Infinity-Vision Unified Security Management
Achieve the gold standard in cyber security with the unified security management delivered by Infinity-Vision. Ensure that your organization can prevent breaches and manage your entire security environment with unified policies from a single pane of glass across networks, cloud, mobile, endpoint and IoT device. Detect, respond, and shut down attacks faster with 99.9% precision using the same SOC tools developed by Check Point Research for their cyber attack investigations.
SECURITY CHECKUP![]()
Threat Intelligence
Powers Infinity
Real-time threat intelligence enriched by AI engines detects and blocks thousands of attacks daily
![]()
Unified Management Across Environments
Centrally control policy management, monitoring and response for every attack surface
![]()
Achieve SOC
Certainty
Expose and shut down attacks faster with 99.9% precision across your environment
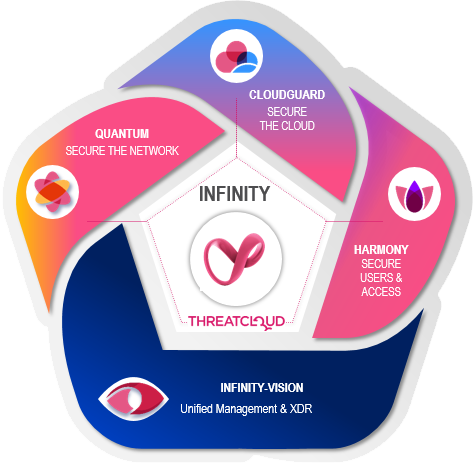
Infinity-Vision Powers the Infinity Architecture
Infinity-Vision is the unified management platform for Check Point Infinity, the first modern, consolidated cyber security architecture built to prevent today’s most sophisticated attacks across networks, cloud, endpoints, mobile and IoT. Powered by the world’s largest threat intelligence network, Infinity-Vision centrally manages the Infinity architecture to mitigate attacks effectively in real time, solves security gaps, and reduces total cost of ownership.
LEARN MOREShared Threat Intelligence Powers Infinity-Vision
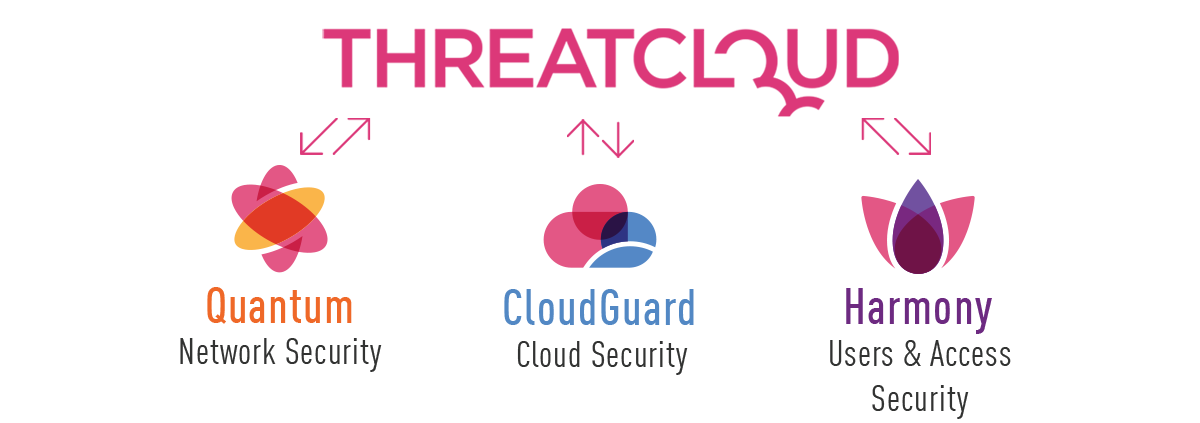
ThreatCloud AI translates threat intelligence data from hundreds of millions of sensors worldwide into proactive security protections across the Infinity architecture.
Unified Management Across Environments
Infinity-Vision consolidates management of multiple security layers, providing superior policy efficiency and enabling teams to manage the security of the entire enterprise through a single pane of glass.
Investigate And Block Only Real Attacks
Horizon SOC exposes and shuts down attacks faster with 99.9% precision. Easily deployed and managed through the Infinity Portal cloud-based platform, Horizon SOC increases security operations efficiency and ROI.
LEARN MORE
Ready to Consolidate Your Security Architecture?
Try it Now
How it Works
Get Pricing
2021 Cyber Security Report
Learn about latest emerging threats, malware trends and cyber security recommendations
DOWNLOAD FULL REPORT
Additional Resources
Downloads
Data Sheet: Check Point Infinity
White Paper: 2021 Security Trends and Enterprise Challenges
Infographic: Cutting Complexity to Strengthen Cyber Security
Solution Brief: Check Point Infinity