforms collects data from multiple identity sources.
This information can then be used across the Check Point ecosystem, on premise and in the cloud, to provide better visibility and network security.


Check Point and UEM
Mobile devices are the backdoor to network breaches, exposing sensitive corporate data to risk.
Check Point’s Check Point Mobile Security is a leading enterprise mobile security and mobile threat defense (MTD) solution. Protecting your business from advanced, fifth-generation cyber attacks has never been easier.
When paired with market-leading UEM solutions, Check Point Mobile Security adds a critical security layer to enhance enterprise mobile security that can be used to dynamically change access privileges to reflect risk levels and keep assets and sensitive data secure.
FIND A PARTNERCheck Point and SD-WAN
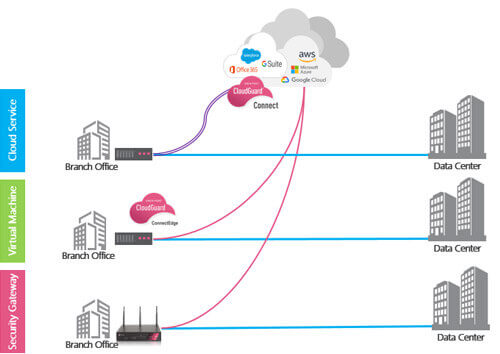
As enterprises increasingly move their on-premises branch office workloads and applications to SaaS applications, they are adopting Software Defined Wide Area Networking (SD-WAN) to intelligently route traffic to cloud services.
However, connecting branch offices directly to the cloud significantly increases their security risk and security management costs.
The Workspace Security Connect service and Check Point Edge virtual machine (VM) integrate with network management and orchestration systems to secure any organization with remote branch offices in minutes.
Check Point and SIEM/SOAR
Check Point offers a fully consolidated cyber security architecture to protect your business and IT infrastructure against sophisticated cyber-attacks across networks, endpoint, cloud and mobile.
Any security infrastructure likely requires additional products and data sources. Check Point network, endpoint, cloud and mobile device events enrich the data that SIEM vendors then analyze for threats.
Check Point and SOAR solutions goes a step beyond event correlation and analysis. Incidents from Check Point and other devices fed into SOAR can generate new threat indicators for malware, threat behavior and network addresses associated with each identified attack.
*Siemplify SOAR is available for purchase directly from Check Point